Replying to @aalexis1234 and @BobSummerwill
I plan to be there & the builders day before.
Mon Jul 02 17:03:40 +0000 2018
RT @KamesCG: Decentralized identity is a lot of things to a lot of people. For some it’s simply a technical challenge. Others it’s a chance…
Mon Jul 02 23:23:46 +0000 2018
RT @KamesCG: Establishing networks of trust is woven into Mankind’s DNA. We are a species of community and coordination. We navigate this r…
Mon Jul 02 23:24:39 +0000 2018
Identity barriers for on/off ramps to Bitcoin are getting quite annoying. Not accepting AUS passport & US greencard seems extreme, but I presume it is a NY bitlicense requirement or a conservative interpretation of it. Unfortunately, by ignoring identity we become hostage to it. https://twitter.com/skycorridors/status/1014205763647082498
Tue Jul 03 18:53:42 +0000 2018
I’ve been saying for years that a number of older cryptographic systems like Chaumian e-Cash & Brandian/uProve Blinded Signatures should be revisited given existence of blockchain tech. It’s started given future Schnorr! Slides from @n1ckler #BuildingOnBtc https://nickler.ninja/slides/2018-bob.pdf
Tue Jul 03 19:38:15 +0000 2018
Transcript of @n1ckler’s presentation at #BuildingOnBitcoin by @kanzure on Blind Signatures & Scriptless Scripts http://diyhpl.us/wiki/transcripts/building-on-bitcoin/2018/blind-signatures-and-scriptless-scripts/
Tue Jul 03 19:43:30 +0000 2018
I have joined the Advisory Board of Veres One, a browser-centric, fit-for-purpose, self-sovereign identity focused blockchain. Also a different business model: No token, no ICO — all services are paid for by the users in fiat, with percentages of revenue dedicated to open source. https://twitter.com/manusporny/status/1014304464461881350
Wed Jul 04 06:27:53 +0000 2018
Our biggest fans this week: @pierre_rochard, @giacomozucco, @bitstein. Thank you! via https://sumall.com/thankyou?utm_source=twitter&utm_medium=publishing&utm_campaign=thank_you_tweet&utm_content=text_and_media&utm_term=d0ab6b00ad990b36d99f7a0b
Wed Jul 04 16:01:02 +0000 2018
The intent of Open Banking in the EU is to increase competition for customers by allowing portability. However, apparently the administrative hurdles are so high that users are not taking advantage of it. A new competitive case study of barriers to exit? Like moving domains are. https://twitter.com/chris_skinner/status/1014397660323831808
Wed Jul 04 18:49:19 +0000 2018
👍Insightful graphic by @VladZamfir that explores a model for the intersection & edges of game theory, markets, mechanism design, distributed systems, incentive design & blockchains. Needs some exploring by experts in each of these knowledge domains to see if missing some edges. https://twitter.com/vladzamfir/status/1014882947781087233
Thu Jul 05 16:51:10 +0000 2018
RT @VladZamfir: @ChristopherA I can already feel dist sys ppl chiming in about how incentives don’t matter or don’t exist or aren’t compute…
Thu Jul 05 17:57:43 +0000 2018
RT @AnnaLysyanskaya: @gregoryneven @ChristopherA @n1ckler Yup – both on the let’s revisit Chaumian stuff, and on let’s not use blind Schno…
Thu Jul 05 17:59:08 +0000 2018
RT @trbouma: @boscolochris Thanks for this! In Canada, we’re starting to think how we can relate #digitalidentity to Section 6 of the Chart…
Fri Jul 06 00:51:46 +0000 2018
RT @_shaunconway: Impact Tokens tell the story… @ixo_impact https://t.co/AxU1rsWvAd
Fri Jul 06 06:36:11 +0000 2018
The video presentation at #OffTheChain by @pedrorechez on the paper on Lightning Network “Multi-hop Locks” is now available. Their approach & proof for a “Scriptless ECDSA” shoud very useful until Bitcoin gets Schnorr. Great work! 👍 https://www.youtube.com/watch?v=sUxh6wO_Z00&feature=youtu.be&t=9m10s
Sat Jul 07 00:30:37 +0000 2018
RT @ChristopherA: The video presentation at #OffTheChain by @pedrorechez on the paper on Lightning Network “Multi-hop Locks” is now availab…
Sat Jul 07 00:33:05 +0000 2018
👍👏I’ve been looking forward to @pwuille’s formalization of Schnorr Signatures using bitcoin’s secp256k1 curve for a LONG time. 64 bytes! A lot of work is behind this to ensure security for musig & other interesting constructions possible in the future: https://github.com/sipa/bips/blob/bip-schnorr/bip-schnorr.mediawiki
Sat Jul 07 00:58:52 +0000 2018
Replying to @KyleSamani
The Schnorr patent didn’t expire until February 2008. In the meantime the NSA designed ECDSA had been available, implemented & studied for over 10 years under a royalty-free license. Satoshi was wise to not use immature Schnorr code in 2009. Ten years later it is now time!!
Sat Jul 07 01:05:51 +0000 2018
RT @ChristopherA: @KyleSamani The Schnorr patent didn’t expire until February 2008. In the meantime the NSA designed ECDSA had been availab…
Sat Jul 07 01:05:56 +0000 2018
👍More important than you think—our brains guess Gaussian, but Networks have Big Tails: “In Mediocristan, no observation can really change the statistical properties. In Extremistan, the tails (the rare events) play a disproportionately large role in determining the properties” https://twitter.com/nntaleb/status/1015050372329680898
Sat Jul 07 01:14:26 +0000 2018
RT @notgrubles: When you forget Ethereum couldn’t implement multisignature storage correctly: https://twitter.com/KyleSamani/status/1015386893393985536
Sat Jul 07 01:25:42 +0000 2018
One of the challenges of Schnorr is that it is so incredibly powerful & elegant that it appears to be simple—this leads naive implementations with severe consequences. In addition, early implementations were focused on single sig use cases & today’s are multisig. Hard problems! https://twitter.com/bitcoinerrorlog/status/1015327043536523269
Sat Jul 07 02:17:54 +0000 2018
Replying to @aalexis1234
I’m fairly confident given how conservative @pwuille is that this formalization is pretty solid. But we need more non-bitcoin members of the cryptographic community to give a look to see if something still missing. Next, sidechannel-resistant code needs coding & security reviews.
Sat Jul 07 02:34:48 +0000 2018
RT @Drabiv: Till now only kings and nations where sovereign. The king was a sovereign, others were subjects. Now #SovereigntyEnablingTechno…
Sat Jul 07 02:38:17 +0000 2018
RT @Drabiv: …it opens a way to create an “Organization of United Humans” based on Self-Sovereign Identities that uniquely represent huma…
Sat Jul 07 02:38:24 +0000 2018
Replying to @aalexis1234, @pwuille, @el33th4xor and @Cornell
In some ways @el33th4xor is still probably too close to bitcoin community for good review — I wouldn’t be surprised if he saw early versions. I’d like to see review of this Schnorr from many different domains @hashbreaker @JanCamenisch @AnnaLysyanskaya @Bryanosaurus @timdierks
Sat Jul 07 02:51:52 +0000 2018
RT @ChristopherA: @aalexis1234 @pwuille @el33th4xor @Cornell In some ways @el33th4xor is still probably too close to bitcoin community for…
Sat Jul 07 02:52:06 +0000 2018
Should not go that broad for review of Schnorr — it is fairly specific knowledge required for review of this. I don’t feel qualified myself, more that I have a good understanding of why it isn’t easy. Unfortunately, leading edge cryptographers are doing quantum resistance work.
