You can also Gordian Envelopes to improve the resiliency of your digital assets using a multi-permit authentication system, that works with symmetric secrets, public keys, advanced permits like quorum of shares, and even multiple permits at the same time. [4/11]
Thu Nov 03 19:50:13 +0000 2022
Our Gordian Envelopes offer a more privacy-focused encoding architecture than existing data formats such as JWT and JSON-LD. We believe it has a better security architecture than JWT and doesn’t fall victim to barriers of canonicalization complexity found in JSON-LD. [3/11]
Thu Nov 03 19:50:13 +0000 2022
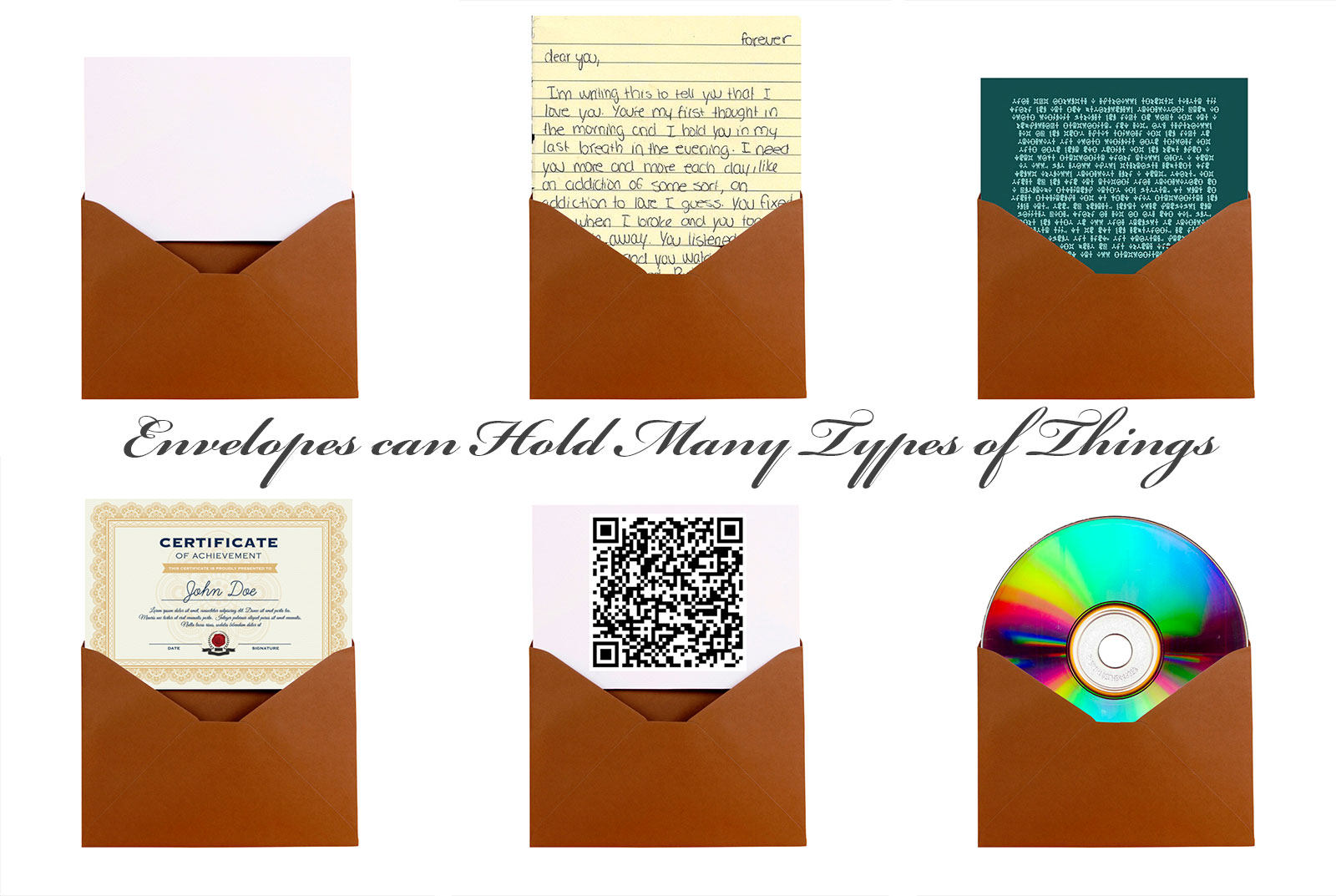
Real-world envelopes can do many more things. They can include special instructions, be locked and/or offer tamper-evident authentication seals from their creator. They can even have windows to show some of the material inside, which are selectively opaque or transparent. [2/11]
Thu Nov 03 19:50:13 +0000 2022
Some context on our new privacy tech from @BlockchainComns: We chose the “Envelope” as the core metaphor for these Smart Documents because they can privately contain & route plain text, encrypted text, small amounts of data or large, certificates, and much more!🧵[1/11] https://twitter.com/BlockchainComns/status/1588245396932857857
Thu Nov 03 19:50:13 +0000 2022
Or if you prefer a video, this 10-minute short also gives a high-level overview: [8/11] https://youtu.be/tQ9SPek0mnI
Thu Nov 03 19:50:14 +0000 2022
Read our “An Introduction to Gordian Envelope” for a broad, high-level overview. [7/11] dhttps://www.blockchaincommons.com/introduction/Envelope-Intro/
Thu Nov 03 19:50:14 +0000 2022
Alternatively, use Gordian Envelopes to protect your anonymity with proofs of inclusion and herd privacy techniques. [6/11] https://github.com/BlockchainCommons/BCSwiftSecureComponents/blob/master/Docs/10-EXISTENCE-PROOFS.md
