Replying to @nvk, @RyanTheGentry, @moneyball, @roasbeef and @niftynei
One of the speakers at the next #SiliconSalon will be taking about VLS (Validated Lightning signer) https://siliconsalon2.eventbrite.com
Sat Sep 03 17:50:49 +0000 2022
Another centralization problem - hosting email services. What used to be one of the most decentralized of internet services as it allowed for self-hosting, it has effectively become impossible to host yourself anymore. https://twitter.com/cfenollosa/status/1566484145446027265
Tue Sep 06 14:41:23 +0000 2022
Replying to @cronokirby
There is a discussion about designing for user sovereignty over hardware in the next #SiliconSalon (next Wednesday at 9am PDT). Too often you are effectively leasing your hardware, as they are brickable by manufacturers or chip makers. https://siliconsalon2.eventbrite.com
Tue Sep 06 19:17:00 +0000 2022
We’ve talked about the chip, but how important is the supply chain for the rest of the board? [4/10] https://twitter.com/ChristopherA/status/1275143980389265408?s=20&t=8Mo2bi6HjDqK6e-2JEwHrQ
Tue Sep 06 22:05:34 +0000 2022
This Second Silicon Salon will be concentrating on some of the foundational issues that are critical to hardware security. https://xkcd.com/2347/
Tue Sep 06 22:05:34 +0000 2022
Generally, each #SiliconSalon will discuss the interaction between the field of cryptography & opportunities offered by semiconductor manufacturers, but there are many different topic areas. We’re going to be looking at some of them next week! [2/10] https://www.siliconsalon.info/
Tue Sep 06 22:05:34 +0000 2022
There is still room to sign up for our 2nd #SiliconSalon on September 14th. This next salon will focus on issues of secure boot, supply-chain security, and firmware upgrades, in particular for use by cryptocurrency and identity wallets. [1/10] https://www.eventbrite.com/e/silicon-salon-2-tickets-403779845387
Tue Sep 06 22:05:34 +0000 2022
There’s also the possibility of self-sovereign hardware. Can we take total control of firmware from a vendor, and what does that ultimately mean? [8/10]
Tue Sep 06 22:05:35 +0000 2022
Moving forward in time brings us to the question of upgrades: how can we continue to trust hardware following firmware updates? [7/10]
Tue Sep 06 22:05:35 +0000 2022
Are we thinking about which components actually need to be run by the SE (Secure Enclave) vs the flexibility offered by the more powerful MCU? [6/10]
Tue Sep 06 22:05:35 +0000 2022
Are we thinking about input attacks where a PIN might be captured or output attacks where an incorrect address might be shown? [5/10]
Tue Sep 06 22:05:35 +0000 2022
See our archives of the first #SiliconSalon for some of the in-depth discussions and presentations you can expect to participate in this time. [10/10] https://www.siliconsalon.info/salon1/
Tue Sep 06 22:05:36 +0000 2022
This is just the beginning of our #SiliconSalon events. We’ve got many more interesting topics to talk about! We hope you’ll join us next week for secure boot, supply-chain security, and firmware upgrades. September 14th: 9am PT. [9/10] https://www.eventbrite.com/e/silicon-salon-2-tickets-403779845387
Tue Sep 06 22:05:36 +0000 2022
@Riscure you might be interested in participating in our next #SiliconSalon https://twitter.com/ChristopherA/status/1567272822795567104
Tue Sep 06 22:11:53 +0000 2022
Envelopes are a new “smart document” functionality, part of the Gordian Architecture led by Blockchain Commons. Here we discuss some of our design choices for how they should be initially implemented, as well as some opinionated cryptographic choices. https://youtu.be/S0deyIHXukk
Fri Sep 09 18:15:01 +0000 2022
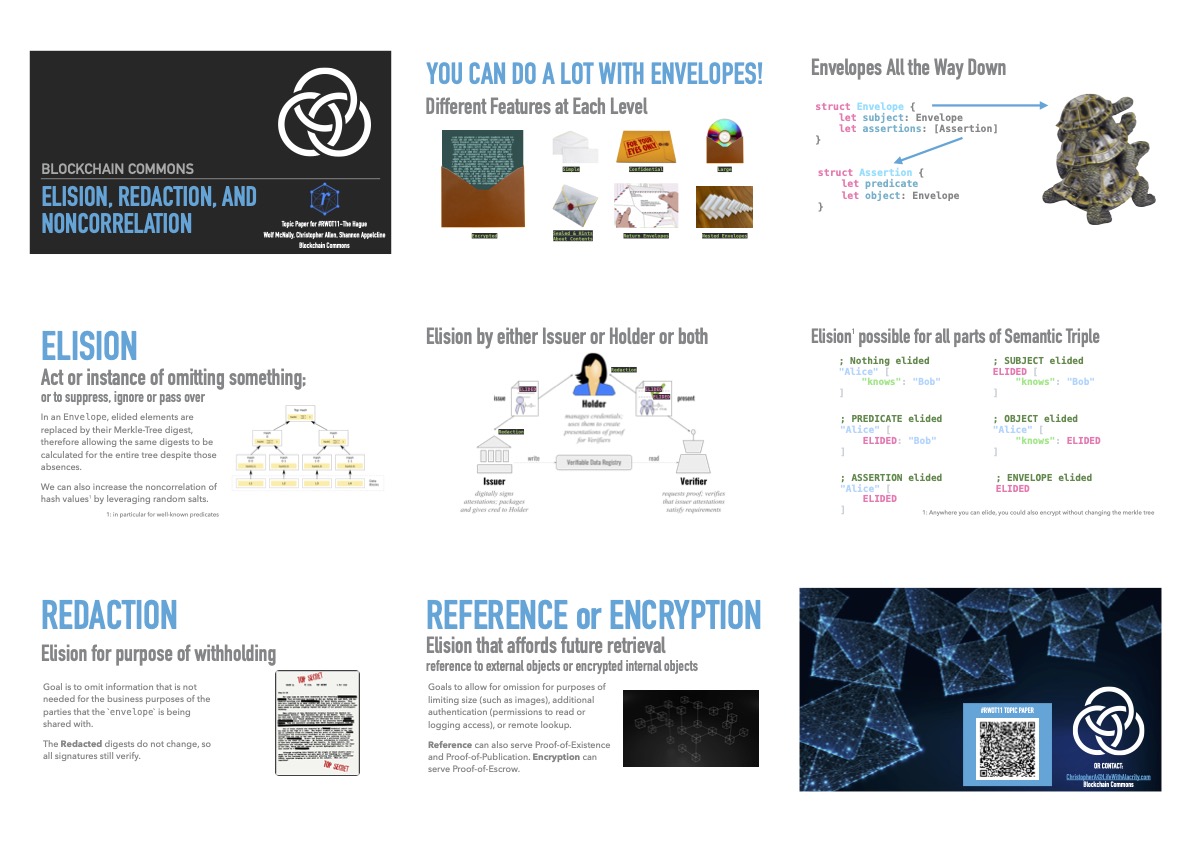
A presentation on the privacy requirements for envelopes in our Gordian Architecture, in particular, to address issues of correlation to allow for elision, redaction & external reference by both issuers & holders. https://youtu.be/ubqKJAizayU