Sat Jul 07 03:21:24 +0000 2018
RT @pwuille: @pbarreto @Snyke We’ve since updated our MuSig paper whose proof was broken by that paper, replacing it with a 3-round scheme.…
Sat Jul 07 03:25:18 +0000 2018
There is a line where too many people without sufficient knowledge can lead to bikeshedding. You want the correct “requisite variety” (a cybernetic term) with both amplification AND attenuation. Otherwise feedback systems can fail to deliver good results. A designer’s fine line.
Sat Jul 07 03:31:33 +0000 2018
RT @DarioTepoTec: @pwuille, of 🇧🇪, proposes a standard for 64-byte Schnorr signatures over the elliptic curve secp256k1.
Belgium 🇧🇪 beats…
Sat Jul 07 03:44:38 +0000 2018
Replying to @michaelfolkson, @kanzure and @KyleSamani
Schnorr has been implemented elsewhere, in particular in combination @hashbreaker’s 25519 curve. However, these implementations are focused on single-signature use cases. @pwuille’s formalization is focused on fast verification In multisig use cases & address multisig attacks.
Sat Jul 07 13:52:42 +0000 2018
RT @ChristopherA: @michaelfolkson @kanzure @KyleSamani Schnorr has been implemented elsewhere, in particular in combination @hashbreaker’s…
Sat Jul 07 13:54:27 +0000 2018
Replying to @cryptodoger, @kanzure and @KyleSamani
Bitcoin does not use the standard NIST defined ECDSA curve’s “random” constant which is widely questioned as being created by NSA. Instead, Satashi chose a variation called secp256k1 which has a prime constant considered safer. https://bitcointalk.org/index.php?topic=289795.msg3183975#msg3183975
Sat Jul 07 14:04:33 +0000 2018
RT @ChristopherA: @cryptodoger @kanzure @KyleSamani Bitcoin does not use the standard NIST defined ECDSA curve’s “random” constant which is…
Sat Jul 07 14:04:38 +0000 2018
Replying to @johnny10MD, @Fiskantes and @KyleSamani
https://twitter.com/christophera/status/1015401476846280705?s=21
Sun Jul 08 09:02:44 +0000 2018
RT @kimdhamilton: I’m very excited to announce that next W3C CCG meeting will focus on uPort DID/VC Protocols, Libraries & Solutions. Join…
Mon Jul 09 02:34:28 +0000 2018
👍🗝💬“I have overvalued reasoning in myself and others and undervalued pride, fear and the need to belong. I’ve been operating like an economist, in other words — an economist from the 1960s.” https://thewholestory.solutionsjournalism.org/complicating-the-narratives-b91ea06ddf63
Mon Jul 09 20:14:28 +0000 2018
👍🗝💬“The idea is to revive complexity in a time of false simplicity…reporters do the opposite…we look for coherence, which is tidy — and natural. The problem is that, in a time of high conflict, coherence is bad journalism, bordering on malpractice.” https://thewholestory.solutionsjournalism.org/complicating-the-narratives-b91ea06ddf63
Mon Jul 09 20:18:53 +0000 2018
RT @ChristopherA: 👍🗝💬“The idea is to revive complexity in a time of false simplicity…reporters do the opposite…we look for coherence, which…
Mon Jul 09 20:18:58 +0000 2018
👍🗝💬“What is oversimplified about this issue? How has this conflict affected your life? What do you think the other side wants? What’s the question nobody is asking? What do you…need to learn about the other side in order to understand them better?” https://thewholestory.solutionsjournalism.org/complicating-the-narratives-b91ea06ddf63
Mon Jul 09 20:22:53 +0000 2018
RT @ChristopherA: 👍🗝💬“What is oversimplified about this issue? How has this conflict affected your life? What do you think the other side w…
Mon Jul 09 20:22:58 +0000 2018
RT @theyblinked: Five Questions For Credential Issuing Systems
“When the blockchain is properly used as a decentralized verification netwo…
Mon Jul 09 20:52:53 +0000 2018
Though it is a cool security UI idea (color changing keyboard to reflect security) without a trusted interface between computer and display it is likely to be hacked along with the primary hack. I do, however, like the idea of a keyboard with an HSM/TPM. https://twitter.com/drwhax/status/1016290493297242112
Mon Jul 09 21:00:02 +0000 2018
Replying to @DanielSolis
If you want advice and insider jokes, let me know.
Mon Jul 09 21:07:38 +0000 2018
RT @rdonoghue: Whelp, HBO had a good run. I do not look forward to watching its hollowed out corpse shamble around.
Mon Jul 09 22:42:13 +0000 2018
“To act jointly, we journey from disparate places to a coherent, collective sense of what is real, what we desire & what we will do to accomplish it. Group alignment emerges through conversations that generate shared stories, understandings & decisions.” http://groupworksdeck.org/patterns/Moving_toward_Alignment
Mon Jul 09 22:56:22 +0000 2018
Latest #RebootingWebOfTrust Design Shop white paper (the 35th!!) has gone now to Final Draft “Open Badges are Verifiable Credentials” led by @ottonomy & @kimdhamilton—from here we take it to the W3C Credentials CG for further discussion towards a standard. https://github.com/WebOfTrustInfo/rebooting-the-web-of-trust-spring2018/blob/master/final-documents/open-badges-are-verifiable-credentials.md
Tue Jul 10 00:31:00 +0000 2018
RT @patestevao: My presentation at @build_on_btc about building ⚡️Lightning Network interfaces that avoid breaking the Bitcoin user’s menta…
Tue Jul 10 00:32:18 +0000 2018
RT @kate_sills: Thread on the difference between transactions and contracts:
Tue Jul 10 00:35:53 +0000 2018
My long-time co-author @Appelcline & I have turned in our manuscript for “Meeples Together” on design & theory of collaborative tabletop games, to be published by @GamePlayWright. Hopefully first in series. Here is a photo from our early re-design of Arkham Horror 15+ years ago!
Tue Jul 10 01:40:53 +0000 2018
Tomorrow’s W3C Credentials CG call (IRC & VoIP) Tuesday at 12p ET (9am PT) will be focused on report out by one the teams implementing DIDs (Decentralized Identifiers) & Verifiable Credentials—@Consensys @uport_me using the Ethereum blockchain & EIP 1056 https://lists.w3.org/Archives/Public/public-credentials/2018Jul/0013.html
Tue Jul 10 02:05:15 +0000 2018
RT @kimdhamilton: “Open Badges are Verifiable Credentials” by @ottonomy and me describes combining the rich vocab, expressiveness, ecosyste…
Tue Jul 10 02:32:45 +0000 2018
You can get updates about our upcoming Kickstarter & release of the book “Meeples Together” via our new Twitter account @MeeplesTogether or Facebook https://www.facebook.com/MeeplesTogether/ — @Appelcline & I also have plans for a blog with cooperative game reviews that didn’t make it into book.
Tue Jul 10 02:36:43 +0000 2018
RT @ChristopherA: You can get updates about our upcoming Kickstarter & release of the book “Meeples Together” via our new Twitter account @…
Tue Jul 10 02:43:23 +0000 2018
RT @JoeAndrieu: @kimdhamilton @BryceWeiner With those working on the standard, it’s well understood that the best practice for maximum priv…
Tue Jul 10 04:40:51 +0000 2018
RT @windley: In a study by Omidyar 1.2 million people denied access to rations because of Aadhaar-related issues. Identity problems can cau…
Tue Jul 10 04:45:55 +0000 2018
Replying to @windley and @Subhashish30
Link to study?
