This is one of a number of bitcoin wallet interoperability proposals that @BlockchainComns is facilitating—if you are a bitcoin wallet vendor & want join in these discussions, let me know. Mostly focused now on seed, shard, and PSBT intern via QRs, but topics are broader! https://twitter.com/BitcoinLixin/status/1278264348230606849
Wed Jul 01 17:37:18 +0000 2020
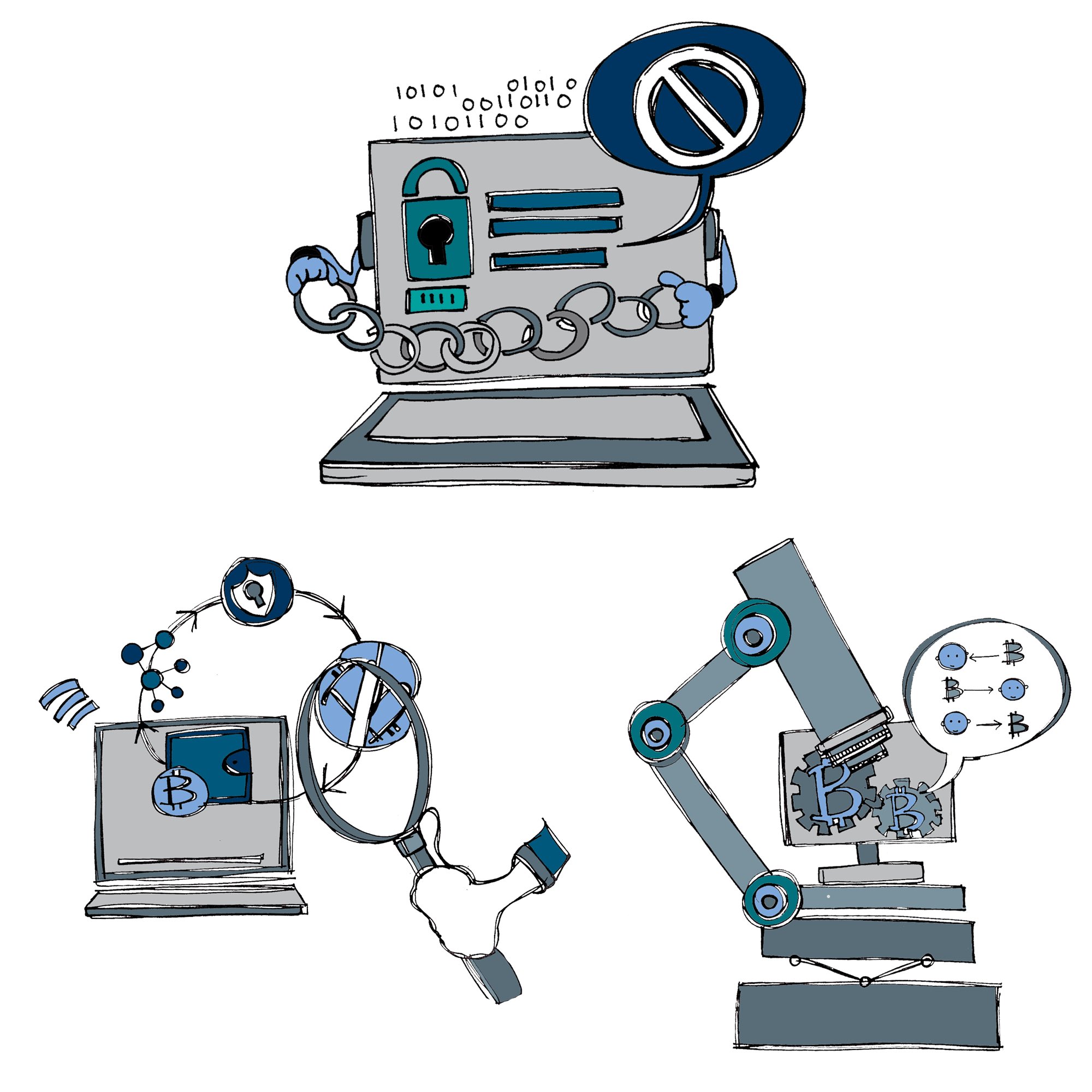
One of our @BlockchainComns interns @cmurray17 needs a good name for his project. Long-term Goal: DECENTRALIZE BITCOIN PRICE DISCOVERY. Focus now is to openly aggregate price data across many exchanges, minimizing the need to trust third party website, all served over Tor. Ideas?
Wed Jul 01 17:51:22 +0000 2020
Replying to @dstadulis, @BlockchainComns and @CMURRAY17
There is a difference between the short-term goal (code that be hosted near your own self-sovereign full node that can collect price information from various parties for you), and the longer term goal of how you might be able to cooperate with others to share price info securely.
Wed Jul 01 18:33:54 +0000 2020
Replying to @dstadulis, @BlockchainComns and @CMURRAY17
Part of the challenge is how you can locally measure various factors of trust but also share them. I may have a REST feed to my personal favorite exchange, which is relatively high trust but also an attack surface or DOS. I’d like to discover if others like me have same price. …
Wed Jul 01 18:38:40 +0000 2020
Replying to @dstadulis, @BlockchainComns and @CMURRAY17
However, that data from “others like me” is not as trustable individually as I’m getting them 2nd hand. However, in aggregate, they may be more trustable than even my trusted local REST feed. We also need to look at potential systemic network attacks to avoid. …
Wed Jul 01 18:41:38 +0000 2020
Replying to @dstadulis, @BlockchainComns and @CMURRAY17
Separately, I’d like to have local storage of price history, but it has a different security requirements, and we need to be careful and not conflate those requirements with the security requirements for current price.
Wed Jul 01 18:43:32 +0000 2020
Replying to @dstadulis, @BlockchainComns and @CMURRAY17
Interesting to me about this project is its relationship with other peer trust issues—like the web of trust that PGP tried to offer individuals, those old approaches never quite scaled. However, this is a nice subset of that problem: How much can I trust my peers price data?
Wed Jul 01 18:52:01 +0000 2020
Replying to @CMURRAY17, @dstadulis and @BlockchainComns
Sorry, I used a Telegraph @ instead of a Twitter one. Sorry for the noise!
Wed Jul 01 19:23:19 +0000 2020
Our intern’s correct Twitter handle is @filial_crypto. The other was a name space collision with Telegram.
Wed Jul 01 20:59:30 +0000 2020
Replying to @oscpacey, @dstadulis and @BlockchainComns
Sill looking for a good name for @fillial_crypto’s project. LocalQuote & PriceWeb feel a bit too generic, or a place to get a quote for plumber or online groceries. @kanzure suggested PriceBleed, which may be a better name for the larger project, or a name for an attack on it ;-)
Wed Jul 01 21:06:10 +0000 2020
RT @ChristopherA: @oscpacey @dstadulis @BlockchainComns Sill looking for a good name for @fillial_crypto’s project. LocalQuote & PriceWeb f…
Wed Jul 01 21:06:35 +0000 2020
#SmartCustody Adversary — Legal Forfeiture
The first adversary in our category of “Loss by Government” is LEGAL FORFEITURE. This adversary simply suggests that your government could use entirely legal means to take your cryptocurrency from you. (1/8)
Wed Jul 01 22:27:48 +0000 2020
The thing is: you can’t really avoid this. If you’re living in a society, you agreeing to abide by its rules. If you try and keep your funds from legal acquisition, then you could be thrust from that society. (3/8)
Wed Jul 01 22:27:49 +0000 2020
Child support. Slip-and-fall lawsuits. Fines for breaking the law. These are all possibilities. You could end up owing money, and the government is getting increasingly good at finding digital assets. (2/8)
Wed Jul 01 22:27:49 +0000 2020
The problem of course arises if your state has corrupt motives. (Or if some other person manipulates the legal system for corrupt motives of their own) And again, defending against this is difficult. (4/8)
Wed Jul 01 22:27:50 +0000 2020
This is why in our best practices shared in our #SmartCustody you check up on your bank safe-deposit boxes every six months! We recommend spring around April 15th (tax day), and in autumn around November 1st (day of the dead). (6/8)
Wed Jul 01 22:27:51 +0000 2020
LEGAL FORFEITURE isn’t always obvious. California in 2007 seized bank safe-deposit boxes improperly. Currency, monetary instruments & physical good were sold, taxed, and held in trust, but all other paper was destroyed. There goes your paper wallet! https://abcnews.go.com/print?id=4832471 (5/8)
Wed Jul 01 22:27:51 +0000 2020
Have your own stories of Legal Forfeiture impacting digital assets? Your own solutions? Let us know! And please consider supporting #SmartCustody. We’re working on V2, with multi-sigs and other expansions: https://smartcustody.btcpay.blockchaincommons.com/ (7/7)
Wed Jul 01 22:27:52 +0000 2020
As with several adversaries discussed in #SmartCustody, one of the best solutions is to not make yourself a target by hiding the depth of your digital holdings. Another is to legally tangle your assets—in upcoming v2 book we’ll talk about using multisig fiduciaries to help. (7/8)
Wed Jul 01 22:27:52 +0000 2020
The first #SmartCustody adversary in category “Loss by Government” is LEGAL FORFEITURE: https://twitter.com/christophera/status/1278455292280270855?s=21 https://twitter.com/ChristopherA/status/1278455292280270855
Wed Jul 01 22:29:50 +0000 2020
Replying to @JoeAndrieu and @BlockchainComns
Hmm, both http://exchangewatch.com and http://watch.exchange are being squatted on at quite high prices. But I wasn’t aware of the .exchange domain. Possibly we use something that has synergy with that.
(Also correcting cc to @Fillial_Crypto)
Wed Jul 01 22:36:15 +0000 2020
After further analysis, base64 is still challenging to meet our full requirements for QR compression, URL compatibility (required for deep-linking by platform libraries and camera apps), etc. We are working on a proposal that may not be quite as efficient, but has a lot of +s.
Thu Jul 02 06:55:06 +0000 2020
RT @trbouma: @hackylawyER @Facebook “In other words, the architecture is the problem.”
Thu Jul 02 18:35:52 +0000 2020
Because what are you going to do? You’re just a person, and they are a country, part of the international community. You are subject to their laws and jurisdiction, and an identity without national citizenship continues to be a huge challenge to human rights. (2/13)
Thu Jul 02 21:04:08 +0000 2020
#SmartCustody Adversary — Nation-State Actor
Of the possible ways to lose your digital assets to a government, having them wielding their power as NATION-STATE ACTOR is probably the scariest. (1/13)
Thu Jul 02 21:04:08 +0000 2020
#SmartCustody is about making risks concrete through their anthropomorphization as adversaries and using that insight to determine if the risks affect you. I don’t think most people are likely to have their digital assets taken by a nation-state. (5/13)
Thu Jul 02 21:04:09 +0000 2020
But we also state: “I am hopefully bound by laws and morality: if my citizens obey the rules and don’t interact with criminals, and if I am truly a law-abiding nation, then they have nothing to worry about. I just want to keep my nation and its people safe.” (4/13)
Thu Jul 02 21:04:09 +0000 2020
As we say in our motivations: “I am the all-powerful state. I can do whatever I want to my citizens. I can surveil, I can seize. I can imprison, I can threaten. I can make their lives so awful that cryptocurrency is the least of their concerns.” (3/13)
Thu Jul 02 21:04:09 +0000 2020
The distinction between the government LEGAL FORFEITURE adversary we discussed yesterday, is that LEGAL FORFEITURE targets you as an individual, whereas with today’s NATION-STATE ACTOR adversary you are more of a bystander or a particular class of citizen or resident. (9/13)
Thu Jul 02 21:04:10 +0000 2020
And we’ve certainly seen situations where NATION-STATE ACTORS started scooping up funds almost as a side effect, such as when Argentina seized pension accounts, India banned large bills, and many examples of locking transfer of bank funds during currency devaluations. (8/13)
Thu Jul 02 21:04:10 +0000 2020
But with that said, I might also be very cautious about which nations I accessed my cryptocurrency from, because some nation-states are certainly more lawful than others, and my experiences in the USA and first world might be different from others elsewhere. (7/13)
Thu Jul 02 21:04:10 +0000 2020
Because the bottom line is, as our motivation suggests, a nation-state can do a lot worse to you than seize digital assets if it wants, and probably do much more easily than focus on seizing your digital assets. (6/13)
Thu Jul 02 21:04:10 +0000 2020
Have your own stories of Nation-States impacting digital assets? Your own solutions? Let us know! And please consider supporting #SmartCustody. We’re working on V2, with multi-sigs and other expansions: https://smartcustody.btcpay.blockchaincommons.com/ (13/13)
Thu Jul 02 21:04:11 +0000 2020
And this is the last of my two “Loss by Government” adversaries, following up on my look at LEGAL FORFEITURE yesterday (and presumably making this adversary form of illegal forfeiture). (12/13)
Thu Jul 02 21:04:11 +0000 2020
So, be careful, but also we use this adversary as an example of how you might look at a really scary problem in #SmartCustody and determine that it’s not actually one you need to worry about, or it is not worth your effort to try to mitigate. (11/13)
Thu Jul 02 21:04:11 +0000 2020
This distinction become blurry when when talk about non-nation-state governments actors, such as regions and cities. For instance, I gave the example of California seizing safety deposit boxes that were unused (by a very flaky definition of “unused”). (10/13)
Thu Jul 02 21:04:11 +0000 2020
Our last #SmartCustody adversary in the category “Loss by Government” is NATION-STATE ACTOR: https://twitter.com/christophera/status/1278796622978150400?s=21
Thu Jul 02 21:05:07 +0000 2020
RT @MeeplesTogether: The Meeples Together case studies are back! This week we looked at the traitorous co-op, Dark Moon, which is pretty…
Fri Jul 03 05:51:56 +0000 2020
RT @MeeplesTogether: One of the first cooperative tabletop games returns for a 20th anniversary edition. A real classic!