Fri Sep 09 19:37:15 +0000 2022
RT @WolfMcNally: I’m very proud of this work I’ve been doing with @BlockchainComns and @ChristopherA .
Fri Sep 09 19:38:38 +0000 2022
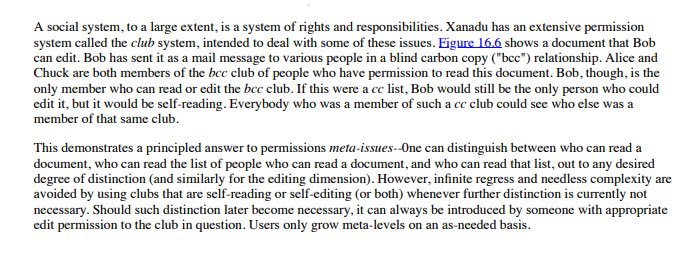
One of the projects that I want to build on top of this Gordian Architecture is a Xanadu-style “Club System” with cryptographic ocaps, like what I described to @marksammiller of @agoric in mid-90s. Think decentralized git for encyclopedia-sized collaboration. Finally is possible! https://twitter.com/ChristopherA/status/1568322661494960129
Fri Sep 09 21:50:03 +0000 2022
RT @ChristopherA: There is still room to sign up for our 2nd #SiliconSalon on September 14th. This next salon will focus on issues of secur…
Mon Sep 12 18:55:07 +0000 2022
Replying to @typedfemale
That was my experience with classical training on flute. I wish instead I’d focused on a more improvisational instrument. I eventually did (the handpan) after years of giving up on flute, and have discovered I can now enjoy improv on flute now. Maybe learn to fiddle?
Tue Sep 13 02:08:36 +0000 2022
I’ve had numerous reports of the twitter account @ChristophbeA impersonating me and chatting up people, presumably for a con. I am blocked by them, so can’t see what they are doing. I have reported to Twitter, but if they have spoken to you, please report them.
Tue Sep 13 17:32:51 +0000 2022
If you’ve been following our Gordian Architecture efforts, and our particular focus on the creation of cryptographic envelopes to support requirements for non-correlation, privacy, security, elision, redaction, etc., we’ve made progress on our CLI app: https://youtu.be/JowheoEIGmE
Tue Sep 13 20:22:41 +0000 2022
RT @FOUNDATIONdvcs: Bitcoin is a bearer asset and by taking self-custody it becomes unconfiscatable.
The same can’t be said for the dollar…
Tue Sep 13 21:21:39 +0000 2022
RT @Sheldrake: @owocki Hi Kevin, I love this stack with one major caveat.
I’ve attempted to communicate that caveat in your style (with my…
Wed Sep 14 19:24:08 +0000 2022
Replying to @cronokirby
I’m personally interested more in STARKs as the trusted setup issues are big. But there are also questions of where optimizations like bulletproofs, or recursive bulletproofs for curve proofs (see 🧵) are more optimal than both. https://twitter.com/ChristopherA/status/1500183510396530691
Wed Sep 14 19:31:08 +0000 2022
RT @srinathtv: An overview of Nova by @abhiramko: https://youtu.be/Jj19k2AXH2k (to be presented at @IACRcrypto 2022). Nova is a super fast recur…
Wed Sep 14 22:41:30 +0000 2022
I’ve been wondering about some of the claims of SNARKs having 80 bits of security was equivalent to what that means elsewhere. This thread (and article behind it) explores this. My summary is it likely isn’t good enough for long. https://twitter.com/SuccinctJT/status/1570089357796581381
Wed Sep 14 23:17:03 +0000 2022
We had discussion this morning during #SiliconSalon 2 about offering more zk-proof mechanisms (and accelerators) in silicon. Nova was pointed out to me as worth investigating. https://twitter.com/srinathtv/status/1558209563404316673
Wed Sep 14 23:53:32 +0000 2022
Wed Sep 14 23:54:03 +0000 2022
A topic that came up during our #SiliconSalon 2 this morning (on boot, firmware & supply chain security) is is there some way to do some kind of verifiable computational proof for initialization of firmware on a low-performance chip? https://en.m.wikipedia.org/wiki/Verifiable_computing
Thu Sep 15 00:13:50 +0000 2022
Right now most verifiable computation approaches leverage homomorphic techniques, which are terribly inefficient. But as really we just need to verify that one signature was properly evaluated by the code, maybe there is some alternative way?