Tue Jul 10 04:46:19 +0000 2018
RT @JeremyRubin: Adapter signatures: a swapped pair of tweaked signatures which are both damaged by the same tweak. Revealing one non tweak…
Tue Jul 10 04:46:31 +0000 2018
#qotd (quote of the day): “Start a stone rolling so in three centuries you’ll have an avalanche.” — @tithenai quoted by @katarinahit via @maxgladstone. I hope I’ve started some stones rolling that will not take quite so long.
Tue Jul 10 06:10:22 +0000 2018
RT @MeeplesTogether: So what’s @MeeplesTogether ? Co-author @Appelcline wrote a long journal entry today about the evolution of this book o…
Tue Jul 10 06:20:54 +0000 2018
RT @Appelcline: I’ve got an unsightly 6-7 books in progress right now. Fortunately one more went to the publisher today: @MeeplesTogether,…
Tue Jul 10 06:21:42 +0000 2018
RT @jefftidball: Meeples Together (@MeeplesTogether) will be a @Gameplaywright release! We’re thrilled to be publishing this great manuscri…
Tue Jul 10 16:49:08 +0000 2018
“Consciously decide to give more attention to where we agree than where we don’t. By tuning in to what we share, we find the way to make progress together.” #GroupWorks https://groupworksdeck.org/patterns/Common_Ground
Tue Jul 10 17:37:57 +0000 2018
RT @FutureCitiesPGH: Few innovations could have as far-reaching impacts on city life. The best part? Superblocks are virtually free. Let’s…
Tue Jul 10 23:32:33 +0000 2018
RT @kimdhamilton: Today’s Credential CG meeting was especially epic: @uport_me, DIDs, and … smooth jazz? You’ll have to listen https://t.…
Tue Jul 10 23:32:49 +0000 2018
Is anyone working on HSM/TPMs under the RISC-V architecture? We need open source/open patent solutions in this space as proprietary Intel & ARM solutions are scary. https://twitter.com/radhakrshn11/status/1016763480706252801
Tue Jul 10 23:35:26 +0000 2018
Replying to @floatfloatboat
But is it being implemented by anyone? Any silicon commitments?
Wed Jul 11 01:17:21 +0000 2018
Replying to @PindarWong, @risc_v and @SiFiveInc
I have a @SiFiveInc developer board & am waiting for the companion “Unleashed” expansion board before playing around more. Trying to identify folk interested in TPM/HSM architectures using RISC-V, but I don’t come from a hardware background so still have a lot to learn.
Wed Jul 11 01:33:44 +0000 2018
Replying to @hrdwrknvrstps
uPort is only one of many DIDs being currently deployed. Both @SovrinID & @VeresOneID are fairly far along, there is BTC-based DID hackathon starting Monday, and many more unannounced ones on way.
Wed Jul 11 04:50:14 +0000 2018
RT @ChristopherA: @hrdwrknvrstps uPort is only one of many DIDs being currently deployed. Both @SovrinID & @VeresOneID are fairly far along…
Wed Jul 11 04:50:22 +0000 2018
This constant-time verifiable sort is mostly useful for securing lattice-based cryptography, which is one of a number of possible post-quantum cryptography solutions. But I suspect there may be other uses. @pwuille? @tdierks? @moxie? @JanCamenisch? Is Paul Kocher on Twitter? https://twitter.com/hashbreaker/status/1016821281998721025
Wed Jul 11 05:46:03 +0000 2018
Our biggest fans this week: @theonevortex, @pierre_rochard, @giacomozucco. Thank you! via https://sumall.com/thankyou?utm_source=twitter&utm_medium=publishing&utm_campaign=thank_you_tweet&utm_content=text_and_media&utm_term=d0ab6b00ad990b36d99f7a0b
Wed Jul 11 16:01:07 +0000 2018
RT @sciphijournal: Why the Culture Wins: An Appreciation of Iain M. Banks http://sciphijournal.org/why-the-culture-wins-an-appreciation-of-iain-m-banks/
Thu Jul 12 04:24:47 +0000 2018
RT @smdiehl: Open sourced a new Haskell bulletproofs library for constructing short non-interactive zero-knowledge proofs that require no t…
Thu Jul 12 05:11:36 +0000 2018
Replying to @twshelton, @hrdwrknvrstps, @SovrinID and @VeresOneID
Details on next week’s BTCR DID Virtual Hackathon are at https://w3c-ccg.github.io/announcements/
Thu Jul 12 18:18:09 +0000 2018
Replying to @jdegoes and @prezcannady
I’ve been successful with that strategy in past. SSL/TLS was built by team at 80% salary 20% time off during peak of dotcom boom. Trying again: https://twitter.com/christophera/status/995413235451875328
Thu Jul 12 18:23:36 +0000 2018
“Shepherding a group discussion includes discerning when the group needs a wider view vs. when to sink down into the details. Zoom out to see vision, patterns, and overall trends; zoom in for examples, specific data, and other particulars.” https://groupworksdeck.org/patterns/Seeing_the_Forest_Seeing_the_Trees #GroupWorks
Thu Jul 12 18:55:02 +0000 2018
Some interesting thoughts here about leveraging zksnarks—it can prove that a leaf is a member of a merkel tree without reavealing which leaf it is or the leaf pre-image. It needs quite a bit of review & I’d like to see it generic & an academic-style paper with some formal proofs. https://twitter.com/barrywhitehat/status/1017438443373096965
Thu Jul 12 19:07:20 +0000 2018
RT @alexbosworth: Routing/Swaps is only 1 type of paid service that a LN node operator could provide
Others:
- Watch for channel breaches…
Thu Jul 12 19:12:33 +0000 2018
Replying to @prezcannady and @jdegoes
Choices were 1-day off a week, arrive late or leave early, or 10 weeks vacation (max 4 weeks at a time). We had several people with families use the first alternatives, others preferred the vacation time. More recently I had 1-day off a week with Blockstream to do dentity work.
Thu Jul 12 19:21:14 +0000 2018
Replying to @prezcannady and @jdegoes
Our CFO at Consensus Development was @CastroLang, who took day off a week as he was an ordained minister to a local struggling church. Several people had kids they took home from school. @tdierks & I took long breaks to refresh.
Thu Jul 12 19:25:24 +0000 2018
Replying to @tdierks, @prezcannady, @jdegoes and @Castrolang
I remember your month long vacation post shipping SSL-Plus where we struggled to answer some customer questions. 😊 In actuality it ended being a good thing as it forced the rest of the team to be able to answer them.
Thu Jul 12 20:33:30 +0000 2018
Replying to @tdierks, @prezcannady, @jdegoes and @Castrolang
It wasn’t a perfect system. I vaguely remember that for those who took off one day a week we eventually tried to have a policy of “any day EXCEPT Wednesday” so we could consistently schedule meetings . But I think it key thing was to express the intent it was important value.
Thu Jul 12 20:41:41 +0000 2018
This is why we need to move to transparent open source & open patent solutions like RISC-V 👇 https://twitter.com/iohk_charles/status/948923810618671104
Fri Jul 13 17:02:01 +0000 2018
RT @NickSzabo4: No. We already have several words for that: “program.” Also “software”. Or “dApp” if it’s distributed. You need not and sh…
Fri Jul 13 17:07:08 +0000 2018
Replying to @fp_robo
We are in the process as a community to revise the 10 self-sovereign identity principles. We probably should not have started with “#1 Existence” as it is the hardest, but will be staring on “#2 Control” on 7/23. See lively discussion of #1 at https://github.com/WebOfTrustInfo/self-sovereign-identity/issues/6 — join us!!