Thu Nov 03 19:50:14 +0000 2022
You can use Gordian Envelope to selectively redact information, even if you’re not the source of that information. This gives users more choice about what information they wish to reveal when they present details issued by others about themselves. [5/11] https://github.com/BlockchainCommons/BCSwiftSecureComponents/blob/master/Docs/09-ELISION-REDACTION.md
Thu Nov 03 19:50:14 +0000 2022
Support this work on foundational specifications by becoming a sponsor of Blockchain Commons! [11/11] https://github.com/sponsors/BlockchainCommons
Thu Nov 03 19:50:15 +0000 2022
Or if you prefer videos, this playlist offers yet another deep dive with examples and demos of all the major features of Gordian Envelopes. [10/11] https://youtube.com/playlist?list=PLCkrqxOY1FbooYwJ7ZhpJ_QQk8Az1aCnG
Thu Nov 03 19:50:15 +0000 2022
If you are an engineer, our “Tech Intro” offers a good starting point for a deeper dive into the construction of Envelopes, with many links to other resources. [9/11] https://github.com/BlockchainCommons/Gordian/blob/master/Docs/Envelope-Tech-Intro.md
Thu Nov 03 19:50:15 +0000 2022
I’m thrilled to see the first #RWOT11 paper from our September collaborative workshop in The Hague “Taking out the CRUD” from a team led by @Kate_Sills… https://twitter.com/RWOTEvents/status/1588254274529636358
Fri Nov 04 18:55:25 +0000 2022
#RebootingWebOfTrust has been ongoing since 2015. Our goal: a global collaboration to empower individuals to co-create decentralized systems for lasting mutual benefit. https://www.WebOfTrust.info
Fri Nov 04 18:55:26 +0000 2022
This is the first #RebootingWebOfTrust we’ve had in three years due to COVID. It was a great success with over 70 participants and more than a dozen more collaborative papers in progress: https://github.com/WebOfTrustInfo/rwot11-the-hague/tree/master/draft-documents