Thu Sep 15 00:25:35 +0000 2022
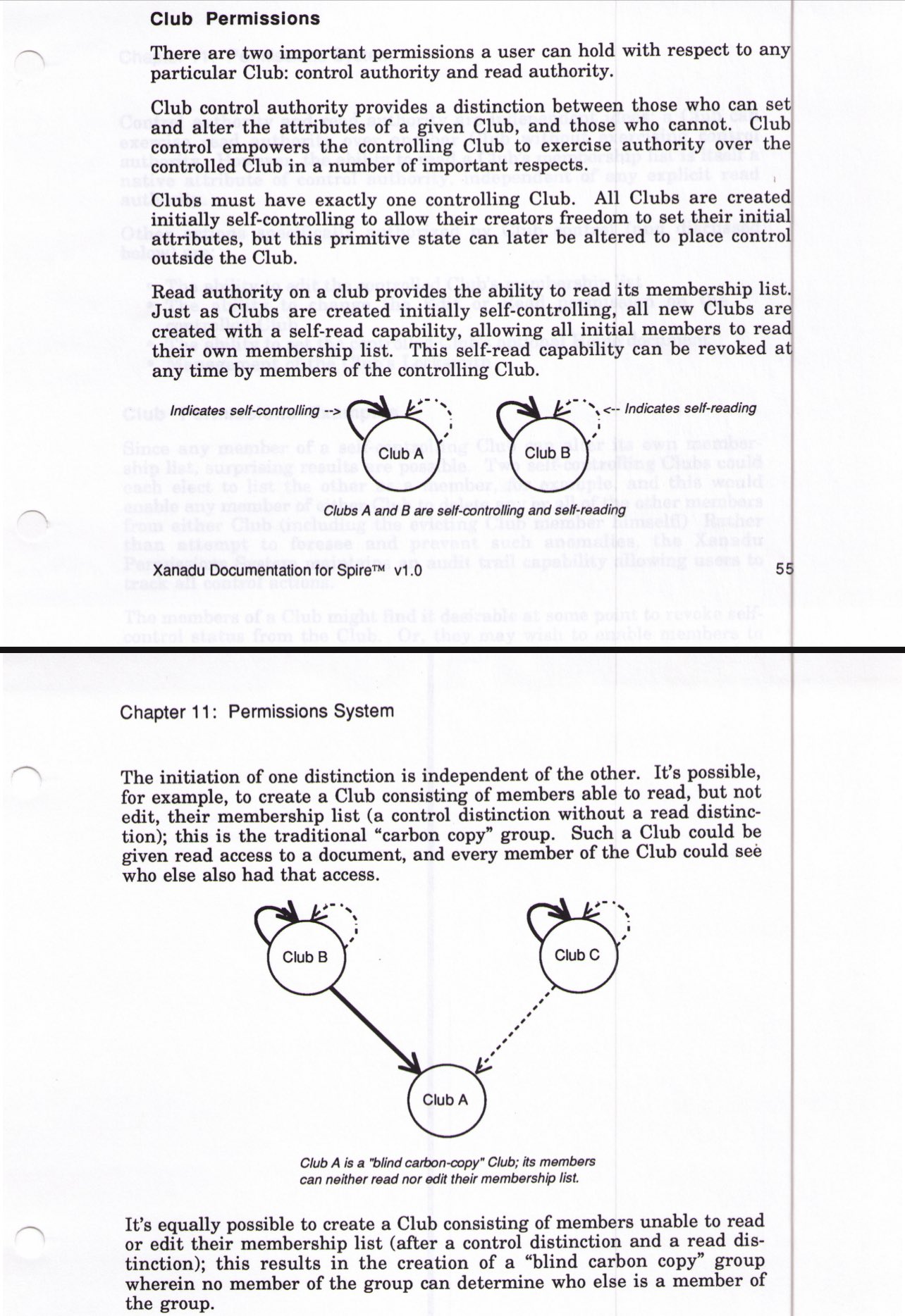
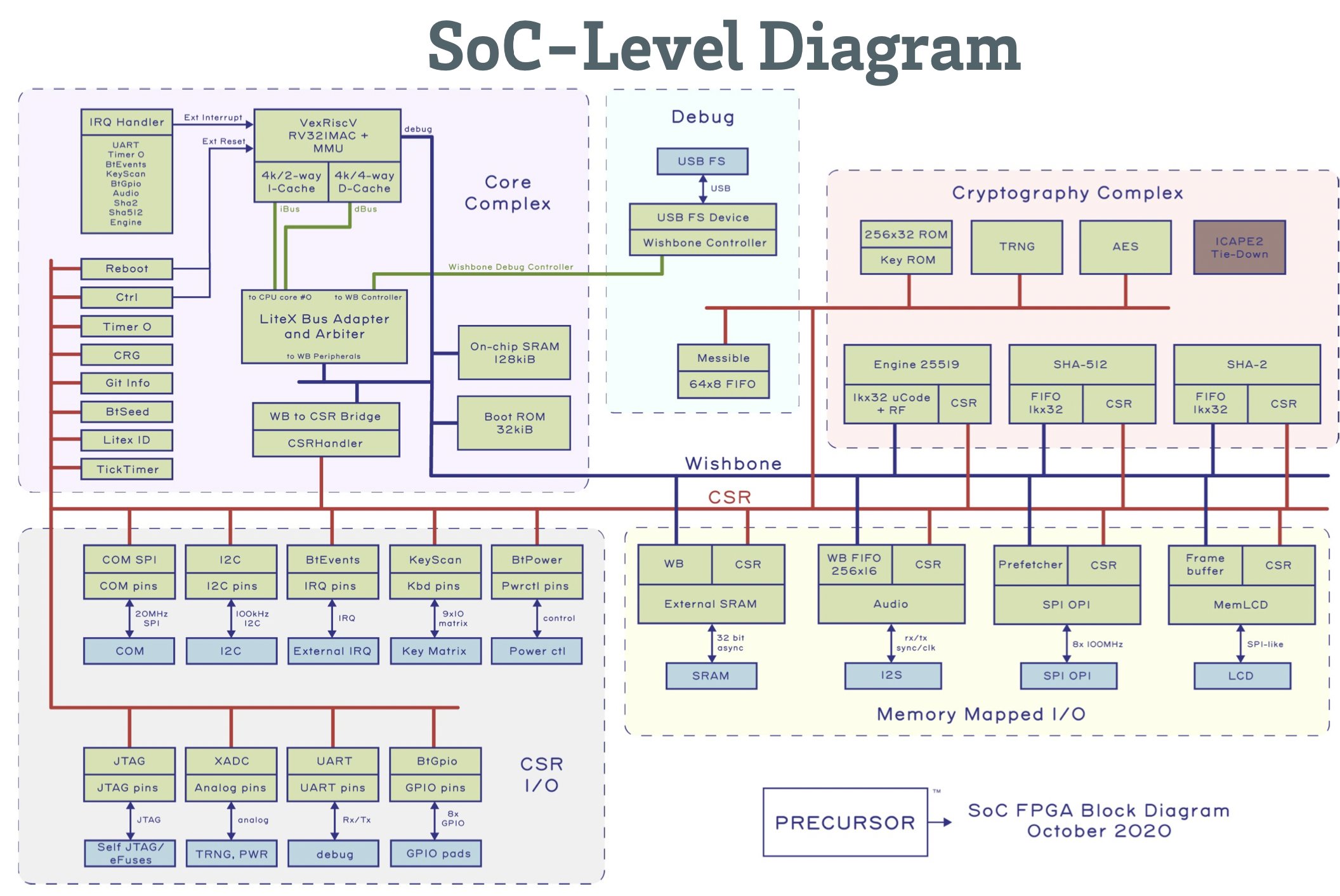
The focus of this second #SiliconSalon was on “Secure Boot, Supply-Chain Security, and Firmware Upgrades”. Our presenters this time included @BunnieLabs , @CrossBarInc new Cramium Labs, @FOUNDATIONdvcs, @Proxy, and the L2 @VLSProject. [3/10] https://www.siliconsalon.info/salon2/presentations/
Mon Sep 19 17:02:10 +0000 2022
Currently, no semiconductor chips are available specifically for cryptographic wallets, leaving developers to cobble together solutions. The object of the #SiliconSalon is to bring together people from blockchain & semiconductor communities to plan next-generation chips. [2/10]
Mon Sep 19 17:02:10 +0000 2022
The second #SiliconSalon organized & facilitated by @BlockchainComns was this Wednesday. The focus was on “Secure Boot, Supply-Chain Security & Firmware Upgrades” for cryptographic hardware. You can now read all about it & view the presentations: [1/10] https://www.siliconsalon.info/salon2
Mon Sep 19 17:02:10 +0000 2022
And if you missed the first Silicon Salon, which provided an overview of the topic, we’ve collected all of the info from that event as well. [7/10] https://www.siliconsalon.info/salon1
Mon Sep 19 17:02:11 +0000 2022
We had lively Q&A on the presentations as well as some open discussions on all three topics. Take a look at our website for key quotes on boot, firmware, and supply chains. [6/10] https://www.siliconsalon.info/salon2
Mon Sep 19 17:02:11 +0000 2022