Fri Jul 13 21:26:01 +0000 2018
RT @ChristopherA: @fp_robo We are in the process as a community to revise the 10 self-sovereign identity principles. We probably should not…
Fri Jul 13 21:26:13 +0000 2018
RT @fp_robo: A small preview of FPR’s forthcoming paper on self-sovereign digital identity
Fri Jul 13 21:26:15 +0000 2018
Here is a beginning of a discussion on revising self-sovereign identity principle #2 “Control. Users must control their identities.” Goal is to revise this principle by end of month, and all 20 principals by October. https://github.com/WebOfTrustInfo/self-sovereign-identity/issues/8
Fri Jul 13 21:52:13 +0000 2018
Replying to @fp_robo
https://twitter.com/christophera/status/1017889460598419456?s=21
Fri Jul 13 21:52:56 +0000 2018
Amira 1.00 from #RebootingWebOfTrust is final! “In our scenario, Amira is a successful programmer working in Boston at a prestigious multi-national bank. Outside of working hours, Amira wants to give back to her community by writing software that matters.” https://github.com/WebOfTrustInfo/rebooting-the-web-of-trust-fall2017/blob/master/final-documents/amira.md
Sat Jul 14 01:25:18 +0000 2018
Many thanks to @JoeAndrieu for taking leadership on this document! The topic is very important to me as it reflects the original vision (almost 3 years ago!) of what I hoped #RebootingWebOfTrust might be able to accomplish! Also a thank you to the many other contributors…
Sat Jul 14 01:32:36 +0000 2018
A shout out & thank you to the other co-authors of #RebootingWebOfTrust Amira 1.0.0 including @Appelcline, @CaptainCalliope, @tonilanec, Tim Chen, @davetfields, Micheal Haley, @digitalsista, @heathervescent & @IdentityWoman — also contributors Patrick McBennett, Raghav Chawla.
Sat Jul 14 01:46:02 +0000 2018
Replying to @AnnaLysyanskaya, @gregoryneven, @n1ckler and @FBaldimtsi
For full reference “Anonymous Credentials Light” by Foteini Baldimtsi, Anna Lysyanskaya “We define and propose an efficient and provably secure construction of blind signatures with attributes.” https://eprint.iacr.org/2012/298.pdf
Sat Jul 14 01:53:15 +0000 2018
RT @ChristopherA: @AnnaLysyanskaya @gregoryneven @n1ckler @FBaldimtsi For full reference “Anonymous Credentials Light” by Foteini Baldimtsi…
Sat Jul 14 01:53:19 +0000 2018
Replying to @AnnaLysyanskaya, @gregoryneven, @n1ckler and @FBaldimtsi
I’d love to see a #SmartSignature predicate language (NOT a consensus script) that could directly support Schnorr operations such as scriptless scripts operations, as well as operations to support these BL anonymous blind signatures & attributes.
Sat Jul 14 02:02:47 +0000 2018
RT @ChristopherA: @AnnaLysyanskaya @gregoryneven @n1ckler @FBaldimtsi I’d love to see a #SmartSignature predicate language (NOT a consensus…
Sat Jul 14 02:14:01 +0000 2018
RT @ericasadun: [http://self.be(Best.self)
](http://self.be(Best.self)) (shamelessly stolen from@IanKay)
Sat Jul 14 02:26:50 +0000 2018
On Monday at 9am PT, the W3C Credentials CG is hosting a 5-day virtual hackathon on making some ideas behind this Amira user story possible by implementing a proof-of-concept using Bitcoin-based DIDs (Decentralized Identifiers) & Verifiable Credentials: https://w3c-ccg.github.io/announcements/
Sat Jul 14 02:54:42 +0000 2018
RT @ChristopherA: On Monday at 9am PT, the W3C Credentials CG is hosting a 5-day virtual hackathon on making some ideas behind this Amira u…
Sat Jul 14 02:54:50 +0000 2018
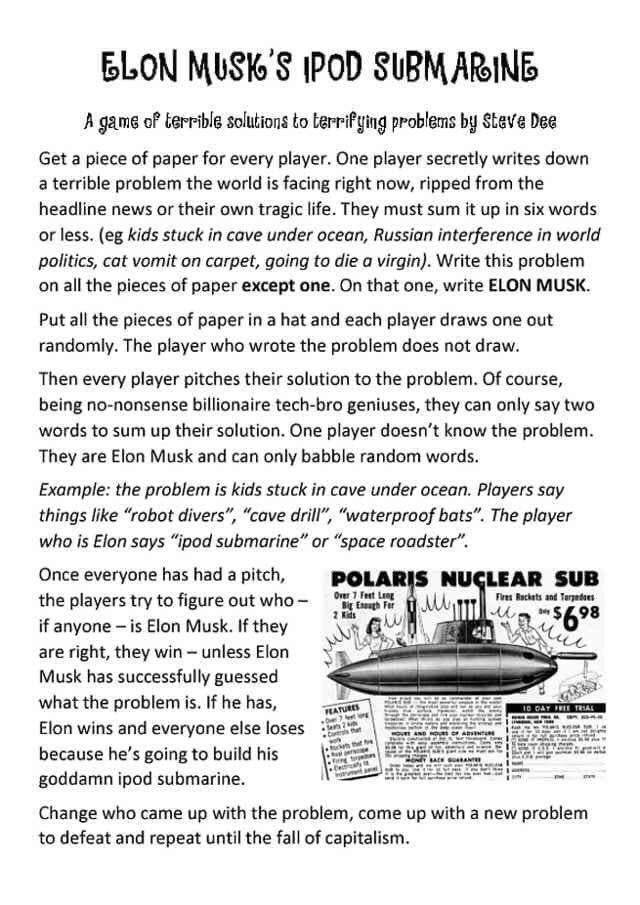
On the side I’m a collaborative tabletop & story game designer, and I really appreciate elegant simple games. Just ran across this very topical party game “Elon Musk’s iPod Submarine” that I quite admire: https://twitter.com/tinstargames/status/1017660844048506880
Sat Jul 14 04:04:33 +0000 2018
Here is a blast from the past. I’ve posted my old free one-page “Monster Smash” tabletop monster battle game from 1994-2001. All you need is some PlayDoh! At one point you could not go to a Bay Area game conv without smelling PlayDoh in the morning 😎 https://github.com/ChristopherA/MonsterSmashGame2001
Sat Jul 14 04:57:10 +0000 2018
Inspired by this simple game from @tinstargames I’ve found my once popular 1-page Play-Doh monster game “Monster Smash” and have posted it on my github https://twitter.com/ChristopherA/status/1017996401651793921
Sat Jul 14 04:59:53 +0000 2018
Some of my favorite photos of “Monster Smash” games circa 2001.
Sat Jul 14 05:12:59 +0000 2018
Replying to @lopp
I personally like the coldti — I don’t use the screws, and you’ve shown me another reason to avoid them.
Sat Jul 14 17:56:36 +0000 2018
RT @darrello: Allowing ME to own MY digital identity means that you can focus on our relationship. (not being hacked, losing my account inf…
Sat Jul 14 18:09:10 +0000 2018
RT @kimdhamilton: I’ll be speaking about Decentralized Identifiers and Verifiable Credentials at a webinar July 24 with a great lineup of s…
Sat Jul 14 20:11:02 +0000 2018
RT @MeeplesTogether: A #FridayQuestion — what was you first co-op board game and what did you think of it?