Fri Nov 04 18:55:26 +0000 2022
The paper, which covers 5 potential threats when using Decentralized Identifiers (#DIDs), has already had a real-world impact with a PR to did:ethr: https://twitter.com/mirceanistor/status/1588546570982522880
Fri Nov 04 18:55:26 +0000 2022
We’re returning to the United States in 2023! Sign up for our mailing list to learn about our next event, #RWOT12 in Los Angeles event planned for March: https://www.weboftrust.info/subscribe/
Fri Nov 04 18:55:27 +0000 2022
No masks <sigh>
Wed Nov 16 02:26:38 +0000 2022
Replying to @LanceRootsID
I’d be interested in your thoughts on our hash-tree selective disclosure approach: https://github.com/BlockchainCommons/WIPs-IETF-draft-envelope
Wed Nov 16 02:31:03 +0000 2022
Replying to @drummondreed, @kristinayasuda and @Microsoft
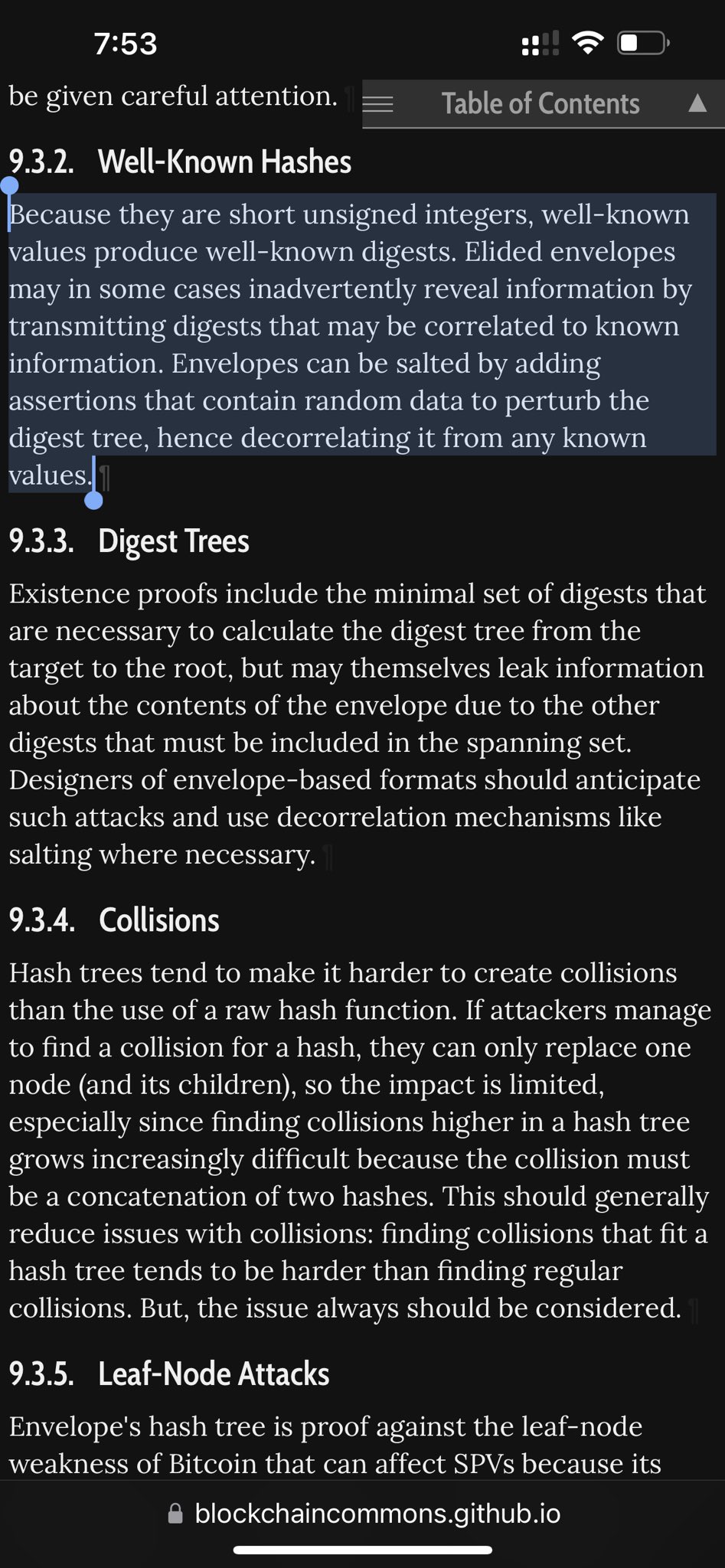
We are also doing different salts in our approach to hash-based selective disclosure. I’d be interested in a better understanding of correlation risks using salts: https://github.com/BlockchainCommons/WIPs-IETF-draft-envelope
Wed Nov 16 02:33:01 +0000 2022
Replying to @tlodderstedt and @kristinayasuda
I’d be interested in your thoughts on our alternative: https://github.com/BlockchainCommons/WIPs-IETF-draft-envelope
Wed Nov 16 02:34:11 +0000 2022
Replying to @vitorpamplona, @drummondreed, @kristinayasuda and @Microsoft
Are they doing some deterministic salts? from our security considerations: https://blockchaincommons.github.io/WIPs-IETF-draft-envelope/draft-mcnally-envelope.html
Wed Nov 16 03:54:32 +0000 2022
Replying to @vitorpamplona, @drummondreed, @kristinayasuda and @Microsoft
I agree that the randomness requirements for salts have to be higher than that for nonces. But I’d love any thoughts on how to offer more detail on this for our security considerations.