Fri Jul 03 06:13:46 +0000 2020
I appreciate this review — at @BlockchainComns we had on our road map to explore Electrum server as well. I think we are now leaning to offer a public but Tor-only Esplora service despite its much higher resource requirements. cc @lopp https://twitter.com/CasaHODL/status/1279069418392367106
Fri Jul 03 17:42:43 +0000 2020
I wish we could harmonize the APIs though. We suspect that for those who want to host their own search services that Electrum server is more practical. Our ideal is for clients to not care about backend.
Fri Jul 03 17:46:09 +0000 2020
😢“The era when the Chinese cared what others thought,” crowed Zhang Xiaoming, the deputy director of China’s Hong Kong and Macau Affairs Office, after Washington’s most recent rebuke, “is in the past, never to return.” https://twitter.com/PrivacyCDN/status/1279057549183070208
Fri Jul 03 17:50:25 +0000 2020
This is one of my greatest concerns when working with standards organizations like IETF, W3C, Oasis, ISO, etc. The big companies have substantial resources to be able to take advantage of the weaknesses that these standards processes have in trying to be fair. https://twitter.com/aniltj/status/1278865788162772995
Fri Jul 03 17:59:45 +0000 2020
RT @heathervescent: On Tuesday, July 7th, the Credentials Community Group at the W3C will have “What’s in a wallet?” part 1 (w/ @manusporny…
Fri Jul 03 21:02:53 +0000 2020
Replying to @heathervescent, @manusporny, @csuwildcat, @kylekemper and @kimdhamilton
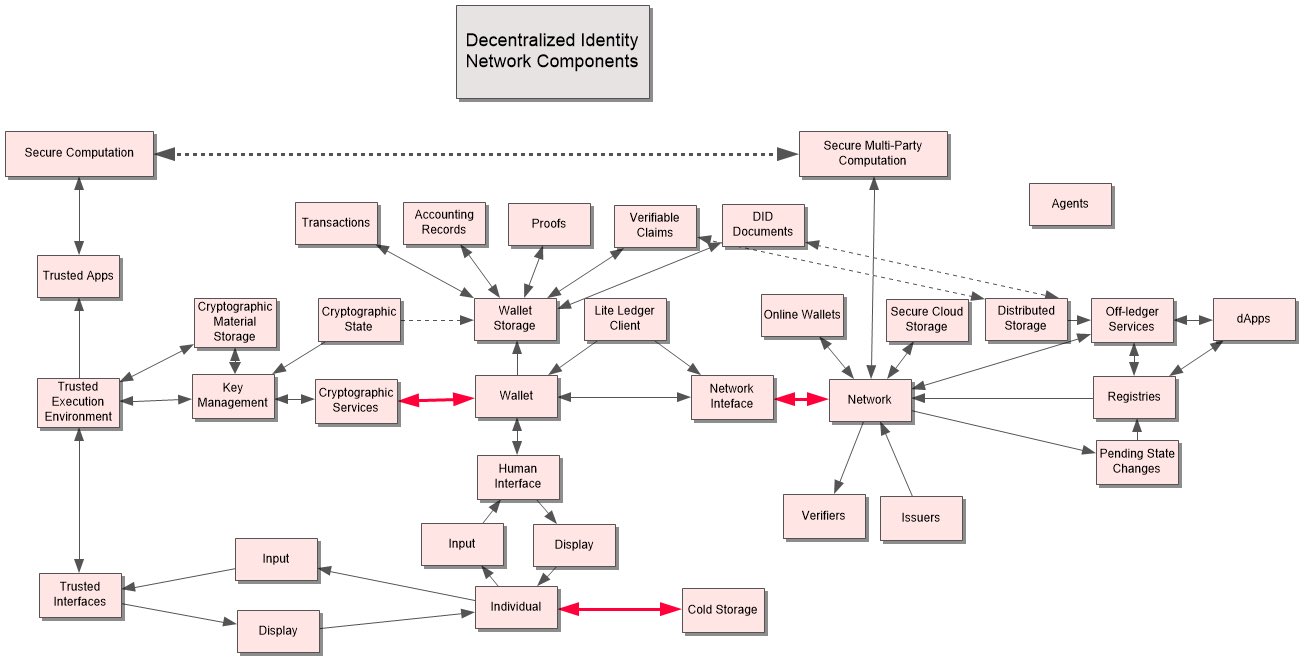
For my 5 minutes of this tallk, I’ll be sharing some thoughts and overview based on this topic paper that @JoeAndrieu and I prepared for #RWOT9 in Prague that didn’t quite get enough interest to turn into a final paper. https://github.com/WebOfTrustInfo/rwot9-prague/blob/master/topics-and-advance-readings/whats-wallet.md
Fri Jul 03 21:10:06 +0000 2020
RT @ChristopherA: @heathervescent @manusporny @csuwildcat @kylekemper @kimdhamilton For my 5 minutes of this tallk, I’ll be sharing some th…
Fri Jul 03 21:10:15 +0000 2020
We worry about thieves. We worry about the government taking our earnings. We worry about our computer crashing. But the average person who takes average precautions is most likely to just lose his keys. (2/8)
Fri Jul 03 21:29:06 +0000 2020
My free #SmartCustody book leads you through a risk modeling exercise that helps you to emotionlessly assess risks and determine what’s most dangerous to your own digital-asset holdings. But my estimate of the category most likely to cause you loss? It’s LOSS BY MISTAKES. (1/8)
Fri Jul 03 21:29:06 +0000 2020
Because in a decentralized world: there’s only you. (And the hand-picked people you select to protect your keys, its shards, and your other secrets) We will be covering each of these 5, non-traditional adversaries over the course of the next week. (7/8)
Fri Jul 03 21:29:07 +0000 2020
Decentralization is all about taking control from centralized forces, but that also gives us the responspibilities that they once held. That’s the other aspect of #SmartCustody: helping everyone to thoughtfully and methodically protect themselves. (6/8)
Fri Jul 03 21:29:07 +0000 2020
I iconify this category as a man with his head on his keyboard, weeping. And that’s the worst part of a Loss by Mistakes: it’s your fault. (5/8)
Fri Jul 03 21:29:07 +0000 2020
But there are lots of mistakes that can cost you your funds. I categorize five: Convenience, Key Fragility, Process Fatigue, Transaction Error, and the more generic User Error. (4/8)
Fri Jul 03 21:29:07 +0000 2020
That’s why one of the core precepts of #SmartCustody is simply to have a safe, redundant copy of your private keys that you keep somewhere remote. #SmartCustody is that simple. (3/8)
Fri Jul 03 21:29:07 +0000 2020
Any thoughts on the category of “Loss by Mistakes”? Any specific adversaries that I missed? Let us know! And please consider supporting the book this is drawn from, #SmartCustody. We’re working on V2, with multi-sigs and other expansions: https://smartcustody.btcpay.blockchaincommons.com/ (8/8)
Fri Jul 03 21:29:08 +0000 2020
Our next category of #SmartCustody adversaries is “Loss by Mistakes”: https://twitter.com/christophera/status/1279165294095695872?s=21 https://twitter.com/ChristopherA/status/1279165294095695872
Fri Jul 03 21:30:04 +0000 2020
Replying to @NachoAlamillo, @heathervescent, @manusporny, @csuwildcat, @kylekemper, @kimdhamilton and @JoeAndrieu
Sure, with attribution to Joe & I. As an independents we don’t have access to ISO documents, so a copy someday would be appreciated. We both had hoped we’d be able to take it to a next generation first though. Better names, more nodes, name all the arrows, fill in missing parts.
Fri Jul 03 21:54:26 +0000 2020
An article about @BlockchainComns and our new “virtual” intern program this summer. I’ve had interns in past such as @kiarabickers but in these days of social distancing we need to find new ways to nurture talent. I’ve been enjoying collaborating with them these last few weeks! https://twitter.com/decryptmedia/status/1279160034136592385
Fri Jul 03 23:03:34 +0000 2020
Replying to @synxiecbeta
My GateWatch gmless cooperative uses the back side of the deck for story prompts. The front side is used for three formats, 6 for rules, 6 for act framing & plot prompts, and 6 for resolution. Digital P&P for Avery sized cards at https://dyvershands.itch.io/gate-watch or cards @ DriveThruRPG.