Sat Jul 14 20:11:53 +0000 2018
Replying to @Appelcline and @MeeplesTogether
My first co-op tabletop game was the old first edition of #ArkhamHorror. I’d just moved to California & fell into a crowd of Call of Cthulhu RPGer’s that played it when the GM was busy. I loved the way the players competed against the board rather than each other.
Sat Jul 14 20:18:44 +0000 2018
Replying to @clifton_r and @hasufl
I thought that was called Lamarkian Poker. https://boardgamegeek.com/boardgame/3270/lamarckian-poker
Sun Jul 15 17:53:53 +0000 2018
Replying to @tim_bansemer
Definitely a topic I have some expertise with. However, I’ve found many people from blockchain communities have simplistic or naive knowledge. In particular when I hear words “voting” or “majority” it often means they don’t truly understand 25+ century history of democracy.
Sun Jul 15 18:05:08 +0000 2018
Replying to @tim_bansemer
At this point I focus on conferences that are more interactive such as design workshops, open space, socratic roundtables, etc. rather than “sage on stage” events. I will speak at other conferences, but only at minimum if expenses covered.
Sun Jul 15 18:09:09 +0000 2018
Replying to @2357_is_prime and @brian_trollz
I call it poor man’s secret sharing. Not as secure, but doesn’t require a computer to deconstruct or construct.
Mon Jul 16 00:08:27 +0000 2018
Replying to @midmagic, @CryptoPietje, @KBryanW and @brian_trollz
There is a lot of research that that multiple-party secret sharing splits are not very resilient as psychologically the other parties don’t take the care for their other’s shares like they do with their own. But for a single person secret sharing splits can increase resilience.
Mon Jul 16 00:11:28 +0000 2018
Replying to @matthew_d_green, @oerdnj and @julian24
This is definitely one of the sub-goals of #RebootingWebOfTrust.
Mon Jul 16 03:36:14 +0000 2018
RT @isislovecruft: really enjoy that the boringSSL puts x509 in the “decrepit” directory along with RSA, DES, and RC4 https://t.co/A5MPYF22…
Mon Jul 16 04:03:44 +0000 2018
Replying to @datarade
Too hot, too humid.
Mon Jul 16 04:09:09 +0000 2018
RT @kanzure: “Decentralized certificate authorities” https://arxiv.org/pdf/1706.03370.pdf
Mon Jul 16 04:19:09 +0000 2018
I’m somewhat skeptical about Harberger taxes—likely too simplistic, but what’s important is chance to try it out “Perhaps it is just another naive theory that doesn’t work in practice. Opting in to these experiments on blockchains will allow us to study and understand it better.” https://twitter.com/simondlr/status/1018434802498916353
Mon Jul 16 06:28:19 +0000 2018
Replying to @FrayJoker and @tinstargames
A testimonial!
Mon Jul 16 17:35:47 +0000 2018
There is still some interest in at least a one-day salon on sidechains if not quite critical mass a full design workshop — for the latter we need to seek sponsorships.
Tue Jul 17 00:50:29 +0000 2018
This podcast from “The Hidden Brain” called “The Edge Effect” explains many of my life choices. I like living, working & collaborating on the edges between ecosystems, businesses, cultures & disciplines. I find it empowers me to be wiser & more creative. https://itunes.apple.com/us/podcast/hidden-brain/id1028908750?mt=2&i=1000415111324
Tue Jul 17 21:53:39 +0000 2018
Great slides on the privacy challenges to prevent correlation in the publication of large datasets. #anonymity #deanonymity. https://twitter.com/SarahJamieLewis/status/1007396185156431872
Wed Jul 18 07:19:38 +0000 2018
Our biggest fans this week: @skinnylatte, @Steven_McKie, @BobSummerwill. Thank you! via https://sumall.com/thankyou?utm_source=twitter&utm_medium=publishing&utm_campaign=thank_you_tweet&utm_content=text_and_media&utm_term=d0ab6b00ad990b36d99f7a0b
Wed Jul 18 16:01:43 +0000 2018
RT @Drabiv: @ChristopherA Interesting concept. I think it can be used in narrow settings - auctions to rent radio waves specters or somethi…
Wed Jul 18 20:23:28 +0000 2018
RT @NickThaGreek: Here is my article on Self Sovereign Identity (SSID) looking at the need for it, and some projects tackling this problem,…
Wed Jul 18 23:19:29 +0000 2018
Replying to @NickThaGreek and @el33th4xor
We are also in the process of having the community review and update my original principles (now a little over two years old) to be hopefully released this fall after the next #RebootingWebOfTrust. Currently in review of principal #2 “Control”. https://github.com/WebOfTrustInfo/self-sovereign-identity/issues
Wed Jul 18 23:23:40 +0000 2018
RT @ChristopherA: @NickThaGreek @el33th4xor We are also in the process of having the community review and update my original principles (no…
Wed Jul 18 23:23:53 +0000 2018
RT @mattblaze: @KimZetter I’ve said it before, I’ll say it again. In the more than quarter century I’ve been doing computer security, I’ve…
Wed Jul 18 23:25:17 +0000 2018
RT @dksf: 5/ HODLers and miners each contribute varying amounts of value to the network, but we remain with an underprovision of developer…
Thu Jul 19 08:56:57 +0000 2018
RT @dksf: 6/ It’s so acute that many people who might have the talent and energy to contribute to Bitcoin development have chosen to 1) lau…
Thu Jul 19 08:57:04 +0000 2018
Replying to @rawtxapp, @mejoshuaphilips, @naval, @real_vijay and @dksf
The lesson of HeartBleed. I was co-author of TLS in 90s. By 2014 #1 security protocol protecting trillions of commerce, with one open source implementation used by 60% of the Internet. Being supported by one engineer 1/4 time, leading to critical security bug from 2012 not found.
Thu Jul 19 09:12:09 +0000 2018
Replying to @pierre_rochard, @Bill_Cherman, @saifedean, @mejoshuaphilips, @naval, @real_vijay, @dksf and @bitstein
One area I’m working on to support #BlockchainCommons is to ask (or get customers to demand) that qualified custodians to demonstrate support for internet & blockchain infrastructure. If 10+ basis points are for fiduciary protection, 1 basis can be for infrastructure.
Thu Jul 19 15:39:49 +0000 2018
RT @ChristopherA: @rawtxapp @mejoshuaphilips @naval @real_vijay @dksf The lesson of HeartBleed. I was co-author of TLS in 90s. By 2014 #1 s…
Thu Jul 19 15:46:15 +0000 2018
RT @ChristopherA: @pierre_rochard @Bill_Cherman @saifedean @mejoshuaphilips @naval @real_vijay @dksf @bitstein One area I’m working on to s…
Thu Jul 19 15:46:20 +0000 2018
Replying to @pierre_rochard, @Bill_Cherman, @saifedean, @mejoshuaphilips, @naval, @real_vijay, @dksf and @bitstein
https://twitter.com/christophera/status/988867015535456256?s=21
Thu Jul 19 15:46:30 +0000 2018
Replying to @pierre_rochard, @Bill_Cherman, @saifedean, @mejoshuaphilips, @naval, @real_vijay, @dksf and @bitstein
https://twitter.com/christophera/status/988856246349508609?s=21
Thu Jul 19 15:48:00 +0000 2018
Replying to @pierre_rochard, @Bill_Cherman, @saifedean, @mejoshuaphilips, @naval, @real_vijay, @dksf and @bitstein
https://twitter.com/markfriedenbach/status/988880753504092160?s=21
Thu Jul 19 15:48:42 +0000 2018
Replying to @pierre_rochard, @Bill_Cherman, @saifedean, @mejoshuaphilips, @naval, @real_vijay, @dksf and @bitstein
https://twitter.com/waynevaughan/status/988896811753455616?s=21
Thu Jul 19 15:49:41 +0000 2018
RT @notgrubles: This is incredibly comprehensive and very cool.