Wed Nov 16 04:00:54 +0000 2022
Replying to @OR13b, @vitorpamplona, @drummondreed, @kristinayasuda and @Microsoft
Why from a root nonce?
Wed Nov 16 04:13:02 +0000 2022
Replying to @OR13b, @vitorpamplona, @drummondreed, @kristinayasuda and @Microsoft
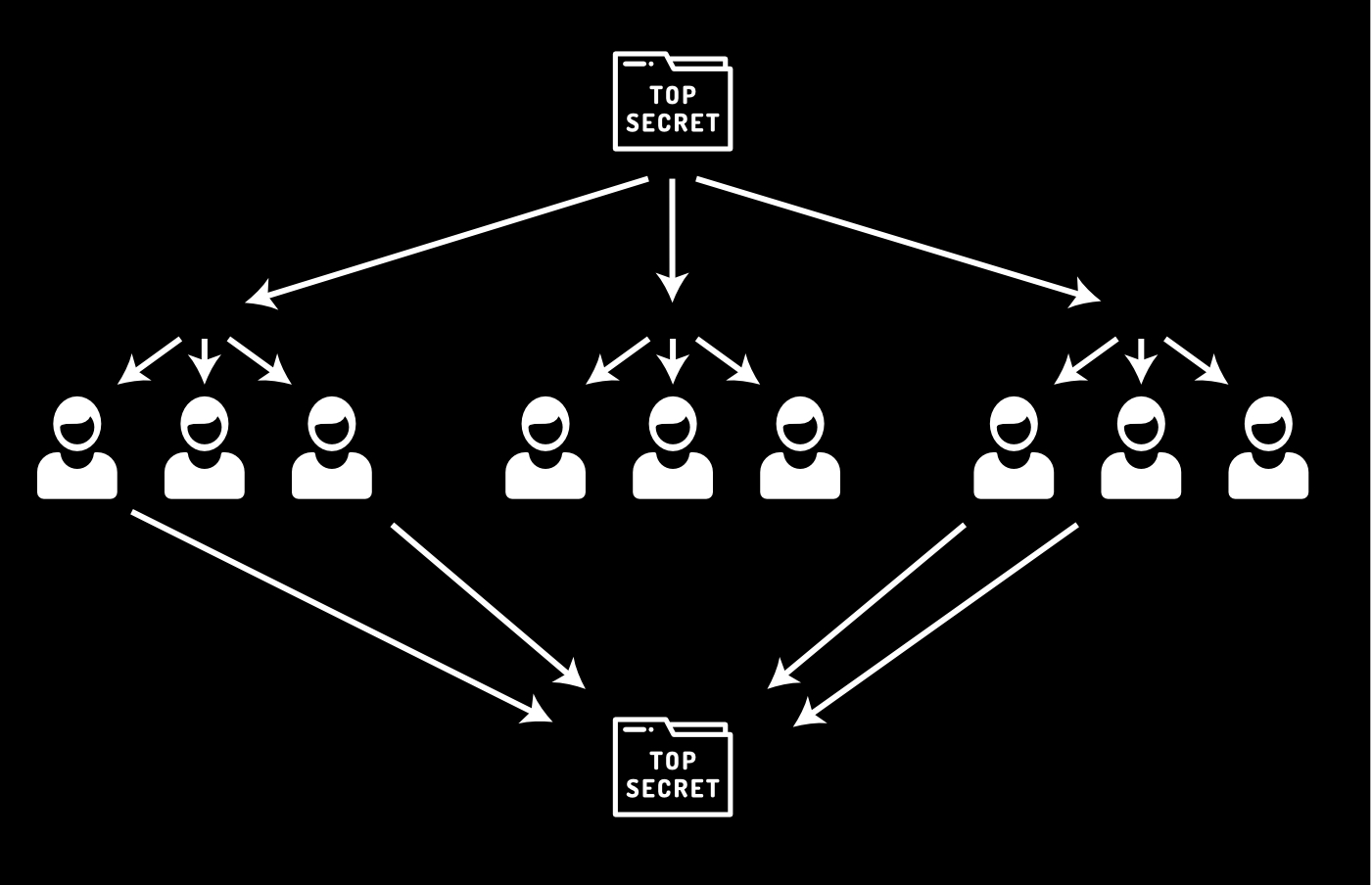
We’ve elected so far to use salts individually, not derived from a root because our form of VC (equivalent, not to standards) can be large aggregates. For instance, for herd privacy there could be one proof for whole graduating class, with existence proofs offered to students.
Wed Nov 16 04:57:36 +0000 2022
Replying to @OR13b, @vitorpamplona, @drummondreed, @kristinayasuda and @Microsoft
If the salt is from a root, all interior envelopes have to be created at same time, whereas in business reality (and multisig) the may be done at different times.
Wed Nov 16 04:59:13 +0000 2022
Replying to @OR13b, @vitorpamplona, @drummondreed, @kristinayasuda and @Microsoft
See video on elision in Gordian Envelopes https://youtu.be/3G70mUYQB18
Wed Nov 16 04:59:57 +0000 2022
Replying to @OR13b, @vitorpamplona, @drummondreed, @kristinayasuda and @Microsoft
…and on existence proofs: https://youtu.be/LUQ-n9EZa0U
Wed Nov 16 05:00:41 +0000 2022
Replying to @OR13b, @vitorpamplona, @drummondreed, @kristinayasuda and @Microsoft
Similarly we wanted an alternative to CL Sigs & BBS+ proofs as a base functionality. Not that those and other zk-proofs don’t have their place (I like bulletproofs) but we believe that they can be offered in addition to the basic functionality.
Wed Nov 16 05:09:08 +0000 2022
Replying to @OR13b, @vitorpamplona, @drummondreed, @kristinayasuda and @Microsoft
There also was a desire to be able to include encrypted objects that didn’t change the signature, or external references.
Wed Nov 16 05:10:39 +0000 2022
Replying to @OR13b, @vitorpamplona, @drummondreed, @kristinayasuda and @Microsoft
We are using envelopes for a lot more than VC or DID like structures. Here it is being used for seed sharding (social key recovery): https://github.com/BlockchainCommons/Gordian/blob/master/Docs/Envelope-Use-Cases-Assets.md
Wed Nov 16 05:12:45 +0000 2022
Fundamentally, you can create authenticated educational credentials with Gordian Envelopes. Great, everyone can do that. [2/9] https://github.com/BlockchainCommons/Gordian/blob/master/Docs/Envelope-Use-Cases-Educational.md#1-danika-proves-her-worth-credentials-signature