Sun Jul 05 01:06:50 +0000 2020
We are due to retire DSA. https://twitter.com/FiloSottile/status/1279513567235096578
Sun Jul 05 01:27:42 +0000 2020
RT @lukOlejnik: Flaws found in Estonian electronic identity cards. Sometimes allowed to impersonate people. Sometimes - break the secret ke…
Sun Jul 05 18:52:16 +0000 2020
CONVENIENCE is an error that arises from your decision to ignore your normal security procedures. Yet that decision might be for entirely good and pragmatic reasons. (2/8)
Mon Jul 06 20:03:15 +0000 2020
#SmartCustody Adversary — Convenience
Our first adversay in category “Loss by Mistakes” is CONVENIENCE. It sounds, well, convenient, doesn’t it? But it is a real adversary because focusing on it instead of safety or security can cause you to lose your digital assets. (1/8)
Mon Jul 06 20:03:15 +0000 2020
Have your own stories of CONVENIENCE impacting digital assets? Your own solutions? Let us know! And please consider supporting #SmartCustody. We’re working on V2, with multi-sigs and other expansions: https://smartcustody.btcpay.blockchaincommons.com/ (8/8)
Mon Jul 06 20:03:16 +0000 2020
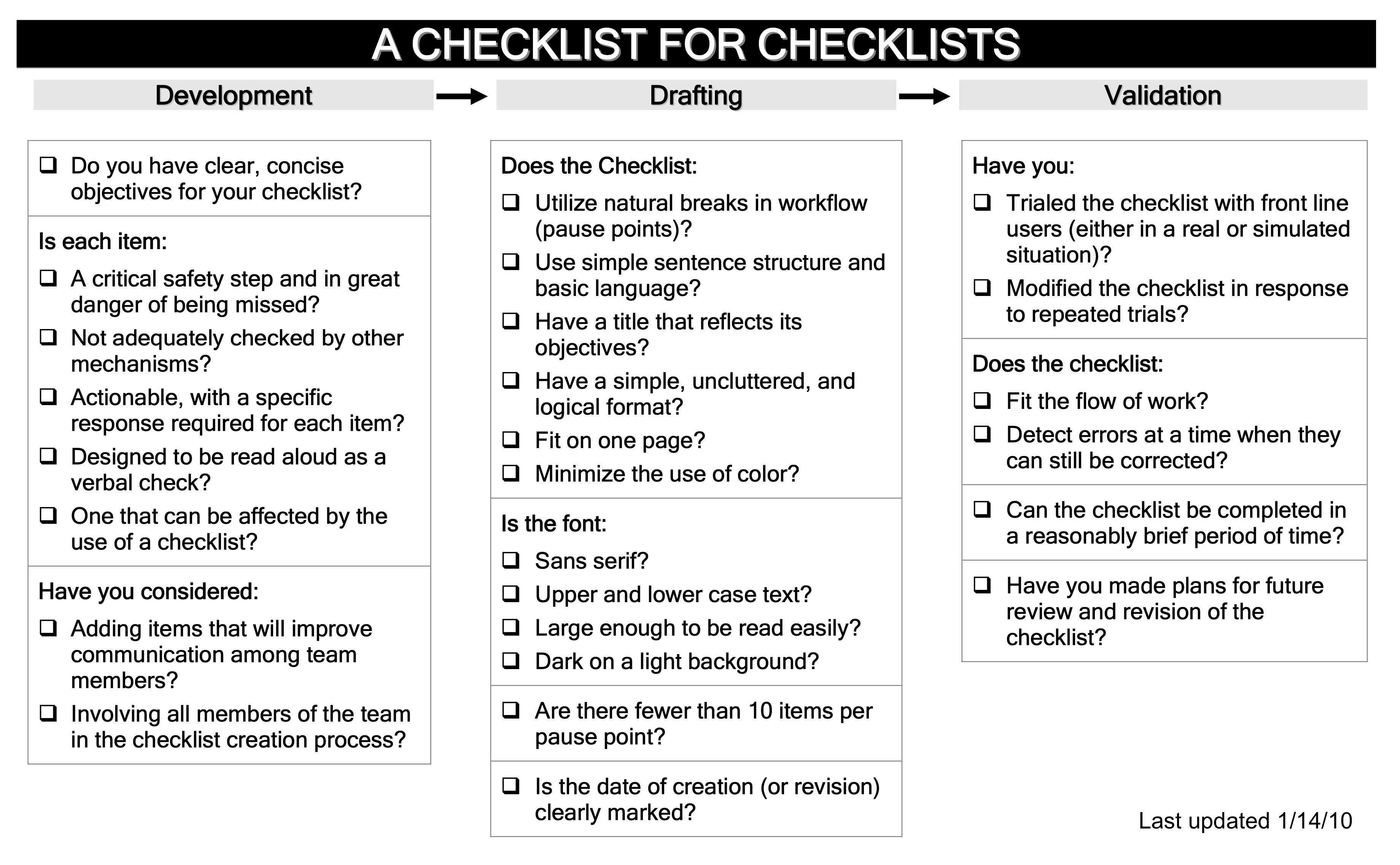
A key to mitigating the threat of CONVENIENCE is to create checklists for your process. This is what airline pilots do. If you skip or change a step, force yourself to sign-off on it. Then at least you KNOW what risks you are taking isn’t about laziness, but is important. (7/8)
Mon Jul 06 20:03:16 +0000 2020
One of the challenges of CONVENIENCE is that, like many the other adversaries in this category, what is convenient to mitigate a threat for a different adversary may increase the threat of this adversary. You want to be just convenient enough but no more! (6/8)
Mon Jul 06 20:03:16 +0000 2020
The solution is obvious: don’t do it. But more thoughtfully: carefully consider any time that you prioritize CONVENIENCE over security and safety, be aware of the new threats you’re creating, and make sure they’re worth it. (5/8)
Mon Jul 06 20:03:16 +0000 2020
Here’s how I imagine the motivation: “I know that you want things to be simple. … if you’re going on a trip, definitely ease up on the security of your bitcoins, so that you can access them from the road. I’m sure nothing bad can happen from all of this ease of use!” (4/8)
Mon Jul 06 20:03:16 +0000 2020
If you’re on the road, cold storage might not be accessible, or it might be vulnerable to theft. If you’re frequently trading, you might need access to your cryptocurrency in a easy and quick manner. CONVENIENCE is important, but can be also dangerous. (3/8)
Mon Jul 06 20:03:16 +0000 2020
Our first #SmartCustody adversary in the category of “Loss by Mistakes” is CONVENIENCE: https://twitter.com/christophera/status/1280230853117804545?s=21 https://twitter.com/ChristopherA/status/1280230853117804545
Mon Jul 06 20:04:11 +0000 2020
RT @signalapp: We’d announce that we’re stopping too, but we never started turning over user data to HK police. Also, we don’t have user da…
Mon Jul 06 20:04:43 +0000 2020
In other words, KEY FRAGILITY is the problem of not just losing your key, but copying it wrong or having it corrupted in storage or even losing it due to the difficulty of a scheme for splitting it up. A private key is complex and that makes it a point of failure. (4/13)
Tue Jul 07 22:04:00 +0000 2020
But it’s an adversary that you can actively help: “Perhaps you could make my job easier by encoding or obscuring your key or by maintaining just a single copy; complexity and singularity both beget fragility in different ways..” (3/13)
Tue Jul 07 22:04:00 +0000 2020
To offer the motivation: “I am entropy writ small. All I need to do is mislay a digit or two from a ridiculously large number, and my job is done.” (2/13)
Tue Jul 07 22:04:00 +0000 2020
#SmartCustody Adversary - Key Fragility
KEY FRAGILITY. For many, this is the big adversary in digital-asset management: the one most likely to cost you your assets. That makes it a big concern in #SmartCustody too. (1/13)
Tue Jul 07 22:04:00 +0000 2020
This adversary also suggests that you don’t want to out-clever yourself. Every single thing you do to make a key harder to access, from hiding it to encrypting it makes it that much more likely that you’ll lose it. (9/13)
Tue Jul 07 22:04:01 +0000 2020
Instead, have faith in manufactured titanium. You can etch your key into it, and as long as you make sure it’s clear and precise, and that it’s stored safely, it’ll be there, forever (or close enough for your purposes). (8/13)
Tue Jul 07 22:04:01 +0000 2020
So don’t place trust in mnemonics. Don’t assume that you can remember that extra BIP38 secret word. Definitely don’t assume you can put your key in a memorized brainwallet! (7/13)
Tue Jul 07 22:04:01 +0000 2020
You can even lose a key by losing the PIN to your hardware wallet, a number that you probably thought was very simple to recall. (6/12) https://www.wired.com/story/i-forgot-my-pin-an-epic-tale-of-losing-dollar30000-in-bitcoin/
Tue Jul 07 22:04:01 +0000 2020
The tales of losing keys to cryptocurrency are legion. A bug in the code wrote the the wrong key to disk. Keys on a hard drive accidentally erased, a hard drive sent to the dump by a maid. Paper keys lost in a fire, others turned to mush by a fire fighter’s hose. (5/13)
Tue Jul 07 22:04:01 +0000 2020
Have your own stories of Key Fragility impacting digital assets? Your own solutions? Let us know! And please consider supporting #SmartCustody. We’re working on V2, with multi-sigs and other expansions: https://smartcustody.btcpay.blockchaincommons.com/ (13/13)
Tue Jul 07 22:04:02 +0000 2020
Remember that #SmartCustody is ultimately about considering risks and unemotionally assessing them. So consider: is your offline cold-storage seed more likely to be stolen by a thief or more likely to be lost or forgotten by you? (12/13)
Tue Jul 07 22:04:02 +0000 2020
We focus on single key cold storage scenarios in v1 of #SmartCustody, future multisig scenarios can address some risks, multisig also means that more information needs to be backed up, and successfully restored. So KEY FRAGILITY will continue to need to be addressed. (11/13)
Tue Jul 07 22:04:02 +0000 2020
Among my colleagues that contributed to bitcoin-core, an informal survey showed the greatest losses were due to KEY FRAGILITY, in particular loss or misuse of an added BIP38 secret word. (10/13)
Tue Jul 07 22:04:02 +0000 2020
Our next #SmartCustody adversary in the category of “Loss by Mistakes” is KEY FRAGILITY: https://twitter.com/christophera/status/1280623626287341568?s=21 https://twitter.com/ChristopherA/status/1280623626287341568
Tue Jul 07 22:05:30 +0000 2020
RT @dstadulis: “We kill based on metadata”
>he narrowly escaped being killed on 5 separate occasions: 2 strikes on cars he was travelling…
Tue Jul 07 22:40:07 +0000 2020
👏👍“Google announced SkyWater PDK, the first manufacturable, open source process design kit. What differentiates this PDK…is the fact that it is manufacturable: with this PDK, you can actually produce chips with the SkyWater foundry in the 130nm node.” https://fossi-foundation.org/2020/06/30/skywater-pdk
Tue Jul 07 22:42:56 +0000 2020
A few things intrigue me about this proposal. First, SkyWater’s silicon fab appears to be in MN. Next the 130nm process may be legacy but is small enough for some good simple secure chip designs, but also large enough to be auditable by many parties including universities. …
Tue Jul 07 22:48:29 +0000 2020
I’d love to se a good TRNG, ability to securely store 8 private master keys, ability to pass in derivative paths, and sign using the resulting keys securely with secp256k1 in both ECDSA & Schnorr, able to accept provable nonce mix, and 8 monotonic counters. All auditable.
Tue Jul 07 22:53:46 +0000 2020
RT @ChristopherA: A few things intrigue me about this proposal. First, SkyWater’s silicon fab appears to be in MN. Next the 130nm process m…
Tue Jul 07 22:54:14 +0000 2020
RT @ChristopherA: I’d love to se a good TRNG, ability to securely store 8 private master keys, ability to pass in derivative paths, and sig…
Tue Jul 07 22:54:16 +0000 2020
Replying to @taoeffect, @aitherick, @zacharylarson and @manusporny
I’m not sure how up to date ERC 725 & 735 are today but that was being used a while ago: https://hackernoon.com/first-impressions-with-erc-725-and-erc-735-identity-and-claims-4a87ff2509c9
Wed Jul 08 01:57:06 +0000 2020
I am pleased to be asked to be an advisor to @AvantiBT led by @CaitlinLong_. I am careful who I accept to have an advisor role with — I helped support Caitlin in Wyoming for the last few years to establish their leadership in law and regulation for digital assets. Great work! https://twitter.com/custodiabank/status/1280891850102956032
Wed Jul 08 19:12:48 +0000 2020
Replying to @kanzure
I’ve been asking around — nothing so far.
Wed Jul 08 19:13:22 +0000 2020
RT @CaitlinLong_: CHECK OUT who’s helping @AvantiBT build a new breed of bank that bridges the US dollar payments system with #Bitcoin & #d…
Wed Jul 08 19:13:53 +0000 2020
So how do you solve it? The answer is in the name, PROCESS FATIGUE. It’s not pure laziness; it’s when you have a process for securing your digital assets that overwhelms you. It’s too much. (4/12)
Wed Jul 08 19:56:21 +0000 2020
We all do this. This isn’t meant as a perjorative. It’s just a question of solving the problem, not ignoring it. (3/12)
Wed Jul 08 19:56:21 +0000 2020
PROCESS FATIGUE is a close cousin: this is another adversary that encourages you to ignore your security procedures, but here it’s just because you are overwhelmed, or have become overly familiar or lazy with your procedures over time. (2/12)
Wed Jul 08 19:56:21 +0000 2020
#SmartCustody Adversary — Process Fatigue
A few days ago I wrote about Convenience, which was a #SmartCustody adversary that could cause loss of your digital assets because you ignored your security procedures. But, it was for theoretically good reasons. (1/12)
Wed Jul 08 19:56:21 +0000 2020
That’s the heart of our risk-modeling: looking at the various problems that you face and deciding which are the most crucial to solve. In this case, you have to determine is if something is MORE dangerous than the PROCESS FATIGUE it might create or less. (9/12)
Wed Jul 08 19:56:22 +0000 2020
The solution goes back to the core idea that #SmartCustody is all about making choices, about figuring out which adversaries are the most dangerous and which aren’t, and focus on the most dangerous first. PROCESS FATIGUE is likely one of them. (8/12)
Wed Jul 08 19:56:22 +0000 2020
Another risk with PROCESS FATIGUE is becoming so overwhelmed that you skip the process entirely. For instance, the Glacier Protocol https://glacierprotocol.org process is quite strong, but I know even some of the contributors to it keep saying “I plan on implementing it soon”. (7/12)
Wed Jul 08 19:56:22 +0000 2020
PROCESS FATIGUE is a pretty dangerous adversary because it can make you randomly and thoughtlessly ignore parts of your procedure. You instead want to do so specifically and thoughtfully. (6/12)
Wed Jul 08 19:56:22 +0000 2020
One particular source of PROCESS FATIGUE is that every new procedure, new device, skill required or new tech you add to your processes to mitigate the risk of a different adversary makes PROCESS FATIGUE become more risky. (5/12)
Wed Jul 08 19:56:22 +0000 2020
Have your own stories of Process Fatigue impacting digital assets? Your own solutions? Let us know! And please consider supporting #SmartCustody. We’re working on V2, with multi-sigs and other expansions: https://smartcustody.btcpay.blockchaincommons.com/ (12/12)
Wed Jul 08 19:56:23 +0000 2020
#SmartCustody is ultimately an iterative process: something that you might return to over time, to reassess and retrofit your storage procedures. Part of that should be determining if any elements are creating PROCESS FATIGUE, and if they can be removed (or not). (11/12)
Wed Jul 08 19:56:23 +0000 2020
In particular PROCESS FATIGUE is a personal adversary. What is overwhelming to you might not be for me. This is why the #SmartCustody book works hard to offer a baseline of checklists & processes, which you can add to optionally for your needs. But not too many! (10/12)
Wed Jul 08 19:56:23 +0000 2020
Our next #SmartCustody adversary in the category of “Loss by Mistakes” is PROCESS FATIGUE: https://twitter.com/christophera/status/1280953891006197760?s=21 https://twitter.com/ChristopherA/status/1280953891006197760
Wed Jul 08 19:57:32 +0000 2020
I’m looking for help to prototype this basic secure chip at two different levels — one is what an API to such a hardware chip might look like, and if it is sufficient or if one or two other functions would make a big difference. The other requires a dive into the SkyWater PDK. https://twitter.com/ChristopherA/status/1280636153859723265
Wed Jul 08 20:03:46 +0000 2020
Replying to @pa_btc
It isn’t clear to me that importing a private key is core requirement. It would be nice, but ultimately it has its own risks which I’m not as confident cheap silicon can address. Instead, maybe that private key can be passed to and decrypted by the silicon. Not sure architecture.