@ChristopherA and @Appelcline’s “Learning Bitcoin From The Command Line”…
Fri Jul 20 22:34:18 +0000 2018
Replying to @notgrubles and @Appelcline
Have some plans for a number of updates including teaching how to configure for Blockstream satellite, more Scripts, wallet primitives from libwally-core https://github.com/ElementsProject/libwally-core, and c-lightning https://github.com/ElementsProject/lightning. Right now mostly C & C++ oriented, but may add more Python.
Fri Jul 20 22:39:29 +0000 2018
RT @kimdhamilton: In which our DID heroes discuss the perils of a perfectly correct roadmap, being burned as witches. Outtakes to follow ht…
Sat Jul 21 07:33:33 +0000 2018
Cantillon Effect: “the first ones to receive the newly created money see their incomes rise whereas the last ones to receive the newly created money see their purchasing power decline” I believed this for a while but did not have a name for it. #inequality https://mises.org/library/how-central-banking-increased-inequality
Sun Jul 22 18:21:30 +0000 2018
Replying to @saifedean
I think a great place to start in learning about Austrian Economics, if you don’t have a lot of background, is the CC-BY textbook “Lessons for a Young Economist”. Very accessible, with a solid pedagogy, and also the separate teacher’s guide is very good. https://mises.org/library/lessons-young-economist
Sun Jul 22 18:41:11 +0000 2018
RT @ChristopherA: @saifedean I think a great place to start in learning about Austrian Economics, if you don’t have a lot of background, is…
Sun Jul 22 18:41:15 +0000 2018
RT @SFBitcoinDevs: Video from @pwuille’s talk on Taproot, Schnorr and SIGHASH_NOINPUT is now available https://youtu.be/YSUVRj8iznU
Sun Jul 22 18:53:43 +0000 2018
RT @alexbosworth: An aspect of paying miner fees is that your fees may go to miners you don’t like. With LN wallets, you could voluntarily…
Sun Jul 22 18:56:23 +0000 2018
Replying to @DTFinegood, @yaneerbaryam and @ricardo_hausman
Any link to the slides?
Sun Jul 22 18:58:38 +0000 2018
🗝💬“The city supports those who are different, because you’re anonymous…facial recognition will be in support of more conformist behavior. It will be harder to be different, unless you…really, really embraces diversity and difference.” https://medium.com/s/futurehuman/how-facial-recognition-tech-could-tear-us-apart-c4486c1ee9c4?source=email-63ba9be92e8f–mktgemail.human
Mon Jul 23 16:34:05 +0000 2018
Unfortunately facial recognition & biometrics are here to stay. As a culture we must resist associating it with data. Instead it should only be used as one of many factors for authentication of cryptographic identifiers, which people then can choose to consent to release data.
Mon Jul 23 17:13:03 +0000 2018
Apple comes closest to having this right with the fingerprint reader on the iPhone 6-8. The device never shares the biometric, only unlocks keys under the users control, after the implied consent of the use of the correct finger. Use wrong finger 3 times & password is required.
Mon Jul 23 17:18:46 +0000 2018
The iPhone X is not quite as good, as someone else holding the iPhone to your face will authenticate unlocking the of the keys. Ability to force requiring a password by holding either volume button & the side button is insufficient as the phone may be coerced away from you.
Mon Jul 23 17:24:36 +0000 2018
In both cases I would personally prefer Apple enable multifactor (both biometric AND password) if the iPhone has moved since the last time it was authenticated, or only in places marked as “safe” like your home. Other recent history can be used as additional factors.
Mon Jul 23 17:32:54 +0000 2018
A solution for services such as Facebook that have large number of stored images are much harder. They need to firewall the facial identifier from the data about individuals. This requires more than “can correlate photos of faces with data” consent by their users.
Mon Jul 23 17:38:01 +0000 2018
In a self-sovereign architecture a future competitor to Facebook would lock the face correlated data behind keys they don’t control, but are under control of their users, that must be consented to for each unique use, not a blanket permission.
Mon Jul 23 17:40:42 +0000 2018
I don’t know of any way to prevent misuse of facial, voice & other biometric information—other than as a culture we must demand it not be abused. China’s use of facial recognition to control against dissent is precisely the anti-pattern we need to avoid.
Mon Jul 23 17:43:53 +0000 2018
RT @apowers313: This is one of the reasons that @FIDOAlliance established Privacy Principles early – to make sure biometrics never leave a…
Mon Jul 23 17:44:18 +0000 2018
Replying to @rabbyte
👍👏
Mon Jul 23 17:44:59 +0000 2018
RT @ixo_impact: “Global Single Sign-on!” by @CedricFranz https://medium.com/ixo-blog/global-single-sign-on-a25e14c38740
In this blog Cedric talks about #RebootingWebOfTrust and…
Mon Jul 23 19:15:27 +0000 2018
RT @MeeplesTogether: Meeples Together isn’t just about game design, but also COOPERATIVE design. One of the foundations of that was @Christ…
Mon Jul 23 19:15:42 +0000 2018
Replying to @xpost1
Absolutely possible, given a variety of trustless decentralized services that can act as your agent when you are offline. You’d likely use a decentralized data store like IPFS, something like lightning network’s idea of “watchtowers” & other related services.
Mon Jul 23 20:49:18 +0000 2018
RT @GuyZys: Great read on privacy-preserving computations paradigms such as MPC, TEEs and Zero-Knowledge Proofs “Privacy and secrecy: a gen…
Mon Jul 23 21:01:04 +0000 2018
Replying to @GuyZys and @AAAinsley
Nice article. I tend not to use the word privacy like you do, due to the problems I raise in The Four Kinds of Privacy http://www.lifewithalacrity.com/2015/04/the-four-kinds-of-privacy.html — instead I use the word confidentiality.
Mon Jul 23 21:03:51 +0000 2018
Replying to @eordano
There are interesting data minimization & selective disclosure technologies emerging to help (zkp, blinding & confidential credential/attribute, etc) Here is a draft of an overview on these from #RebootingWebOfTrust now moving onward to W3C Credentials CG https://github.com/w3c-ccg/data-minimization/blob/master/README.md
Mon Jul 23 23:02:02 +0000 2018
Good overview of some approaches to confidentiality via zkp, etc. Agree 👍“Second, and more important: there is no silver bullet. Allow me to repeat that. There is no silver bullet. No one answer, no one technique, completely solves the privacy problem.” https://medium.com/@leor.fishman/privacy-and-secrecy-a-general-analysis-f39dcd6a709f
Mon Jul 23 23:10:17 +0000 2018
This satirical page is actually useful as a list of anti-patterns to avoid in writing secure code. I’d love to see added to it anti-patterns about writing code that is vulnerable to side-channel attacks. https://www.owasp.org/index.php/How_to_write_insecure_code @pwuille #sfbitcoindevs @hashbreaker @ASayakkara
Tue Jul 24 03:24:52 +0000 2018
In our W3C Credentials CG https://w3c-ccg.github.io VoIP/IRC meeting tomorrow at 9am PT 12ET https://lists.w3.org/Archives/Public/public-credentials/2018Jul/0047.html we will be discussing the “Amira 1.0.0 User Story: A Self-Sovereign Web of Trust Engagement Model of an Immigrant Software Engineer” Join us! https://github.com/WebOfTrustInfo/rebooting-the-web-of-trust-fall2017/blob/master/final-documents/amira.md
Tue Jul 24 06:04:13 +0000 2018
Thinking about security properties of an iPad Mini WiFi-only with iTouch, vs a Ledger. Both can be air-gapped, iPad has camera & display but Ledger requires USB to communicate. Both have hardware randomness. Both have to release a key from HSM for transaction to be signed. …
Tue Jul 24 22:15:13 +0000 2018
Both have some tamper resistance w/ hardware assurance of OS. Both require signed apps to be loaded. Both are not open source HSM. Unfortunately iPad’s iTouch biometric is not useful in this case as password is required first to enable it. Ledger fits better in safe-deposit box.