If you’d like, you can also watch all the presentation videos on our YouTube channel. [5/10] https://www.youtube.com/playlist?list=PLCkrqxOY1FbqacMfq755GNWs2sTmJpMHF
Mon Sep 19 17:02:11 +0000 2022
The presentations offered a lot of depth on how people currently overcome these challenges. There’s a lot more to working with semiconductors than just the chip itself! Our web pages include slide shows and transcripts from the presentations. [4/10] https://www.siliconsalon.info/salon2/presentations
Mon Sep 19 17:02:11 +0000 2022
If you feel this sort of work is important, please consider becoming a sponsor of @BlockchainComns on GitHub. At the sustaining sponsor level, you can help plan these events and guide our other priorities. [10/10] https://github.com/sponsors/BlockchainCommons
Mon Sep 19 17:02:12 +0000 2022
Thanks to all of our participants! They’re the ones that make #SiliconSalon work, since they’re all about bringing multiple parties together into a Commons.[9/10]
Mon Sep 19 17:02:12 +0000 2022
We are considering “Hardware Cryptographic Acceleration” as a possible topic for our third #SiliconSalon, either in late Fall or Winter, depending on how the holidays affect everyone! [8/10]
Mon Sep 19 17:02:12 +0000 2022
Replying to @mullvadnet
We’d love to have a presentation & Q&A about @Mullvadnet’s Tillitis device in an upcoming #SiliconSalon. From your GitHub you are using FPGA? @bunniestudios offered a presentation leveraging FPGA at our last event: https://twitter.com/ChristopherA/status/1571907511732797440?s=20&t=YroPVpXyYx8LZPu5L94umw
Mon Sep 19 19:30:28 +0000 2022