Wed Jul 08 20:07:00 +0000 2020
New #Decentralized #DigitalIdentity #SSI paper released today from last year’s #RWOT8 design workshop “Driving Adoption with Focus on Basic Human Needs: Safety and Security” led by Sam Chase @CircleWorkTV with @mckervey @CarstenStoecker & Dan Burnett: https://github.com/WebOfTrustInfo/rwot8-barcelona/blob/master/final-documents/driving-adoption-needs.md
Wed Jul 08 21:23:53 +0000 2020
“Each of these use cases will track a user’s journey and highlight the implementation of verifiable credentials as a means to increase trust and efficiency while also protecting personally identifying information (PII).”
Wed Jul 08 21:23:54 +0000 2020
“4 use cases: updating fire safety training with spatial computing; reducing fatigue-related workplace accidents with sleep data; issuing security clearances for journalists through background checks & managing trust in accident-prevention systems for autonomous driving programs”
Wed Jul 08 21:23:54 +0000 2020
“This paper investigates two primary forces that have the potential to drive adoption of decentralised technology by both individuals and enterprises: safety and security.”
Wed Jul 08 21:23:54 +0000 2020
“(We) outline systems using self-sovereign principles that provide mutual benefit to system administrators and users and that have a net positive impact on process efficiencies. Each use case describes a decentralised-credential system model that can be further adopted at scale.”
Wed Jul 08 21:23:55 +0000 2020
Replying to @kanzure
I don’t know. Since Open Titan is intended for mobile it seems to me that it might be on a bit tight for a low power 130nm chip for use with #RISCV. But I’m a real amateur in regards to modern hardware architecture — last one that I can say I half-way understood was the 6502.
Wed Jul 08 23:34:50 +0000 2020
But you’d be very wrong to think that TRANSACTION ERRORS are gone entirely. It’s still easy to copy the wrong address from a list. And when you do things repetively it is easy to make mistakes. Just last week I sent one contractor my other contractor’s regular payment. (5/10)
Thu Jul 09 18:17:05 +0000 2020
In the several years we’ve been writing about issues with digital assets, the likelihood of TRANSACTION ERROR has been dropping. QR Codes make addresses easier to use, wallets and servers are increasingly keeping you from making the most obvious errors. (4/10)
Thu Jul 09 18:17:05 +0000 2020
Spending cryptocurrency isn’t as simple as handing over cash (or a credit card). There are a lot of things you have to get right, and with it all cloaked in pseudonymity, it’s harder than ever to be certain you’re sending the right amount to the right person. (3/10)
Thu Jul 09 18:17:05 +0000 2020
As always in #SmartCustody, we express adversaries as motivations: “I am the slightest error in a transaction. I want your transaction to do something that you don’t expect. I am the startling results that are ultimately detrimental to you.” (2/10)
Thu Jul 09 18:17:05 +0000 2020
Wrong address? Wrong amount? Wrong change address? Wrong change amount? Wrong fee? Wrong script? Wrong timelock date? These are all potential TRANSACTION ERRORS, an adversary to the #SmartCustody of your digital assets. (1/10)
Thu Jul 09 18:17:05 +0000 2020
The best solution for a TRANSACTION ERROR is care. Verify each number and address twice. Check and double-check. Never transact in a hurry: take the time! (7/10)
Thu Jul 09 18:17:06 +0000 2020
And if you do more complex things like write scripts, it’s quite possible to design something that never completes. Attackers can even force errors, like when hackers replaced a funding address for a CoinDash ICO and stole the money. (6/10) https://www.coindesk.com/7-million-ico-hack-results-coindash-refund-offer
Thu Jul 09 18:17:06 +0000 2020
I also believe in the power of checklists — even experts like doctors and pilots use them in their professions, you can too! On this topic I particularly like the book “Checklist Manifesto” by @Atul_Gawande and this summary of it as a video https://www.youtube.com/watch?v=bCDmDzIOZ-g (8/10)
Thu Jul 09 18:17:07 +0000 2020
Have your own stories of TRANSACTION ERROR impacting digital assets? Will you share some of your own checklists? And please consider supporting #SmartCustody. We’re working on V2, with multi-sigs, more checklists, and other expansions: https://smartcustody.btcpay.blockchaincommons.com/ (10/10)
Thu Jul 09 18:17:08 +0000 2020
The cold-storage scenario we offer in the #SmartCustody book is a big checklist, reviewed by many experts and tested in the real world. Copy it and make similar lists for your own procedures. (9/10) https://github.com/BlockchainCommons/SmartCustodyBook/blob/master/manuscript/03-adversaries.md
Thu Jul 09 18:17:08 +0000 2020
Another #SmartCustody adversary in the category of “Loss by Mistakes” is TRANSACTION ERROR: https://twitter.com/christophera/status/1281291296645058560?s=21 https://twitter.com/ChristopherA/status/1281291296645058560
Thu Jul 09 18:17:57 +0000 2020
RT @ChristopherA: I also believe in the power of checklists — even experts like doctors and pilots use them in their professions, you can t…
Thu Jul 09 18:18:22 +0000 2020
RT @ChristopherA: The cold-storage scenario we offer in the #SmartCustody book is a big checklist, reviewed by many experts and tested in t…
Thu Jul 09 18:18:37 +0000 2020
RT @bavarianledger: Finally finished building the amazing #Lethekit.
Thanks to @ksedgwic and @ChristopherA.
Doesn’t it look adorable?
More…
Thu Jul 09 21:16:10 +0000 2020
Replying to @francispouliot_
Yes—almost impossible to have a typo in modern addresses, EXCEPT for another valid address. To users they all look alike. So the one on your clipboard or QR may be the wrong one, for instance the previous one. This just happened to me last week. Thinking about adding warning.
Thu Jul 09 21:20:25 +0000 2020
RT @ChristopherA: @francispouliot_ Yes—almost impossible to have a typo in modern addresses, EXCEPT for another valid address. To users the…
Thu Jul 09 21:20:37 +0000 2020
Replying to @hodlwave, @michaelfolkson and @francispouliot_
Both are possible, but the malware is a different adversary. I consider the clipboard substitution most likely is a SYSTEMIC NETWORK ATTACK as they are rarely specifically target you but all apps of a specific type. https://twitter.com/christophera/status/1272955265730490368?s=21 https://twitter.com/ChristopherA/status/1272955265730490368
Fri Jul 10 00:33:15 +0000 2020
#SmartCustody Adversary — User Error
I’ve spent the last week sharing about the various sorts of “Loss by Mistakes” that can cause you to lose digital assets. #SmartCustody helps you mitigate these risks. Now I want to discuss a final, more general mistake: USER ERROR. (1/11)
Fri Jul 10 19:15:00 +0000 2020
Leaving your infant to play with your Ledger and finding your keys erased? That’s USER ERROR combined with Key Fragility. Drunkenly bragging about your Bitcoin holdings and then getting hacked? That’s USER ERROR combined with Correlation & Network Attack, Personal (6/11)
Fri Jul 10 19:15:01 +0000 2020
Often, USER ERROR is tied in to other adversaries, to make them even more risky. (5/10)
Fri Jul 10 19:15:01 +0000 2020
Forgetting to pay for your safety deposity box and having the bank throw out your backup keys? That’s USER ERROR. (4/11) https://www.uppo.org/blogpost/925381/281568/Unclaimed-Safe-Deposit-Box-Basics
Fri Jul 10 19:15:01 +0000 2020
USER ERROR is every other mistake that you could make that in some way could cost you your digital assets. (3/11)
Fri Jul 10 19:15:01 +0000 2020
These are mistakes that aren’t covered by other adversaries in this category. It’s not Convenience or Process Fatigue (where you ignore your security procedure), it’s not Key Fragility (where you lose a seed) and it’s not Transaction Error (where you mess up a transfer). (2/11)
Fri Jul 10 19:15:01 +0000 2020
Do you have your own stories of USER ERROR impacting digital assets to share? Your own solutions or checklists? Let us know! And please consider supporting #SmartCustody. We’re working on V2, with multi-sigs and other expansions: https://smartcustody.btcpay.blockchaincommons.com/ (11/11)
Fri Jul 10 19:15:02 +0000 2020
This is the last #SmartCustody “Loss by Mistakes” adversary. Next week we’ll conclude this series with our last category “Privacy-Related Problems”. Let us know if you have found this series useful! (10/11)
Fri Jul 10 19:15:02 +0000 2020
Like with other adversaries in this category, you need to be constantly thoughtful and responsible. With decentralization and self-sovereignty, we take over responsibilities from centralized authorities, and we need to prove ourselves worthy of them. (9/11)
Fri Jul 10 19:15:02 +0000 2020
For insance, I lost a Ledger once as I forgot to label it and entered the PIN for a different Ledger too many times and thus erased it. A friend of mine left his Trezor on his desk and the cat swept it into the trash basket. What other weird USER ERROR stories do you have? (8/11)
Fri Jul 10 19:15:02 +0000 2020
This is another adversary that can be defeated with care, time, double-checking, and of course checklists. But it also requires some out-of-the-box thinking. This is where the community can really help each other by sharing the more odd stories. (7/11)
Fri Jul 10 19:15:02 +0000 2020
Our last #SmartCustody adversary in the category of “Loss by Mistakes” is USER ERROR: https://twitter.com/christophera/status/1281668262502166534?s=21 https://twitter.com/ChristopherA/status/1281668262502166534
Fri Jul 10 19:15:41 +0000 2020
RT @ChristopherA: This is another adversary that can be defeated with care, time, double-checking, and of course checklists. But it also re…
Fri Jul 10 19:16:12 +0000 2020
Replying to @kevinakwok
Happened to me a while back, fortunately had a relatively recent backup. OneTab has serious problems with lots of links. Imported to Better One Tab and it can store more, but clunky in other ways. Best one of these types is a paid app only for Safari.
Sat Jul 11 08:55:54 +0000 2020
As a game designer, this thought is kind of scary. A self-evolving ARG meme game. “Every single QAnon behavior I’ve seen is a 10x+ version of ARG player behavior but uncontrolled, undirected and unconstrained” https://twitter.com/hondanhon/status/1281685535686180864
Sat Jul 11 18:01:27 +0000 2020
RT @JasonReitman: When he was saying “As you wish”, what he meant was, “I love you.”
The great Carl Reiner and Rob Reiner. https://t.co/wf6…
Sun Jul 12 03:53:01 +0000 2020
I’m pleased to hear that ∑-script, which I mentioned in my paper & talks on #SmartSignature script languages for authentication, now has a successor called ErgoTree: https://twitter.com/chepurnoy/status/1282461736214437889
Mon Jul 13 17:18:49 +0000 2020
Simplicity is another #SmartSignature language and I’m proud to have witnessed its birth at @Blockstream. It has been two years since I left Blockstream, but I have been keeping my eye out for this important milestone: Jets, premade compositional code blocks in verifiable C. 👍👍 https://twitter.com/Blockstream/status/1246581437630947330
Mon Jul 13 17:21:47 +0000 2020
#SmartCustody Category — Privacy-Related Problems
Almost all of the adversaries covered in #SmartCustody are about losing your digital assets. But there are other things of value that you could lose, which is why my final Category of adversaries is PRIVACY-RELATED PROBLEMS (1/9)
Mon Jul 13 17:58:12 +0000 2020
Loss of privacy can often become cascade problem as it can make your other adversaries even stronger. If you lose privacy, people might find out more about your digital assets and how you access them, and that might make you vulnerable to other losses. (3/9)
Mon Jul 13 17:58:13 +0000 2020
I envision privacy-related problems as a naked man trying to hide his nudity. It’s embarassing, it vulnerable, but it can be worse than that! (2/9)
Mon Jul 13 17:58:13 +0000 2020
The revelation of certain medicinal purchases? Of campaign contributions? Your support of free speech? You get the idea. (6/9)
Mon Jul 13 17:58:14 +0000 2020
But loss of privacy can be a problem in and of itself: your cryptocurrency holdings, or what you do with them, could endanger you or your reputation in other ways. (5/9)
Mon Jul 13 17:58:14 +0000 2020
So this category of #SmartCustody adversaries includes some of those cascades: the new problems that occur when your privacy is lost. (4/9)
Mon Jul 13 17:58:14 +0000 2020
This category includes three adversaries: Correlation can cost you your privacy; Censorship can be an unfortunate result; and Loss of Fungibility lies in the middle as a Privacy-specific attack. (7/9)
Mon Jul 13 17:58:15 +0000 2020
Loss of privacy can lead to coercion against your right to speak freely, to assemble peacefully, to vote & to earn a living. To me supporting privacy is to support anti-violence, in particular against the corrosive forms of violence that don’t require guns or rubber hoses. (8/9)
Mon Jul 13 17:58:16 +0000 2020
Any thoughts on Privacy-Related Problems? Any specific adversaries that I missed? Let us know! And please consider supporting the book this is drawn from, #SmartCustody. We’re working on V2, with multi-sigs and other expansions: https://smartcustody.btcpay.blockchaincommons.com/ (9/9)
Mon Jul 13 17:58:17 +0000 2020
Our last category of #SmartCustody adversaries (and our last week of this series) is Privacy-Related Problems: https://twitter.com/christophera/status/1282736099983388672?s=21 https://twitter.com/ChristopherA/status/1282736099983388672
Mon Jul 13 17:59:43 +0000 2020
At @BlockchainComns we have been researching interoperable standards for secure airgapped communication between wallets & the network, for use in tools like #LetheKit, @FullyNoded2, @CoboVault, #Spectre @CryptoAdvance. Latest research:
URDemo Animated QRs https://youtu.be/t-GGZ9FyuT8
Mon Jul 13 18:45:19 +0000 2020
There is a lot more research going on. This all is part of a collaboration between multiple cryptocurrency wallet companies. If you are a wallet developer, please contact us to join in the conversation. Please sponsor Blockchain Common on @Github https://github.com/sponsors/BlockchainCommons
Mon Jul 13 18:51:19 +0000 2020
A video so you can test your own Animated UR QR implementations against is at https://youtu.be/YwgSmOa4ltg
Mon Jul 13 18:51:19 +0000 2020
Details on our research for what the requirements are for UR data and how this demo works functions is at: https://github.com/BlockchainCommons/Research/blob/master/papers/bcr-2020-005-ur.md
Mon Jul 13 18:51:19 +0000 2020
The open source for this demo right now is only in an iOS Swift app at https://github.com/BlockchainCommons/URDemo but we are working on a C++ reference as well.