Tue Jul 24 22:33:06 +0000 2018
iPad Touch has similar properties and fits in safe deposit box, but I’m not sure if it has true HSM like the iTouch iPad.
Tue Jul 24 22:35:28 +0000 2018
Replying to @kragen
Ledger requires a laptop which like the iPad has a wide variety of attack surface complications.
Tue Jul 24 22:39:50 +0000 2018
Replying to @boscolochris
A ledger without a laptop is useless. Both have a lot of code in involved.
Tue Jul 24 22:42:01 +0000 2018
Replying to @Leon_Vandenberg
I can store things into the Secure Enclave of a iPad using the keychain API. And if it is air-gapped with Wi-Fi off in a bank vault it may be pretty close in actual security. It is just a thought exercise.
Tue Jul 24 22:45:53 +0000 2018
Replying to @rm0rf and @Leon_Vandenberg
Just as a thought experiment isn’t any management engine effectively off if air-gapped in a bank vault? And there is no baseband on a Wi-Fi only iPad. I don’t trust baseband chips but I do feel like I can turn off Wi-Fi, or even disable antenna.
Tue Jul 24 22:51:00 +0000 2018
In this thought experiment I would load up transaction input on my iPhone, go to vault, use QR code to send unsigned transaction to iPad (or iPod Touch), it would QR code signed transaction back, which I would leave bank vault with my iPhone to send once outside.
Tue Jul 24 22:55:41 +0000 2018
Replying to @kragen
No NFC in iPad. Why disable speaker?
Tue Jul 24 23:07:09 +0000 2018
Replying to @rm0rf and @Leon_Vandenberg
I’m more concerned about the management engine of every modern laptop today over the custom chip Apple uses.
Tue Jul 24 23:08:51 +0000 2018
Replying to @kragen
I agree — I’d love to have a cheap RISC-V device with camera & small screen with open boot and the simplest HSM or even better an HSM that can sign secp256k1 on enclave. All open source and open patent. Critical path is costs of production of that chip.
Tue Jul 24 23:13:19 +0000 2018
Replying to @kragen
Perfection is the enemy of the good. I am presuming that the iPad and software was secure when put into the bank vault. I mainly don’t want it to be corrupted once it is in there. I doubts the efficacy of attacking a previously secure device using audio.
Tue Jul 24 23:17:33 +0000 2018
I would likely have to leave a charger in the bank vault with the iPad because otherwise bringing in a power source to recharge the battery from outside might be an avenue for compromise.
Tue Jul 24 23:22:04 +0000 2018
Replying to @Leon_Vandenberg and @rm0rf
If that is true than likely the Ledger is insecure too. The chip is a made state sponsored (France-EU) chip company. Worthy to consider nationstate adversaries, however it is impractical to do anything about it until we have our own RISC-V fabs.
Tue Jul 24 23:29:40 +0000 2018
Replying to @BitcoinAlley
My original thought was iPod Touch because it could fit in safe-deposit box, but there was a significant upgrade to hardware security module (HSM) in the biometric devices like iPad with iTouch. But I suspect HSM even in iPod Touch may be better than Ledger’s HSM.
Wed Jul 25 00:06:54 +0000 2018
Replying to @kragen
Possibly but I’m unclear on firmware upgrade architecture. https://www.st.com/content/ccc/resource/technical/document/user_manual/34/1a/20/75/7f/84/45/cb/CD00208802.pdf/files/CD00208802.pdf/jcr:content/translations/en.CD00208802.pdf
Wed Jul 25 00:12:32 +0000 2018
Replying to @kragen
Interestingly, there may be some secp256k1 support. I don’t think it is on spec sheet. https://github.com/mogorman/microecdsa
Wed Jul 25 00:14:04 +0000 2018
RT @trbouma: Note to self: Ensure these requirements and considerations are in all #digitalidentity #POC and #RFP (thx to @kimdhamilton ) h…
Wed Jul 25 17:23:17 +0000 2018
Replying to @MadBitcoins and @BitcoinAlley
It is somewhat harder to pown a Mac. Changing Apple password and resetting all devices should be enough. Here is a helpful page: https://support.apple.com/en-ca/HT204145
Fri Jul 27 04:03:09 +0000 2018
RT @trevortimm: ACLU took Amazon’s facial recognition tech—which Amazon is aggressively selling to police—and loaded it with 25,000 mugshot…
Fri Jul 27 04:43:08 +0000 2018
RT @rusty_twit: My new workspace is ready! Thanks @phneep !
Fri Jul 27 05:20:00 +0000 2018
🤷🏻♂️“Funny how we talk about link rot when it appears we now also have tld rot” https://blog.benjojo.co.uk/post/the-death-of-a-tld
Fri Jul 27 05:33:49 +0000 2018
RT @MicroSFF: “Dad, there’s a monster under my bed!”
“Yes, the bed they used to live under has been razed.”
“But it’s a monster!”
“Maybe, b…
Fri Jul 27 05:49:28 +0000 2018
RT @trbouma: This is a great resource.
With that, I revise my long-standing saying: ‘ If you truly want to understand something, you have…
Fri Jul 27 13:26:28 +0000 2018
Replying to @BitcoinAlley and @MadBitcoins
It feels doubtful that they could attack his Droid’s firmware remotely but I’m less knowledgeable here. Should be good enough to reset to factory.
Fri Jul 27 13:29:30 +0000 2018
Replying to @Drabiv
Self-Sovereign Identity doesn’t mean that you are in complete control (for instance an ancient King has total sovereignty). But it does define the borders within which you (the self) can make sole decisions and outside of which you negotiate with others (other selves), as peers.
Fri Jul 27 17:32:00 +0000 2018
RT @GETJolocom: Locking the Web open! discussing #identity at #DWebSummit w/ @csuwildcat @kimdhamilton @IdentityWoman @peacekeeper @rh7 @Ch…
Fri Jul 27 17:36:03 +0000 2018
Replying to @Drabiv
Exactly — self-sovereign identity is bounded. BTW, I’m hoping to get some dialogue going on this topic in our upcoming update to the 10 Principals of Self-Sovereign Identify — Principal #2 “Control”: https://github.com/WebOfTrustInfo/self-sovereign-identity/issues
Fri Jul 27 18:15:20 +0000 2018
RT @Drabiv: Self-Sovereign Identity is self-controlled, but bounded by other “selfes-“ - peers in relationships. https://twitter.com/ChristopherA/status/1022908310016552960
Fri Jul 27 18:25:40 +0000 2018
Replying to @Drabiv and @NZN
This is close to heart of Self-Sovereign Identity Principal #1 “Existence: Existence. Users must have an independent existence” — however the issue discussion on this is more complex. Is it a fundamental human right/dignity or one of property/ownership? https://github.com/WebOfTrustInfo/self-sovereign-identity/issues/6
Fri Jul 27 19:22:25 +0000 2018
Replying to @NZN, @Drabiv and @NZN
I would appreciate some discussion of this in issue #6 as we somewhat reached an impass moving forward on update of Principle #1 of Self-Sovereign Identity. Some reconciliation might help @NSmolenski get back involved. https://github.com/WebOfTrustInfo/self-sovereign-identity/issues/6 @JoeAndrieu
Fri Jul 27 20:37:47 +0000 2018
🗝💬“Going private is a way of proving you can win without catering to the masses. It means you have a highly engaged, highly specific audience, and you can make niche content just for them”. This closed/open group dynamic seems to switch every few years. https://www.wired.com/story/is-a-meme-born-in-a-private-account-still-a-meme
Fri Jul 27 20:47:01 +0000 2018
👍👏“I strongly advise against using one of these devices. While Bitfi is perhaps not an outright scam, the design is inferior to that of hardware wallets where the device really is needed (or the backup of the seed) along with the passphrase in order to spend the coins.” https://twitter.com/ryancdotorg/status/1022870589973848066
Fri Jul 27 20:50:50 +0000 2018
Replying to @Dwyndal
As cryptocurrency hardware wallets Trezor & Ledger both have different security tradeoffs. I lean in direction of Ledger, but there are good arguments the other way. Both are good. Once @Coinkite is out I may change my mind.