RT @ChristopherA: @mullvadnet We’d love to have a presentation & Q&A about @Mullvadnet’s Tillitis device in an upcoming #SiliconSalon. From…
Mon Sep 19 19:30:50 +0000 2022
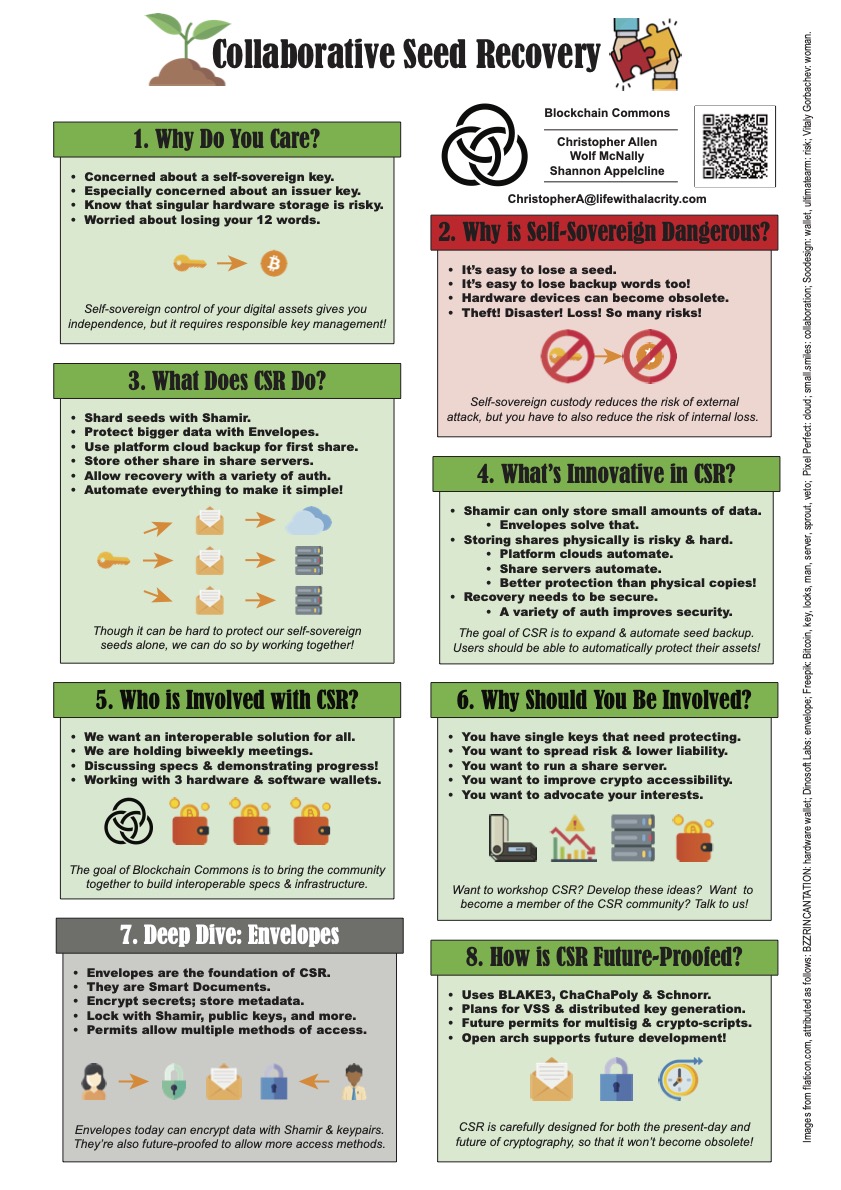
The first paper is on Collaborative Seed Recovery, our next-generation way to ensure that your self-sovereign assets can be recovered even if you lose a key. Here’s our paper on that. [3/8] https://github.com/WebOfTrustInfo/rwot11-the-hague/blob/master/advance-readings/collaborative-seed-recovery-csr.md
Tue Sep 20 18:01:20 +0000 2022
I’m bringing two @BlockchainComns papers with me to spark new discussions and hopefully move forward with the technology of self-sovereign digital identity, data, and other assets. [2/8]
Tue Sep 20 18:01:20 +0000 2022
I am off this week to #RWOT11, the #RebootingWebOfTrust design workshop, this time in The Hague. I founded it in 2015 with leaders from the Bitcoin (@VitalikButerin) & Ethereum communities, and since we incubated the DID spec, now a W3C standard. [1/8] https://github.com/WebOfTrustInfo/rwot11-the-hague
Tue Sep 20 18:01:20 +0000 2022
We have begun building a reference CLI (command-line interface) called envelope to demonstrate these privacy features. A multi-video playlist introducing it is available at https://www.youtube.com/playlist?list=PLCkrqxOY1FbooYwJ7ZhpJ_QQk8Az1aCnG [7/9]
Tue Sep 20 18:01:21 +0000 2022
Here’s a briefer poster on Elision, Redaction, and Noncorrelation in our Envelopes. [6/8] https://github.com/WebOfTrustInfo/rwot11-the-hague/blob/master/advance-readings/posters/elision-redaction-correlation-smart-documents-poster.pdf