Mon Jul 13 18:51:19 +0000 2020
Thanks to everyone that reviewed or contributed parts of this research (and I am missing a few!): cc/ @WolfMcnally @Fonta1n3 @msgilligan @ksedgwic @MarkFriedenbach @manusporny @StepanSnigirev @BitcoinLixin @gorazdko & financial support from @bitmarkinc @AvantiBT @unchainedcap
Mon Jul 13 19:15:05 +0000 2020
One of our big remaining items in our research is to port animated QRs to #LetheKit, an very constrained open source DIY hardware box for offline cryptographic tools. We’ll report back in the next few weeks how fast it can output UR: https://github.com/BlockchainCommons/bc-lethekit
Mon Jul 13 19:23:57 +0000 2020
Replying to @evanwolf and @github
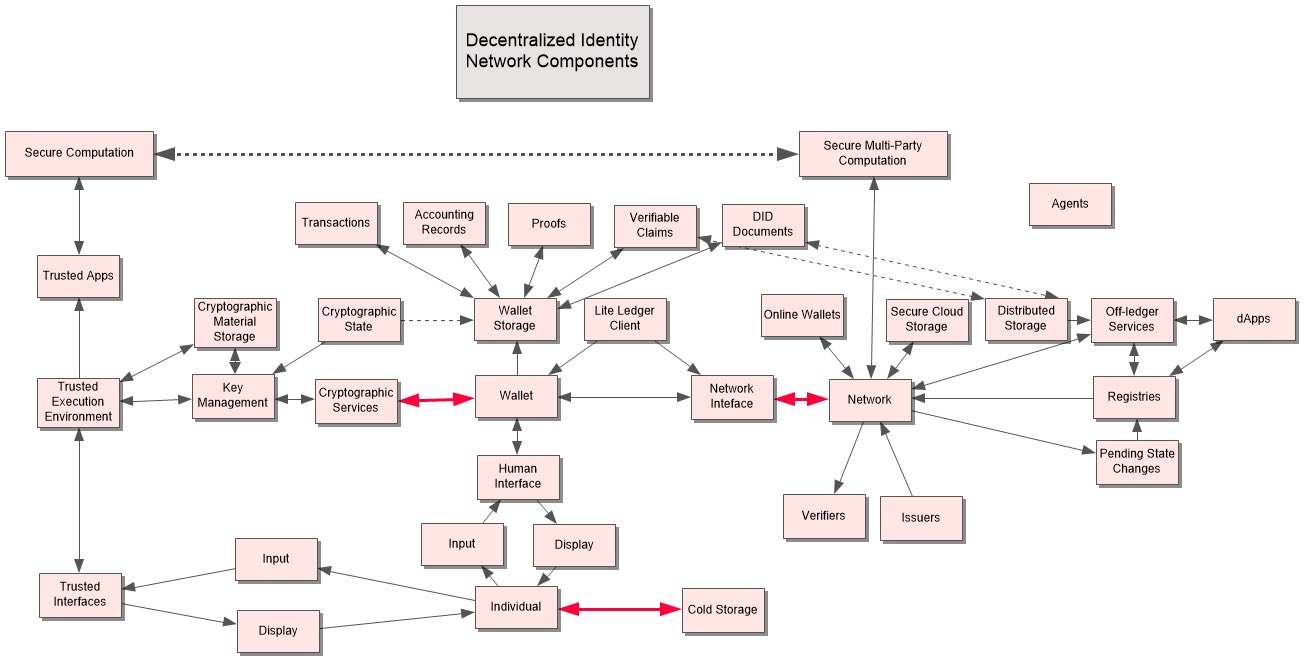
Absolutely. @FullyNoded 2 and #LetheKit both came out of requirements to have a full bitcoin wallet in order to implement the BTCR DID method. You’ll also see hints on the potential airgap requirements in the red lines in this identity wallet architecture: https://github.com/WebOfTrustInfo/rwot9-prague/blob/master/topics-and-advance-readings/whats-wallet.md
Mon Jul 13 19:26:53 +0000 2020
Yes, I agree — desire by some to continue a so-called mandate for cryptoagility is misguided. I was co-author of TLS 1.0 and even ciphersuites ultimately became an insufficient constraint. Still dealing with problems in JOSE architecture due to it. /cc @kennwhite @Dejan_Kosutic https://twitter.com/kennwhite/status/1282786618466799617
Tue Jul 14 01:06:37 +0000 2020
RT @heathervescent: On Tuesday, July 14, the Credentials Community Group at the W3C will have “What’s in a wallet?” part 2 (w/ @IdentityWom…
Tue Jul 14 05:59:19 +0000 2020
A story in a thread… https://twitter.com/TheRealDoctorT/status/1282722029758750720
Tue Jul 14 06:02:48 +0000 2020
It’s important to remember that Bitcoin is pseudonymous, not truly anonymous. You can see where money came from. You can trace it forward and backward. That’s the definition of the blockchain, and is also true for many other blockchains. (2/13)
Tue Jul 14 19:40:04 +0000 2020
Of all of the adversaries found in #SmartCustody, the one most likely to cost you your privacy is CORRELATION. (1/13)
Tue Jul 14 19:40:04 +0000 2020
CORRELATION can also reveal those who you are transacting with are doing business with. You don’t want to be paid for your share of a dinner, only to find that all your funds are not accepted because some of those coins were used in a crime three transactions back. (7/13)
Tue Jul 14 19:40:05 +0000 2020
There’s been some serious forensic analysis of Bitcoin translations when money has gone missing or when people have mysteriously “died”. That could be directed at anyone, including you. (6/13)
Tue Jul 14 19:40:05 +0000 2020
Even just revealing your holdings could be dangerous. Imagine spending from an address with a large balance at a coffee shop. Suddenly, the staff there knows you’re a Bitcoin millionaire, and they physically know who and where you are. That’s not safe! (5/13)
Tue Jul 14 19:40:05 +0000 2020
That’s all pseudonymous too, of course. You interact with Bitcoin addresses that aren’t necessarily tied to specific identities. But they could be. And every one is a transaction that can reduce your own privacy. (4/13)
Tue Jul 14 19:40:05 +0000 2020
It’s also the definition of CORRELATION. If you keep all of your digital assets together, once you make one transaction with someone, they can see all of those funds and all of the others things you did with those funds and all the ways you received them. (3/13)
Tue Jul 14 19:40:05 +0000 2020
And of course, good personal data hygiene helps as well. Don’t offer personal information or KYC/AML proofs to parties that might not serve your interests. (11/13)
Tue Jul 14 19:40:06 +0000 2020
Another anti-CORRELATION tactic is segregation. Keep the funds you use for your different businesses, hobbies, charities, family life and personal life separate. You don’t have to CoinJoin everything, maybe just coins intended for transfers between your own accounts. (10/13)
Tue Jul 14 19:40:06 +0000 2020
So how do you avoid CORRELATION? Key Hygiene. At minimum use a different address for everything. Use wallets that offer coin control. For Bitcoin there are also various trustless coin-mixing methods such as CoinJoin.(9/13) https://en.bitcoin.it/wiki/CoinJoin(7/12)
Tue Jul 14 19:40:06 +0000 2020
Another risk of CORRELATION is that it can increase risk to your colleagues. Your donation to a human rights organization might put your other business partners at risk the next time they enter a country that has human rights problems. (8/13)
Tue Jul 14 19:40:06 +0000 2020
Have your own stories of CORRELATION impacting digital assets? Your own solutions? Let us know! And please consider supporting #SmartCustody. We’re working on V2, with multi-sigs and other expansions: https://smartcustody.btcpay.blockchaincommons.com/ (13/13)
Tue Jul 14 19:40:07 +0000 2020
As with everything in #SmartCustody, assess your danger. Are Privacy-cascade problems such as censorship and physical theft are likely to threaten you? If so, your Privacy is important. If not, you wan to worry more about other adversaries. (12/13)
Tue Jul 14 19:40:07 +0000 2020
Our first #SmartCustody adversary in the category of “Privacy-Related Problems” is CORRELATION: https://twitter.com/christophera/status/1283124120444481537?s=21 https://twitter.com/ChristopherA/status/1283124120444481537
Tue Jul 14 19:41:05 +0000 2020
I wrote this 4 years ago & was an accurate prediction. Even more true for the next decade. Unanticipated consequences of network effects changed the world in just the past four years, and has the potential to change us even more, for either good or bad! Care & attention required. https://twitter.com/ChristopherA/status/810183777494282240
Tue Jul 14 22:26:43 +0000 2020
Replying to @VladZamfir
Four years later re-reading this paragraph I can’t help but wonder if this is in effect what causes a two-party systems in many countries, including such paradoxes as right-to-life partnered with death penalty advocates. That always mystified my EU colleagues.
Tue Jul 14 23:48:05 +0000 2020
I have mixed feeling about this. Academia must evolve and change, but also Google has been offering free “Google Apps for Education” to small collages & schools for over a decade and now is directly competing with them. A conflict of interest. https://twitter.com/CNBC/status/1282839615855104000
Wed Jul 15 00:03:58 +0000 2020
Replying to @camgeer and @kimdhamilton
https://twitter.com/christophera/status/1283190535990079489?s=21 https://twitter.com/ChristopherA/status/1283190535990079489
Wed Jul 15 17:24:52 +0000 2020
The next adversary in the “Privacy-Related Problems” for #SmartCustody is CENSORSHIP. This another example of a adversary that causes a Privacy cascade, where your loss of Privacy causes you other problems. (1/9)
Wed Jul 15 23:10:11 +0000 2020
The motivation is: “I don’t want your money, I just want to make sure you can’t have it. But, I have a deeper motivation than that. Maybe I’m threatening you, maybe I’m blackmailing you, and maybe I’m getting my revenge.” (2/9)
Wed Jul 15 23:10:12 +0000 2020
CENSORSHIP of Bitcoin is only possible if someone knows who you are: “I personally know you, I know you have cryptocurrency, and I’m making sure that you can’t use it.” (3/9)
Wed Jul 15 23:10:13 +0000 2020
Note that you don’t actually lose funds due to CENSORSHIP, you just can’t access them. But if you need to pay for something or to cash in your funds, it amounts to the same thing. At least in the short term. (4/9)
Wed Jul 15 23:10:14 +0000 2020
WikiLeaks received funds through Bitcoins when they were otherwise blockaded. However, even in Bitcoin, theoretically there could be consensus to not mine your transactions. (5/9) https://www.forbes.com/sites/jonmatonis/2012/08/20/wikileaks-bypasses-financial-blockade-with-bitcoin/
Wed Jul 15 23:10:15 +0000 2020
CENSORSHIP in Bitcoin is actually pretty to enforce because censorship-resistence is fundamental to its decentralized design. This may not be as true for smaller cryptocurrencies. (6/9)
Wed Jul 15 23:10:16 +0000 2020
The greatest threat of censorship is your transactions not being mined. You can avoid it entirely if you mine your own blocks, even if you only do so once in a long while. This is why @Blockstream started mining — so that #Liquid would be guarenteed at least one tx a day. (7/9)
Wed Jul 15 23:10:17 +0000 2020
As CENSORSHIP is part of a privacy cascade, the obvious solution is to not lose your privacy. Practice good key hygeine, asset segregation, practice anonymity to avoid correlation. (8/9) https://twitter.com/ChristopherA/status/1283124120444481537
Wed Jul 15 23:10:18 +0000 2020
Have your own stories of CENSORSHIP impacting digital assets? Your own solutions? Let us know! And please consider supporting #SmartCustody. We’re working on V2, with multi-sigs and other expansions: https://smartcustody.btcpay.blockchaincommons.com/ (9/9)
Wed Jul 15 23:10:19 +0000 2020
Our next #SmartCustody adversary in the category of “Privacy-Related Problems” is CENSORSHIP: https://twitter.com/christophera/status/1283539387016519681?s=21 https://twitter.com/ChristopherA/status/1283539387016519681
Wed Jul 15 23:11:22 +0000 2020
“The point…is not just censorship, but its inverse: propaganda. TikTok’s algorithm, unmoored from the constraints of your social network or professional content creators, is free to promote whatever videos it likes, without anyone knowing the difference.“ https://stratechery.com/2020/the-tiktok-war/
Wed Jul 15 23:38:14 +0000 2020
“To that end it has been taking action for over 20 years to control information within its borders and, over the last several years, to control information outside of its borders.”