Sat Jul 28 00:27:10 +0000 2018
Replying to @RawMaterialNYC and @Bitfi6
I respectfully disagree. With 30+ years of cryptographic experience & as co-author TLS, brainwallets will always be inferior as cryptographic seeds as they all have insufficient randomness. You may be able to temporarily mitigate through some obscurity in code, until POOF!
Sat Jul 28 01:11:52 +0000 2018
Replying to @Dwyndal and @Coinkite
Opendime isn’t a wallet, it is a bearer instrument. Different security requirements. Once funded it is equivalent to a paper wallet in a lockbox—both with possession can be stolen easily. Good Opendime scenarios are that you can give someone a lockbox before putting money in it.
Sat Jul 28 01:17:55 +0000 2018
👍 Great thread on Information Theory from the fundamentals of Shannon’s Law to limits on human & cultural management of complexity. Thought he was going to lead to PoW & blockchain as a form of pocket against entropy, but still relevant to our community. https://twitter.com/Kpaxs/status/947516453691052034
Sat Jul 28 02:49:06 +0000 2018
#Privacy “different browsers understand…consent around WebRTC differently https://ntblk.github.io/webrtc-privacy/.…when you deny or give permission on Chrome, Firefox or Safari. You’ll notice…Safari will not display your private IP address if you do not give consent” https://www.article19.org/resources/privacy-and-consent-in-the-age-of-browsers-the-question-of-webrtc/
Sat Jul 28 18:45:12 +0000 2018
RT @ACLU: Here’s what happened when we tested @Amazon’s facial recognition tool on members of Congress. (Spoiler alert: it didn’t go well)…
Sat Jul 28 18:46:45 +0000 2018
A walk through of details of how India’s #Aadhaar digital identity system is so flawed. The key problem is identifiers and the proof of their authenticity MUST be kept separate from authorization. The W3C DID architecture does this in a non-centralized way under user control. https://twitter.com/nileshtrivedi/status/1023196004911263744
Sun Jul 29 17:24:34 +0000 2018
Some key quotes from the thread: https://twitter.com/nileshtrivedi/status/1023203478494052352
Sun Jul 29 17:26:01 +0000 2018
Another key quote: https://twitter.com/nileshtrivedi/status/1023203009201762304
Sun Jul 29 17:32:55 +0000 2018
RT @nic__carter: The latest from @hasufl and myself: Visions of Bitcoin
https://medium.com/@nic__carter/visions-of-bitcoin-4b7b7cbcd24c
Sun Jul 29 22:59:45 +0000 2018
Text by @CassSunstein, a leader on “nudge” behavioral economics. In particular I find it a beginning of a model for thinking about ethics of intervention when seduced by cognitive bias. One issue of concern to me is question at end “Best…if choice architects cannot be trusted” https://twitter.com/CassSunstein/status/1023702974965706752
Sun Jul 29 23:34:58 +0000 2018
When I taught “Using the Social Web for Social Change” in a sustainable MBA program we also talked about the ethics of using behavioral economics “nudge” interventions. I didn’t realize then but see now that untrustworthy “choice architects” are actively attacking our systems.
Mon Jul 30 00:05:27 +0000 2018
Replying to @ChrisDiehl and @CassSunstein
I see it the struggle in the Final Words section “When people lack antecedent preferences or when those preferences are not firm, and when an intervention constructs or alters their preferences, the ‘as judged by themselves’
standard is more difficult to operationalize”.
Mon Jul 30 00:45:31 +0000 2018
Replying to @ChrisDiehl and @CassSunstein
What we needed in this discipline are more frank discussions about identifying, challenging & overcoming bad actor “choice architects”. I think the concept of “trustless” and other mechanism design approaches are a start, but they too have risks if they assume rational actors.
Mon Jul 30 00:51:22 +0000 2018
RT @ChrisDiehl: @ChristopherA @CassSunstein More recently I struggle to support nudging when that, in my mind, cedes power to a centralized…
Mon Jul 30 01:01:02 +0000 2018
RT @asglidden: There’s probably a bunch about the mechanics of this I haven’t really thought through - it’s a very rough idea. But it’s an…
Mon Jul 30 01:02:33 +0000 2018
RT @el33th4xor: This should be periodic reading for anyone working on open source software. https://twitter.com/esesci/status/1023765396879364096
Mon Jul 30 05:49:29 +0000 2018
RT @agkrellenstein: SgxPectre Attacks: Stealing @Intel Secrets from #SGX Enclaves via Speculative Execution
Mon Jul 30 05:56:58 +0000 2018
RT @o0ragman0o: @fs0c131y This was my talk contrasting #Aadhaar with #SelfSovereignIdentity given in India (at what turned out to be an Acc…
Mon Jul 30 18:47:22 +0000 2018
I think it is important for us to examine “Game Theory (+behavioral economics, memetic engineering, etc) as a Dark Art” as these practices are emerging and risk the good that is possible with these approaches. https://twitter.com/RhysLindmark/status/1023657025648119808
Mon Jul 30 19:30:28 +0000 2018
Replying to @JAlanHenning, @Appelcline and @MeeplesTogether
Shannon has many more books in the hopper, but together we are about 1/3rd through a book on the patterns of cooperative play, which includes RPGs, improv, jazz, children’s play, etc. Some of it was in first draft of Meeples Together but pulled out as it was less focused.
Tue Jul 31 14:09:17 +0000 2018
Replying to @_PoTeaD, @trbouma and @konklone
When I wrapped up my work on TLS 1.0 nineteen years ago I would have never guessed it would take so long to upgrade. Personally I’d prefer to move to a no-legacy TLS 1.3.
Tue Jul 31 15:15:18 +0000 2018
Our 7th(!) #RebootingWebOfTrust Design Workshop will be in Toronto on September 26-28th. Over 37 whitepapers, specs and POCs collaboratively created at previous events. Join us to create the future of human-rights decentralized & self-sovereign identity! http://rwot7.eventbrite.com
Tue Jul 31 17:17:51 +0000 2018
RT @Appelcline: I’ve been the editor-in-chief for #RebootingWebofTrust for almost three years now. That’s a lot of intriguing papers on int…
Wed Aug 01 01:16:18 +0000 2018
RT @jmartinez_43: In my latest post, I discuss how losing a twitter beef against @francispouliot_ led me to question what decentralization…