Thu Nov 17 18:44:42 +0000 2022
Smart Documents using our Gordian Envelope specs remain one of the top priorities at @BlockchainComns, so for #IIW week, I wanted to talk about some of the identity use cases by looking at educational credentials. [1/9] https://github.com/BlockchainCommons/Gordian/blob/master/Docs/Envelope-Use-Cases-Educational.md
Thu Nov 17 18:44:42 +0000 2022
Finally, the incorporation of credentials into large sets allows for herd privacy, such as a single one for a whole graduating class. This can protect them even from the issuer: users can decide when and if they ever reveal them! [6/9] https://github.com/BlockchainCommons/Gordian/blob/master/Docs/Envelope-Use-Cases-Educational.md#5-paul-privately-proves-proficiency-herd-privacy
Thu Nov 17 18:44:43 +0000 2022
Credentials don’t have to be offered by centralized or established authorities: peer-to-peer credentials are also possible with Gordian Envelopes! [5/9] https://github.com/BlockchainCommons/Gordian/blob/master/Docs/Envelope-Use-Cases-Educational.md#part-two-web-of-trust-credentials
Thu Nov 17 18:44:43 +0000 2022
That’s just the beginning, other holders can also repackage a Gordian Envelope, with their own elision and add their own credential endorsements. [4/9] https://github.com/BlockchainCommons/Gordian/blob/master/Docs/Envelope-Use-Cases-Educational.md#3-thunder–lightning-spotlights-danika-third-party–repackaging
Thu Nov 17 18:44:43 +0000 2022
The power of the Gordian Envelope comes from the fact that anyone can elide data, not just the issuer. Worried about discrimination because of your name, like Danika in our example? Just elide it out and the credential remains valid. [3/9] https://github.com/BlockchainCommons/Gordian/blob/master/Docs/Envelope-Use-Cases-Educational.md#2-danika-restricts-her-revelations-elision
Thu Nov 17 18:44:43 +0000 2022
Contact me if you’d like to become involved. You can also support the future development of interoperable specs like these by becoming a Blockchain Commons supporter! [9/9] https://github.com/sponsors/BlockchainCommons
Thu Nov 17 18:44:44 +0000 2022
Our intro to envelopes covers the topic generally. [8/9] https://github.com/BlockchainCommons/Gordian/blob/master/Docs/Envelope-Intro.md