Wed Jul 15 23:39:37 +0000 2020
“If China is on the offensive against liberalism not only within its borders but within ours, it is in liberalism’s interest to cut off a vector that has taken root precisely because it is so brilliantly engineered to give humans exactly what they want.”
Wed Jul 15 23:40:40 +0000 2020
👍 “Centralization, the ultimate vulnerability.” — @SarahJamieLewis https://twitter.com/SarahJamieLewis/status/1283522973010235392
Thu Jul 16 04:46:33 +0000 2020
I believe that designing #TTRPG’s specifically for use on virtual chat & video platforms will become a major new trend. I’ve been puzzling though how to adapt my gmless collaborative storygame Twilight Road (sequel to last year’s kickstarter Gate Watch) specifically for Zoom. https://twitter.com/JamesIntrocaso/status/1280550852256829441
Thu Jul 16 05:34:29 +0000 2020
#SmartCustody Adversary — LOSS OF FUNGIBILITY
Yesterday we discussed the perils of the Censorship adversary’s desire to “make sure you can’t use” Bitcoin by threatening your ability to transact on-chain. The motive of LOSS OF FUNGIBILITY is “I want to punish other people” (1/15)
Thu Jul 16 18:54:39 +0000 2020
In fact, cryptocurrency like Bitcoin should be even more fungible than most paper currency. That’s because it’s constantly being pooled. There’s no such thing as a discrete coin in Bitcoin — instead all Bitcoin is only a balances on an accounts in a ledger. (3/15)
Thu Jul 16 18:54:40 +0000 2020
Fungibility means that any one unit of a currency is indistinguishable from any other unit. All dollar bills are mostly fungible: until someone writes down a serial number and then monitors its use. The same is true with digital assets. (2/15)
Thu Jul 16 18:54:40 +0000 2020
The problem arises if a Bitcoin was used for something that’s considered antisocial by some community, which could taint the money. And it’s become a real problem in the blockchain world because some exchanges now trace the origins of cryptocurrency. (5/15)
Thu Jul 16 18:54:41 +0000 2020
If Censorship threaten’s your ability to transact on-chain, the LOSS OF FUNGIBILITY adversary threatens your ability to use cryptocurrency elsewhere. This is a serious problem, and in fact it’s the final adversary in my #SmartCustody book. (4/15)
Thu Jul 16 18:54:41 +0000 2020
Yesterday’s #TwitterHack netted over $110K of Bitcoin but already those coins are being blacklisted. Seems like a paltry amount given the sophistication of the attack—but what if the attacker gave those coins to thousands of innocent people? All funds could be blacklisted. (7/15)
Thu Jul 16 18:54:42 +0000 2020
Someone paid you with funds where somewhere in the past it was used by someone as drug money? You’re an American citizen who used your Bitcoins for gambling? In either case, you might suddenly find your funds locked by an exchange. (6/15)
Thu Jul 16 18:54:42 +0000 2020
Mitigating the risks of the LOSS OF FUNGIBILITY adversary are difficult. First step is to make sure that exchanges don’t have exclusive control of your private keys. As I wrote a few days ago, true Censorship is hard because when we are using a decentralized system. (9/15)
Thu Jul 16 18:54:43 +0000 2020
But it isn’t all about illegal source of funds. In the US cryptocurrencies are not legally a “currency” but instead are an “intangible property”. This means that a bankruptcy court could legally say “that payment to you was pledged to someone else, give it back”. (8/15)
Thu Jul 16 18:54:43 +0000 2020
But you can also approach this as a Correlation problem, which I talked about yesterday. LOSS OF FUNGIBILITY only occurs if someone can correlate where your coins came from. (10/15)
Thu Jul 16 18:54:44 +0000 2020
So, scramble them. Use CoinJoin, SendShared, or Zerocoin. Use Confidential Transactions on @Blockstream’s Liquid. We have ways to break the links in the blockchain. (11/15)
Thu Jul 16 18:54:45 +0000 2020
But, as always only concern yourself with this adversary if it truly seems to be a concern. If you genuinely think your funds are likely to be clean, there’s almost no danger here. Or at least prioritize against other adversaries first! (13/15)
Thu Jul 16 18:54:46 +0000 2020
If you in the US are planning to pledge your cryptocurrency against a loan, consider holding your cryptocurrency in Wyoming. Under their laws, after two years all of those funds are consider “perfected” and can’t be clawed back by a bankruptcy judge. (12/15) https://twitter.com/CaitlinLong_/status/1086371268461359105
Thu Jul 16 18:54:46 +0000 2020
Have your own stories of LOSS OF FUNGIBILITY impacting digital assets? Your own solutions? Let us know! And please consider supporting #SmartCustody. We’re working on V2, with multi-sigs and other expansions: https://smartcustody.btcpay.blockchaincommons.com/ (15/15)
Thu Jul 16 18:54:47 +0000 2020
And that closes out my look at Privacy-Related Problems, which included everything I talked about here: Censorship, Correlation, and Loss of Fungibilty. And it’s also the end of my look at 27 different adversaries that can impact your digital assets. (14/15)
Thu Jul 16 18:54:47 +0000 2020
Our last #SmartCustody adversary in the cateogy for “Privacy-Related Problems” is LOSS OF FUNGIBILITY: https://twitter.com/christophera/status/1283837467552972801?s=21 https://twitter.com/ChristopherA/status/1283837467552972801
Thu Jul 16 18:56:40 +0000 2020
Replying to @lackingceremony, @jaceaddax and @jdragsky
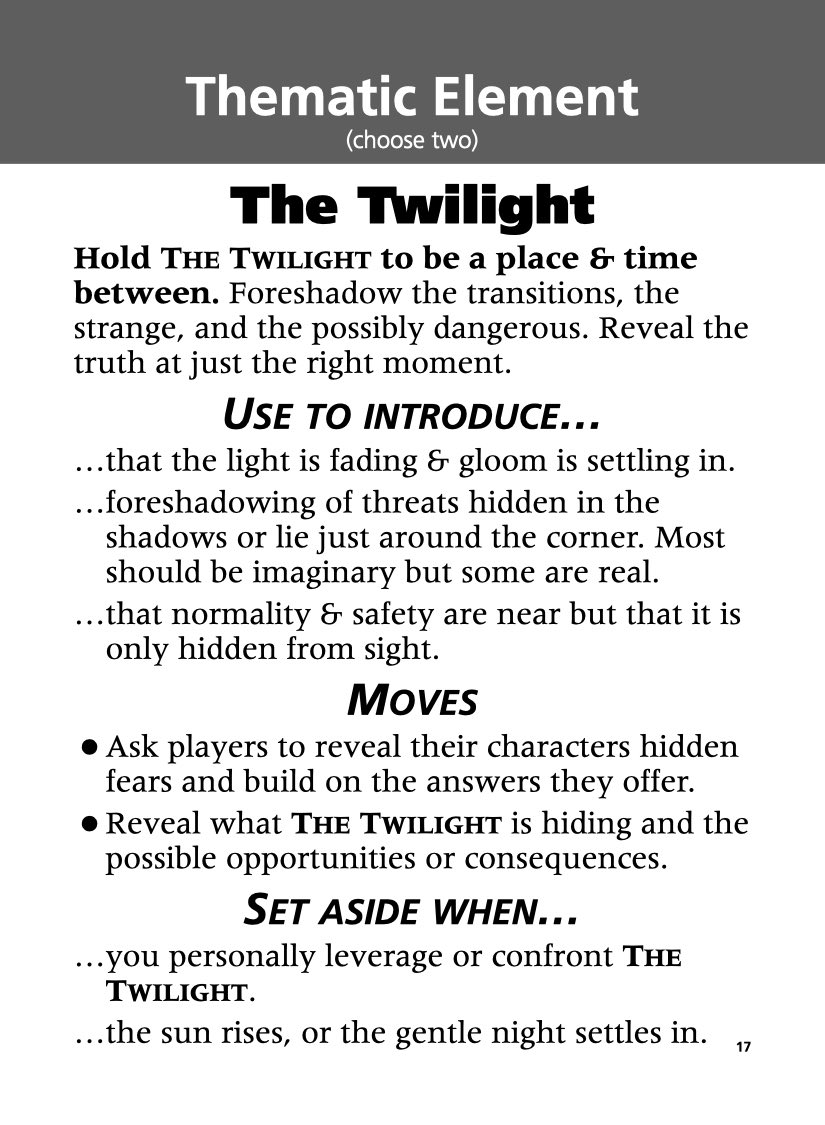
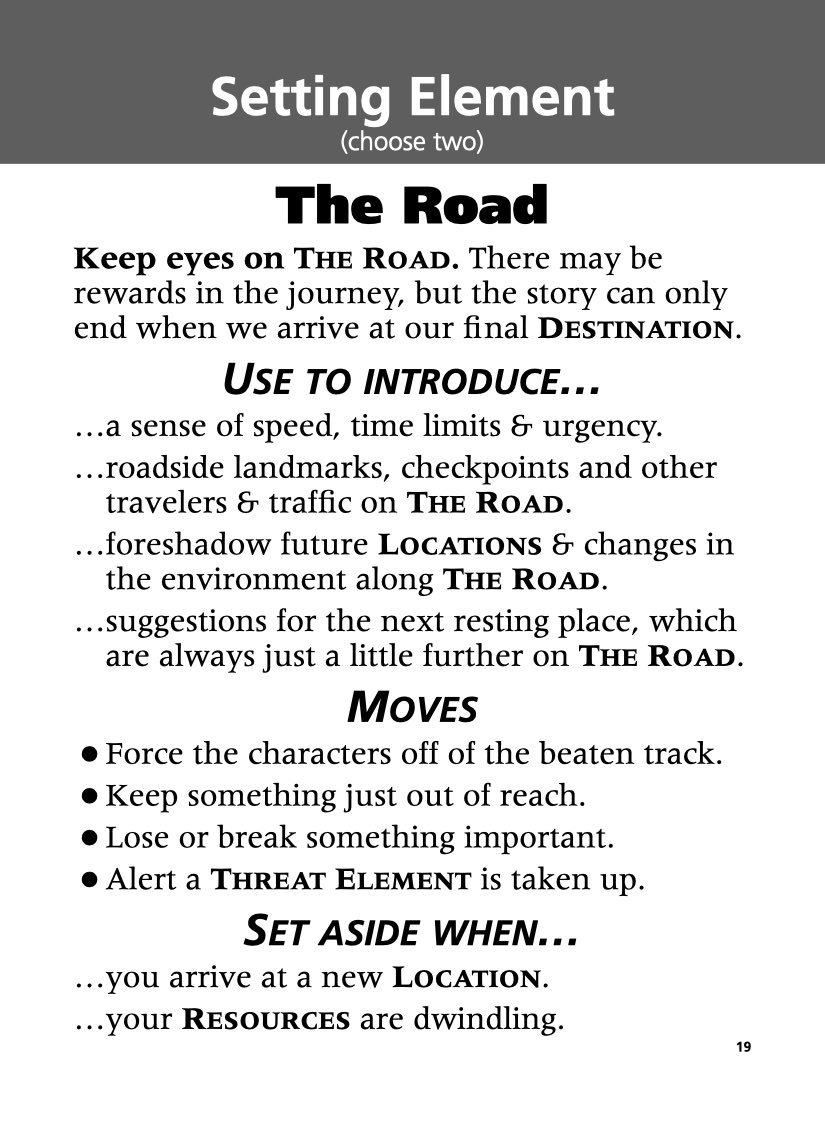
A followup question — any advice for BoB environment moves vs characters moves? I feel like there is a lot of good lessons from PbtA character moves, but what appeals to me most is gmless cooperative opportunties. Here are the two key cards for my “Twilight Road” playtest:
Fri Jul 17 07:09:41 +0000 2020
Replying to @lackingceremony, @jaceaddax and @jdragsky
@lackingceremony, I definitely started there, and greatly appreciate your lead! I do find inspiration at other BoB examples since your publication, and am puzzling how to evolve setting elements. For instance, I’m finding that these elements can lead to one another…
Fri Jul 17 07:37:50 +0000 2020
Replying to @lackingceremony, @jaceaddax and @jdragsky
For instance, in my game you start with Twilight & Road in play, but choosing Road can open up Locals, and then Locals can leads to Authorities.