Tue Sep 20 18:01:21 +0000 2022
The second paper discusses how our new Envelope structure supports elision of data even if you are not the issuer, which we think is a big advance. Here’s that paper: [5/8] https://github.com/WebOfTrustInfo/rwot11-the-hague/blob/master/advance-readings/elision-redaction-correlation-smart-documents.md
Tue Sep 20 18:01:21 +0000 2022
We’ve also produced a poster on Collaborative Seed Recovery if you prefer a shorter intro. [4/8] https://github.com/WebOfTrustInfo/rwot11-the-hague/blob/master/advance-readings/posters/collaborative-seed-recovery-csr-poster.pdf
Tue Sep 20 18:01:21 +0000 2022
We’re looking forward to seeing old friends and new faces alike at RWOT11! Given Covid it has been a long three years since we met F2F! If you are interested in joining us last minute, tickets are available through Friday. [8/8] https://rwot11.eventbrite.com
Tue Sep 20 18:01:22 +0000 2022
News just in—The #Wyoming Legislative Select Commitee on Blockchain reviewed my bill to offer special protection of private keys against disclosure: https://wyoleg.gov/InterimCommittee/2022/S19-2022091923LSO-0058v0.5.pdf. The bill passed the committee, allowing the bill will be forwarded onward! Hopefully a law in early 2023! https://twitter.com/ChristopherA/status/1558146722542469121
Tue Sep 20 22:36:58 +0000 2022
I’m reading through the #RebootingWebOfTrust advance readings for next week in The Hague. Unlike other workshops, we ask participants to share short papers beforehand to get a “sense of the community”. Interested in #DecentralizedIdentity? Take a look! https://github.com/WebOfTrustInfo/rwot11-the-hague/tree/master/advance-readings