Thu Nov 17 18:44:44 +0000 2022
Generally, Gordian Envelopes offer many features that we think are innovative and could offer improvements for decentralized identity uses. Elision, peer-to-peer credentialing, and herd privacy are some of the most notable! [7/9]
Thu Nov 17 18:44:44 +0000 2022
Replying to @codenamedmitri
It looks there are now multiple hash-based selective-disclosure approaches: in mDL, in SD-JWT, JSON-LD Merkle Disclosure (I’m not sure if ACDC offers it). Some interesting difference: first three are hash-lists, whereas Gordian Envelope does hash-trees, which has som efficiency…
Thu Nov 17 19:55:58 +0000 2022
Replying to @codenamedmitri
SD-JWT has a root salt that derives child salts, which does save on space, but makes multiple signatures much harder. Gordian Envelopes offers optional salts for each entry, at multiple levels, because sometimes correlation of hashes IS desirable.
Thu Nov 17 19:58:36 +0000 2022
Replying to @codenamedmitri
A particular feature that none of the other formats offers is support for non-VC structures, such as very large “herd privacy” structures. For instance a single VC for a large graduating class, or other large cohorts, where instead of a VC to students they get an existence proof.
Thu Nov 17 20:00:55 +0000 2022
https://twitter.com/codenamedmitri/status/1593321646785368065
Thu Nov 17 20:01:52 +0000 2022
RT @chrisheuer: Great session leading to action at #iiw New group working to #endsurveillancecapitalism Stop tracking us, stop manipulating…
Thu Nov 17 23:29:15 +0000 2022
List of deceptive language compiled at #IIW. In particular today I feel the #DarkPattern “CONSENT:
Sign indemnification contract with us from any potential liability without knowing what you sign.” https://twitter.com/_nat_en/status/1593050322767056898
Thu Nov 17 23:34:35 +0000 2022
RT @moskovich: @pujaohlhaver We’re working on this collaborative model for custody with @BlockchainComns. You should check out their work h…
Thu Nov 24 03:35:32 +0000 2022
Replying to @moskovich, @pujaohlhaver and @BlockchainComns
Collaborative Seed Recovery, or CSR, is a new system intended to automate the recovery of seeds and other sensitive digital data in a way that is safe, secure, and simple to use. https://github.com/BlockchainCommons/Gordian/blob/master/Docs/CSR.md