Fri Jul 17 07:40:06 +0000 2020
Replying to @lackingceremony, @jaceaddax and @jdragsky
On another axis, I’m also finding some of these are clearly more setting elements, but other are more “thematic” elements (like Kith & Kin here) and yet others are more explicitly focused on being threats (in this case The Beyond) which has to be returned when a move is used.
Fri Jul 17 07:44:38 +0000 2020
Replying to @lackingceremony, @jaceaddax and @jdragsky
Avery, in some BoB games since Dream Askew I’m seeing that some are moving toward strong and weak moves for more than characters and also using them plot elements. But also I’m seeing emerging ”permissions” which are neither strong or weak, that you get just by holding the role.
Fri Jul 17 07:48:15 +0000 2020
Replying to @lackingceremony, @jaceaddax and @jdragsky
Unfortunately in times of COVID-19, my irregular roleplaying playtesters has fallen even more apart, and of course other playtest opportunities at conventions are now complete cancelled. So I’m seeking thoughts from other BoB designers on what is emerging since Dream Askew.
Fri Jul 17 07:50:57 +0000 2020
Replying to @chepurnoy
Any advantages of using secp256k1 with ErgoScript? We’ve been paper-napkin possibilities of also leveraging bulletproofs for curve operations using the secq “mirror” curve: https://github.com/BlockchainCommons/secp256k1-schnorrsig/issues/1#issuecomment-410482607
Fri Jul 17 08:37:34 +0000 2020
Since the beginning of June I have shared about the 27 digital asset adversaries from my #SmartCustody book. I was able to produce this content thanks to the sponsors and supporters for the project to date. (1/12) https://www.smartcustody.com/sponsors/
Fri Jul 17 19:50:13 +0000 2020
And, that’s only Chapter 3 of #SmartCustody, pages 93-155. You can read the whole book for free thanks to these generous patrons! (2/12) https://bit.ly/SmartCustodyBookV101
Fri Jul 17 19:50:15 +0000 2020
The rest of the book covers randomness, basic personal risk-modeling, our full cold-storage self-custody scenario & checklists, discusses fiduciary duties, and offers a more advance risk-model example for a family fund. (3/12) https://bit.ly/SmartCustodyBookV101
Fri Jul 17 19:50:17 +0000 2020
But I’d like to do more. My co-author, @Appelcline and I have outlined a second edition of the book that would make room for discussing other hardware wallets, introduce multisignatures, and include personal and fidicuiary multi-sig scenarios. (4/12)
Fri Jul 17 19:50:18 +0000 2020
You can support producing #SmartCustody 2.0 by helping us to meet our goal of 5 BTC dedicated to the Second Edition through crowdfunding via our BTCPay server. (5/12) https://smartcustody.btcpay.blockchaincommons.com/
Fri Jul 17 19:50:19 +0000 2020
Or you can become a Patron of Blockchain Commons and support not only #SmartCustody but also our other open projects intended to improve blockchain and cryptocurrency infrastructure through monthly patronage as a GitHub Sponsor. https://github.com/sponsors/BlockchainCommons (6/12)
Fri Jul 17 19:50:21 +0000 2020
We also invite hardware wallet companies, full-node vendors, custodians, advisors, and legal experts to sponsor us. We can include your services or hardware in lists in the book, and we can also give you ad space. Ask me for more information. (7/12)
Fri Jul 17 19:50:22 +0000 2020
If you’re interested in advice via Zoom about your own personal #SmartCustody scenario or checklists, please also contact me directly. I can offer a personal consultation for just $500 for 50 minutes of my time. (8/12)
Fri Jul 17 19:50:24 +0000 2020
#SmartCustody is a project of Blockchain Commons, a “not-for profit” benefit corporation that’s creating blockchain infrastructure that can help everyone who cares about decentralization, blockchains, Bitcoin, digital civil rights, and more. (9/12)
Fri Jul 17 19:50:25 +0000 2020
Our projects include the Bitcoin StandUp full-node installer, the @FullyNoded 2 Bitcoin multisig wallet, this #SmartCustody book, the “Learning Bitcoin from the Command Line” developer course, our LetheKit DIY platform, and many more! (10/12) https://github.com/blockchaincommons
Fri Jul 17 19:50:27 +0000 2020
This is the last of this extended series of tweet storms on #SmartCustody. Let me know if it was useful, if there are ways we can spread the word about #SmartCustody, and if there are other topics that you’d like to see me share more about. (11/12)
Fri Jul 17 19:50:28 +0000 2020
You can also help the digital commons yourself by actively contributing to make an open web, digital civil liberties, and human rights possible. Let me know what you are doing, and let’s collaborate! (12/12) ៚
Fri Jul 17 19:50:29 +0000 2020
We conclude this series of tweet storms to ask for your help in making V2 of #SmartCustody possible, and to help in our broader mission to support open blockchain infrastructure, internet security, the open web, digital civil liberties, and more. https://twitter.com/christophera/status/1284213839337189377?s=21 https://twitter.com/ChristopherA/status/1284213839337189377
Fri Jul 17 19:53:36 +0000 2020
👍 Very nice overview of the different kinds of Bitcoin nodes and the different ways they connect on the network together. The only things I might add for next version are: the role of Tor, about FIBRE connections (mostly between miners), and value of sattelite/mesh connections. https://twitter.com/glozow/status/1282808196055224320
Sat Jul 18 02:02:41 +0000 2020
Replying to @bitcoin_ch, @pamelawjd and @TheBitStory
I had a good experience speaking at @bitcoin_ch last time. The next time I’m in Europe I’ll offer another talk. Currently hoping that things improve enough by summer 2021 to spend a few months in Switzerland & the EU. Virtual probably until then.
Sat Jul 18 02:10:17 +0000 2020
Replying to @tarah and @astepanovich
I keep reading great work by @TeenVogue (4+ years now). I’d love to know how this is happening and how we can incentive other media to offer the same integrity for at least some content of them all.
Sat Jul 18 02:20:37 +0000 2020
Replying to @intjr
I keep putting them out there. Some stick, some do not. I learn something from everything I put out there from both those ideas that get great engagement and even those that do not (of course Twitter algorithms make it harder). Memetic engineering is definitely not a science yet.
Sat Jul 18 07:40:05 +0000 2020
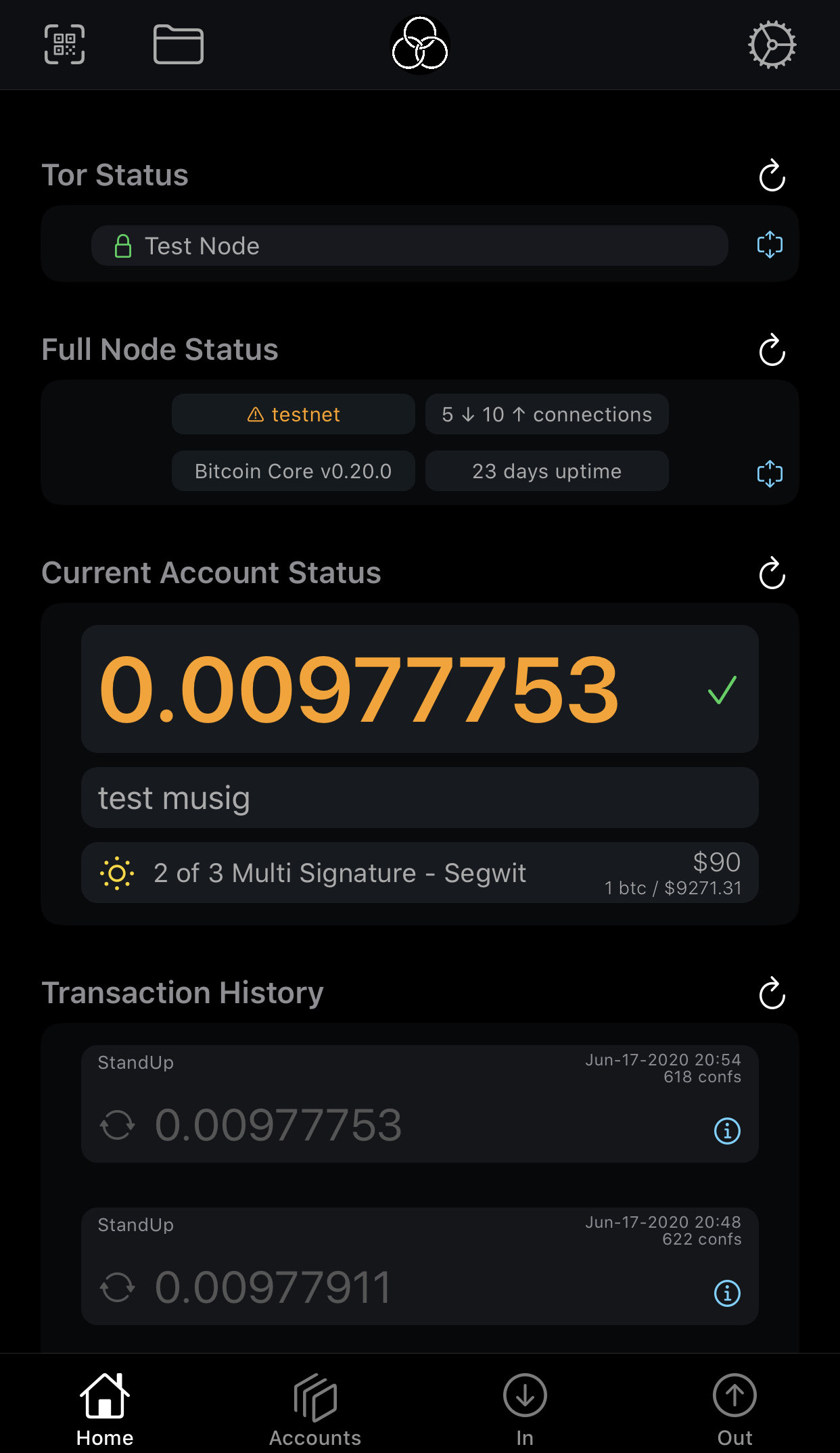
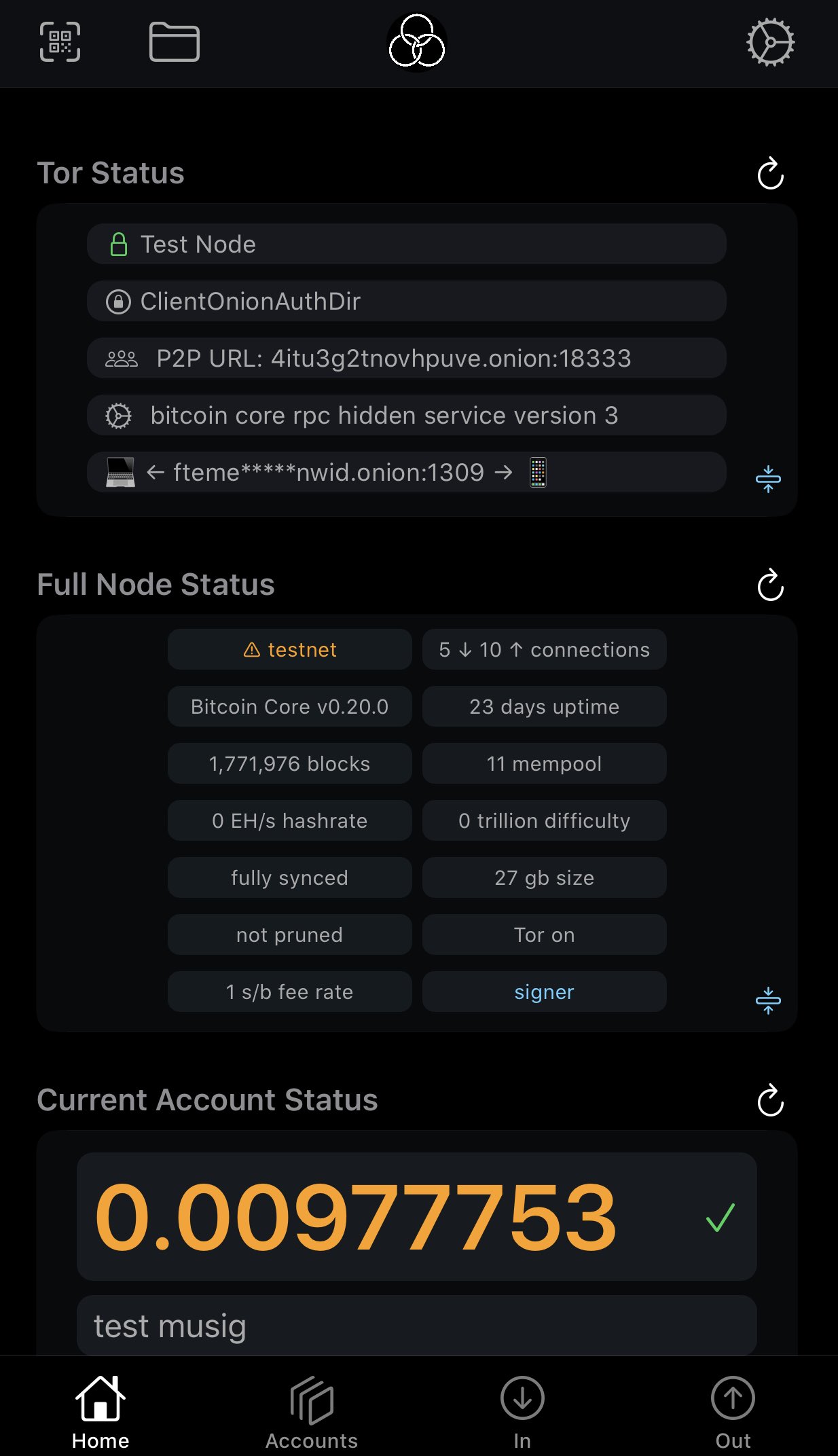
Replying to @nopara73
FullyNoded & FullyNoded2 — both are mobile apps to your personal full node(s) via Tor. Your full node can also be configured to only use Tor. We are releasing spotbit so so that it can retrieve pice info and make only available via Tor. We also support UTXO coin & change control.