Fri Sep 23 09:09:06 +0000 2022
RT @FOUNDATIONdvcs: Do you want to learn more about the Passport #bitcoin hardware wallet? Our CTO @KenOfFoundation outlined the Passport b…
Fri Sep 23 09:11:41 +0000 2022
RT @AnimoSolutions: At #RWOT University Day @ChristopherA opens with a presentation on the ideology and architecture of self-sovereign iden…
Mon Sep 26 12:27:41 +0000 2022
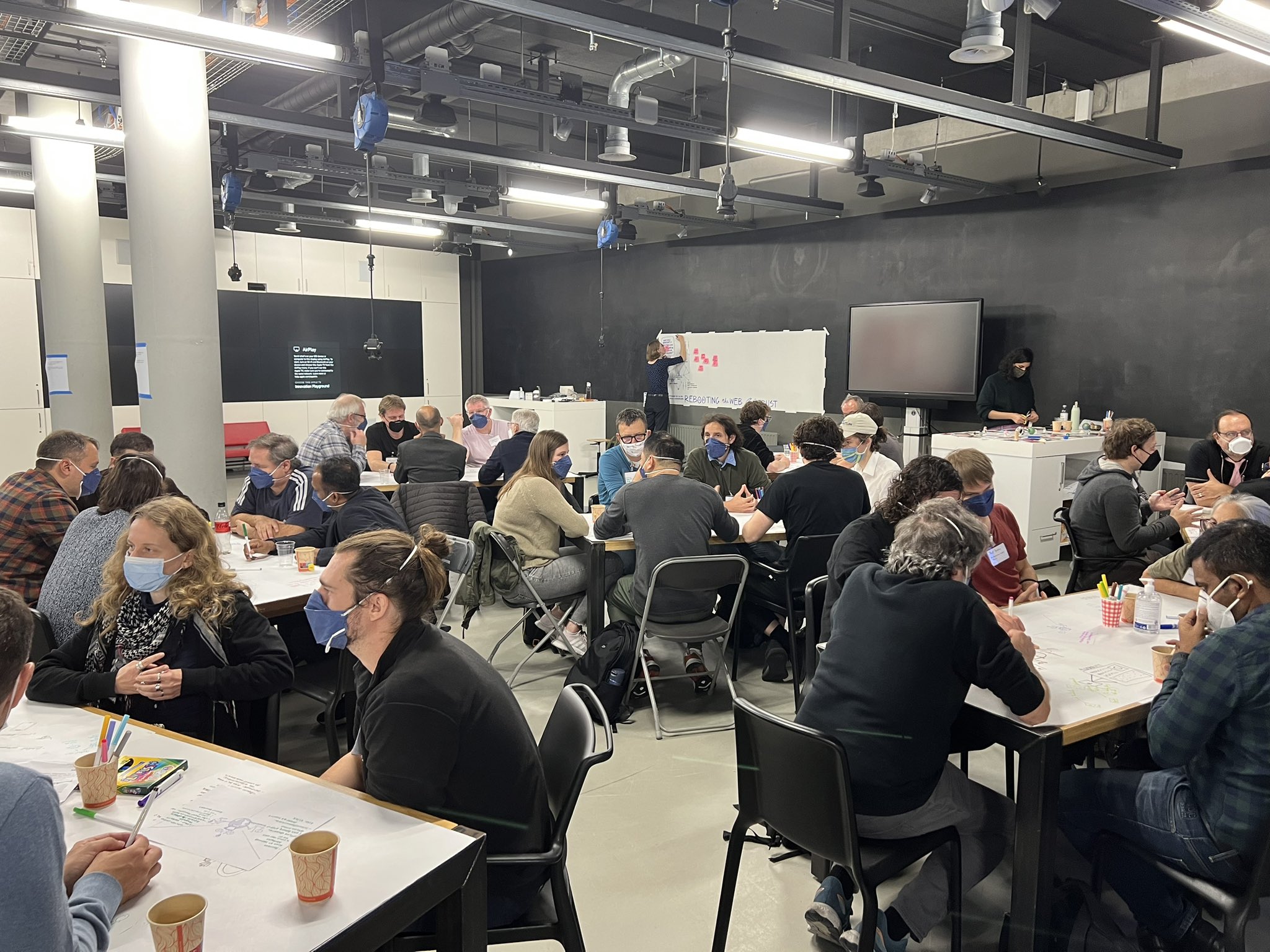
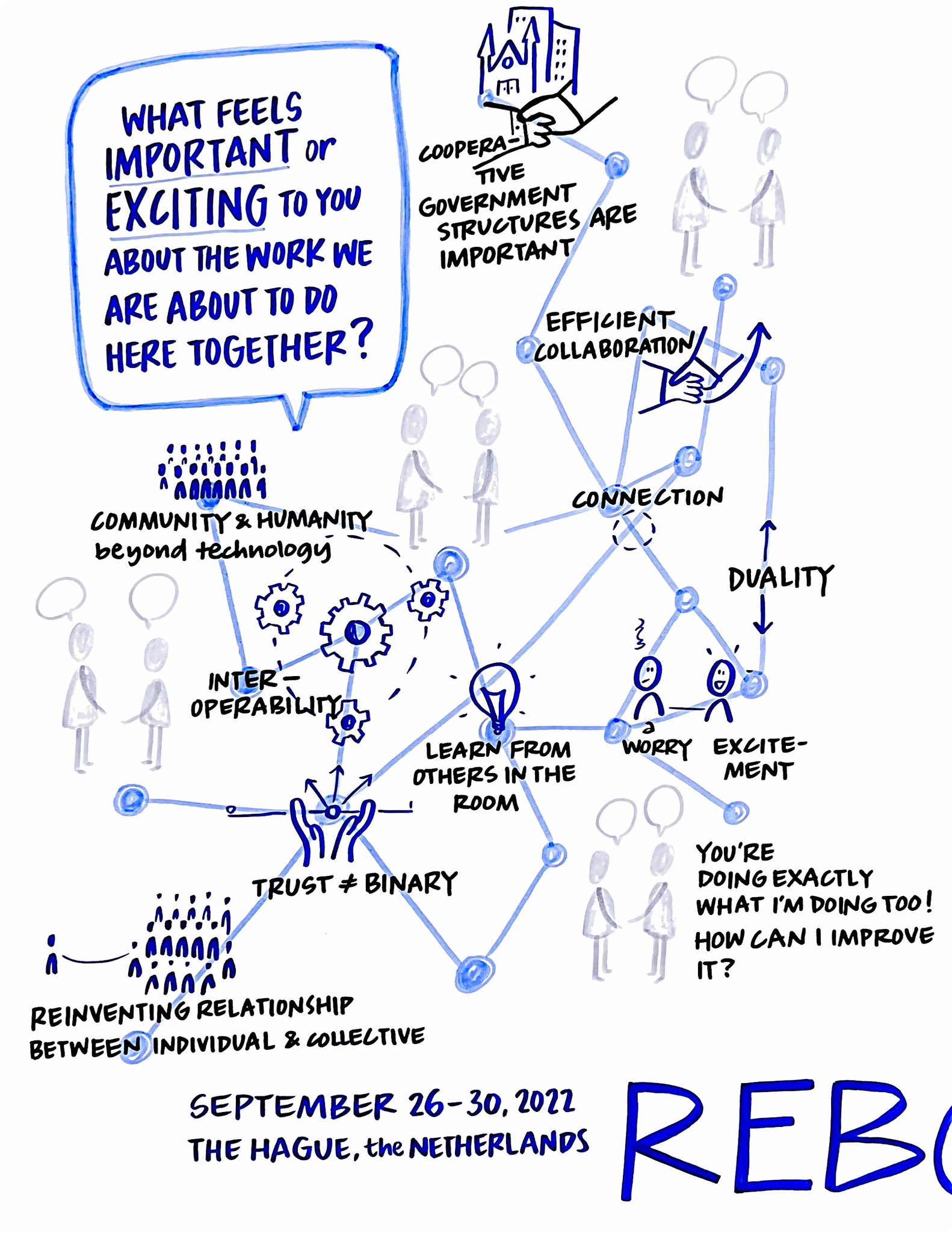
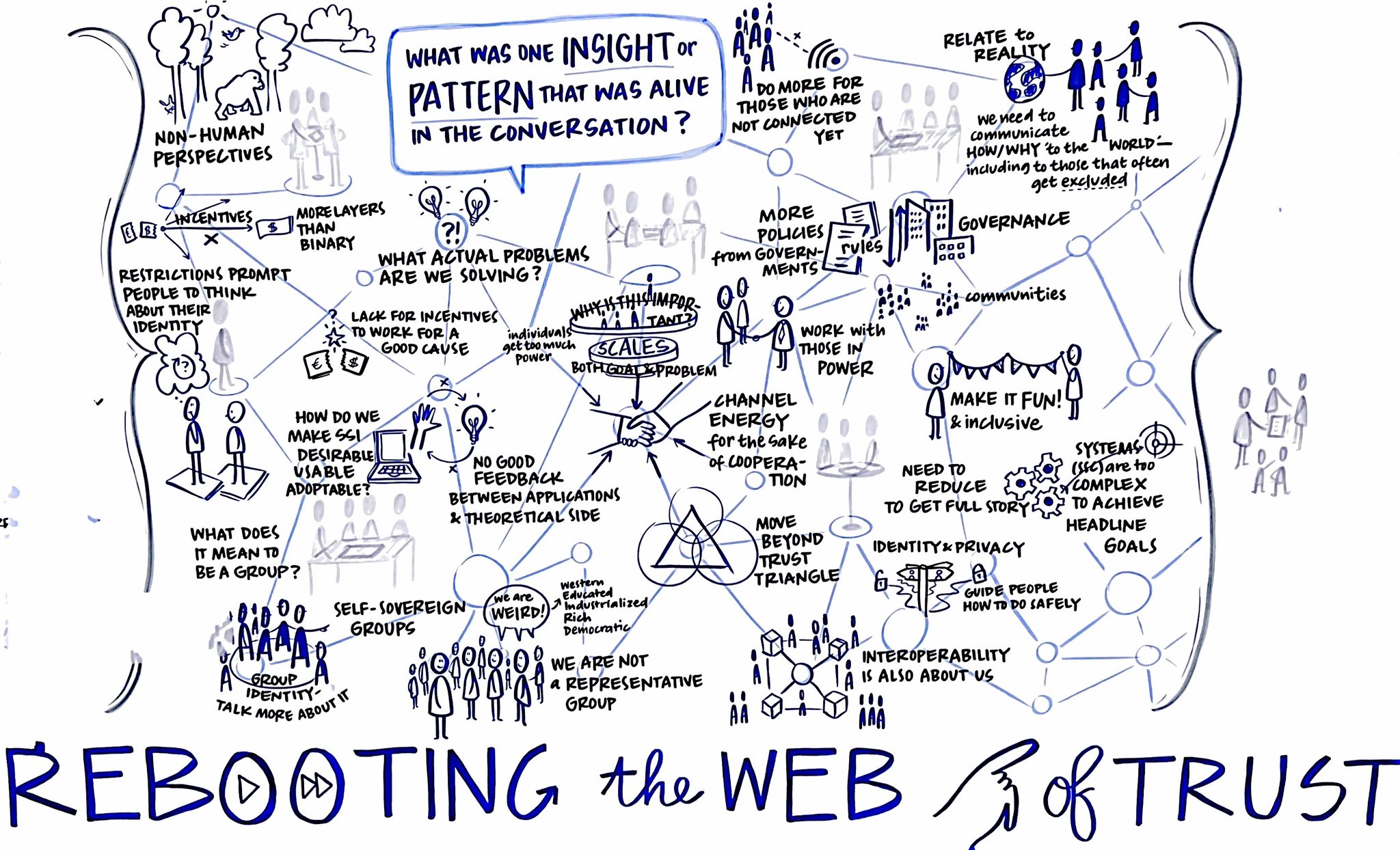
Participants at #RWOT11 distilling decentralized identity problems, insights, and possible solutions. Leveraging 3 rounds of WorldCafe facilitation at beginning of workshop to bring forward a sense of community on what we should focus on for the rest of the week.
Tue Sep 27 09:57:15 +0000 2022
Early capture from morning:
Tue Sep 27 15:05:40 +0000 2022
Collection of possible topics of interest before narrowing down to those that have sufficient team interest to collaborate on AND can be completed to first draft by Friday:
Tue Sep 27 15:14:56 +0000 2022
More pre-topic selection notes:
Tue Sep 27 20:46:37 +0000 2022
Potential topics thrown on floor for review before “dot voting” with green dots for “I want to be involved” or red dots for a “cautionary tale”:
Tue Sep 27 20:50:10 +0000 2022
All of the #RWOT11 teams are wrapping up their first drafts today. My team (@brent_zundel @peacekeeper @ft_ssi & Elena from @nymlab) wrote a paper on “Selective Correlation” about desirable correlation, threats, data minimzation and best practices: https://github.com/WebOfTrustInfo/rwot11-the-hague/blob/master/draft-documents/selective-correlation.md
Fri Sep 30 10:34:14 +0000 2022
Another first draft paper from #RWOT11 “Identity Threats” (by @kate_sills @Appelcline @CarstenStoecker & Cihan of @DanubeTech) lists different attacks on DID methods to better understand what threats a decentralized identity system might be vulnerable to. https://github.com/WebOfTrustInfo/rwot11-the-hague/blob/master/draft-documents/identity-threats.md
Fri Sep 30 10:46:04 +0000 2022
RT @KudrixD: We collaborated productively & intensely in greatest atmosphere at #RWOT11 on a matrix & paper titled „Credential Profile Comp…
Fri Sep 30 11:41:42 +0000 2022
At last day of #RWOT11 a group photo of our #DecentralizedIdentity advocates, architects & developers (missing a few heading home early or redacting themselves):
Fri Sep 30 11:56:27 +0000 2022
Relevant to some discussion I’ve had this week at #RWOT11 about the C2PA spec drafts, this is a new zk-proof by @danboneh (et al) that can verify cropped, resized, or rescaled images: https://medium.com/@boneh/using-zk-proofs-to-fight-disinformation-17e7d57fe52f
Fri Sep 30 17:40:02 +0000 2022
Full list (with abstracts) of draft papers on #DecentralizedIdentity written collaboratively by the 75+ attendees at #RWOT11 in The Hague. Huge range of topics: https://github.com/WebOfTrustInfo/rwot11-the-hague/tree/master/draft-documents