Sun Jul 19 09:35:49 +0000 2020
Replying to @nopara73
We are not supporting any mixing right now, but hope to do payjoin and some other simple things soon. We also support now a number of multisig scenarios, and can sign one of the sigs in anything that can be described by a descriptor.
Sun Jul 19 09:38:42 +0000 2020
Replying to @nopara73
One idea we have is cooperative mixing. We use higher numbered change address derivations (maybe 2) to pass change to a mixer, and when done it returns it to change 0. Wallet carefully segregates.
Sun Jul 19 09:42:21 +0000 2020
Replying to @nopara73
FullyNoded2 is actually Blockchain Commons second bitcoin wallet, but we threw the 1st away as lessons learned. We tried to do Neutrino but required us to either have dependencies on libraries we didn’t have confidence in, or build from scratch. Both were too risky.
Sun Jul 19 18:31:44 +0000 2020
Replying to @balajis and @prestonjbyrne
I nurtured and an architecture for Decentralized Identifiers starting about 5 years ago, which is now emerging as an international standard in W3C. BUT, despite A Bitcoin method being the first proposed it still isn’t fully implemented as there is no business model there…
Sun Jul 19 21:54:22 +0000 2020
Replying to @balajis and @prestonjbyrne
…thus the three big LESS (legally enabled self-sovereign identity) DID platforms (IBM-backed HyperLedger Indy/Sovrin, Microsoft/Consensys DIF, and http://Veres.One/Digital Bazaar) are all making great progress, while we who helped created the trustless BTCR are toiling without…
Sun Jul 19 21:58:30 +0000 2020
Replying to @balajis and @prestonjbyrne
We need support from the larger Bitcoin community, but anything that smells of identity at all largely turns them off. I want to implement BIP322 to sign BTCR messages with Bitcoin transactions, but @kallewoof reports little backing. We need people like you to help. …
Sun Jul 19 22:01:58 +0000 2020
Replying to @balajis, @prestonjbyrne and @kallewoof
All this energy you’ve been putting in this week in talking about disintermediating Twitter is possible and there are experts like myself & others working toward. But the problem is not technical but financial. No VC wants to invest in anything truly decentralized as…
Sun Jul 19 22:04:49 +0000 2020
Replying to @balajis, @prestonjbyrne and @kallewoof
The business models are difficult. Blockchain Commons is in no way recouping our expenses for things like our FullyNoded2 wallet or efforts toward decentralized identity on a trustless platform like BTCR as no one knows how to monetize it sufficiently. We are trying patronage…
Sun Jul 19 22:08:11 +0000 2020
Replying to @balajis, @prestonjbyrne and @kallewoof
…but so far no proof that patronage is a viable model. VCs want an exit, not a fundamental bootstrap that could grow the whole pie. …
Sun Jul 19 22:12:35 +0000 2020
Replying to @balajis, @prestonjbyrne and @kallewoof
There are higher layers that might be possible to be profitable for VCs but so far require the bottom layer to lock the user. Casa is an example, but as once you are using them you are locked into their solution, and they have no desire to in interoperate with other wallets.
Sun Jul 19 22:13:37 +0000 2020
Replying to @balajis, @prestonjbyrne and @kallewoof
Which makes sense for them but not for the industry. Right now Blockchain Commons has been working with multiple wallet vendors for interoperability and no vendor lock-in, but it is hard. And it will likely be even harder as we start to create DIDs that will address your problems
Sun Jul 19 22:16:22 +0000 2020
Replying to @balajis, @prestonjbyrne and @kallewoof
So I urge you to help us solve this underlying problem — there are some essential tools that can’t be safely monetized. The browser is an example: it needs to be free, and the biz model somewhere else, but we have fighting for 30 years to keep it from being abused and failing. …
Sun Jul 19 22:19:24 +0000 2020
Replying to @balajis, @prestonjbyrne and @kallewoof
Same is true for wallets — both for cryptocurrency and for decentralized identity. We must keep them independent with no vendor lock-in as ultimately they needs to under the control of the individual or it isn’t safe.
Sun Jul 19 22:22:18 +0000 2020
Replying to @balajis, @prestonjbyrne and @kallewoof
Bottom line, the problem here is not tech, but the intersection of a viable business model and what is safe for the larger community.
Sun Jul 19 22:32:52 +0000 2020
Replying to @JasonCoombsCEO, @balajis, @prestonjbyrne and @kallewoof
The problem is that Bitcoin holders are not incentivized to invest in the larger ecosystem. Right now they’d rather HODL every bitcoin rather than invest a percentage to make all bitcoin more valuable, including their own. …
Sun Jul 19 22:36:29 +0000 2020
Replying to @JasonCoombsCEO, @balajis, @prestonjbyrne and @kallewoof
Reid Hoffman got a great return on his investment on Blockstream as Bitcoin increased more than 100x because Blockstream offered resources to make it better. Blockstream shouldn’t need an exit, but due to VC model it must, making it less useful to whole community now than it was.
Sun Jul 19 22:40:24 +0000 2020
Replying to @EMostaque, @balajis, @prestonjbyrne and @kallewoof
There are great engineers that don’t need options and a big exit to join us, but they do need to be paid at least somewhat competitively. So biggest expense is people. But these projects need long term support, or Heartbleed-like incidents happen.
Sun Jul 19 22:44:05 +0000 2020
Replying to @EMostaque, @balajis, @prestonjbyrne and @kallewoof
We have reached out to foundations (both civic society and cryptocurrency) but the first only make short-term project based commitments. The second are also short-term but largely want the project to be tight with their cryptocurrency, not general purpose like a wallet.
Sun Jul 19 22:46:37 +0000 2020
Replying to @EMostaque, @balajis, @prestonjbyrne and @kallewoof
The http://Charter.Network is an attempt to reach out to parties like Knight Foundation to become involved. https://www.prnewswire.com/news-releases/blockchain-commons-and-bitmark-introduce-charter-a-new-social-media-architecture-301078535.html
Sun Jul 19 22:48:17 +0000 2020
Replying to @JasonCoombsCEO, @balajis, @prestonjbyrne and @kallewoof
I’m certainly not forking Bitcoin to fund wallet development and support. We don’t know how to do so safely, as we’ve seen what happens both in the recent past with Bitcoin as well as in other cryptocurrency communities. Incentive design is very hard.
Sun Jul 19 22:52:29 +0000 2020
Replying to @EMostaque, @balajis, @prestonjbyrne, @kallewoof and @cuysheffield
Here is a high-level architecture of what a combined cryptocurrency & decentralized identity wallet needs, but still a lot to define. From my paper: https://github.com/WebOfTrustInfo/rwot9-prague/blob/master/topics-and-advance-readings/whats-wallet.md
Sun Jul 19 23:22:56 +0000 2020
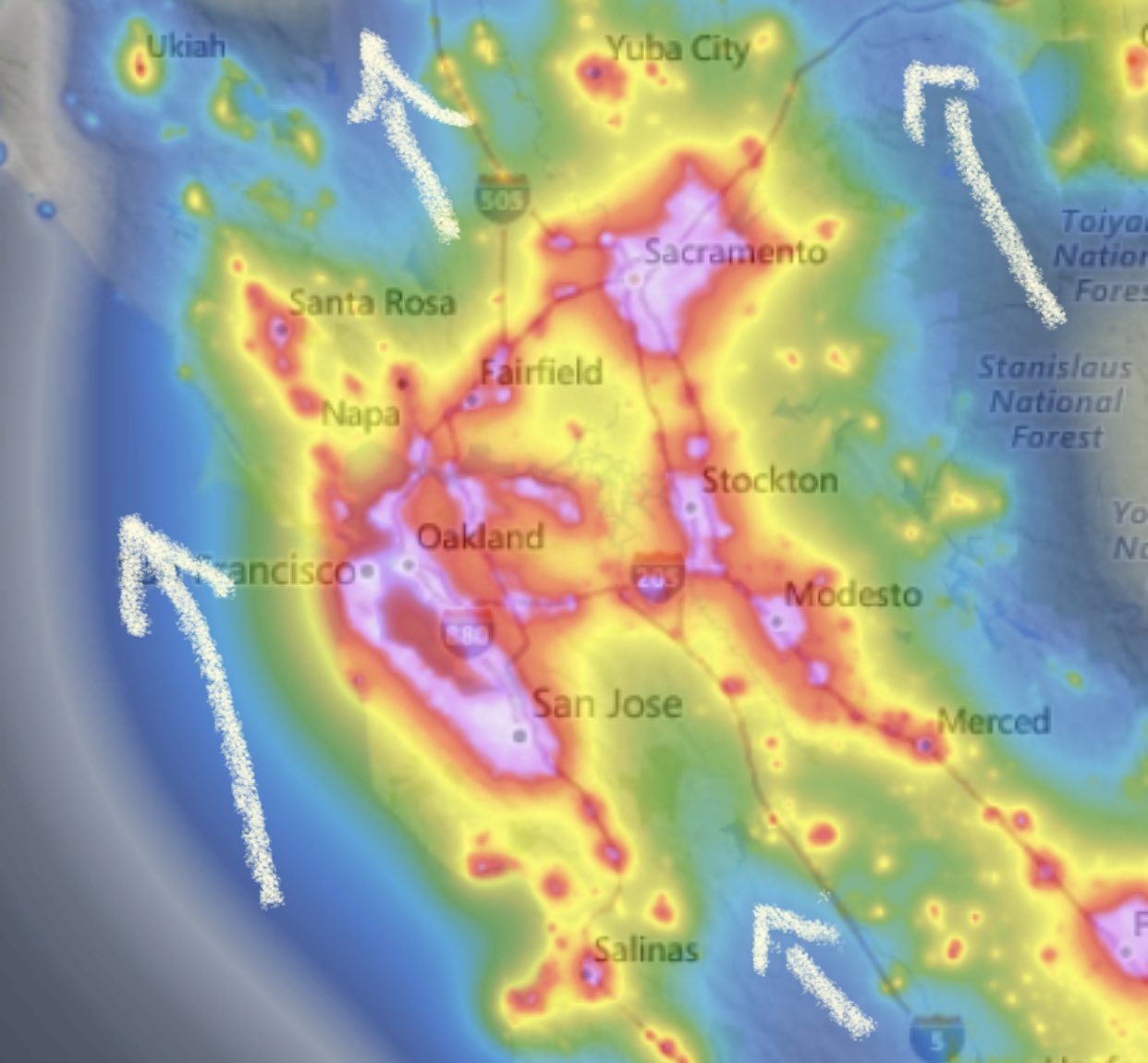
For those of seeking a good place to see the Neowise comet, a good source is this Light Pollution Map for where a NW view is unobstructed. I’m thinking a road trip to Wilbur Springs, CA is warranted: https://www.lightpollutionmap.info/#zoom=6.19&lat=4638087&lon=-13548529&layers=B0FFFFFTFFFFFFFFF /ht @bradtem
Mon Jul 20 00:51:53 +0000 2020
The Capay Valley (great organic farming valley) is rather nice, but not sure if farm stands are still open. Cache Creek Casino in the valley might have camping or RV spots, or visit newly reopened/restored rustic Wilbur Hot Springs resort. About 1-1/2 to 2 hour drive, so not bad.
Mon Jul 20 01:06:27 +0000 2020
I’ve shared before about the Cantillon Effect that causes the rich to get richer. Due to the delay in the market response to information about inflation, it gives banks & others closer to the sources of creation of currency an advantage. By @MattStoller https://mattstoller.substack.com/p/the-cantillon-effect-why-wall-street
Mon Jul 20 16:43:24 +0000 2020
We need a new name for the Fully Noded 2 wallet, as it has been causing some confusion. FN1 is a power-user tool to control your full node, whereas FN2 is focused on being best multisig user wallet UX leveraging your full node over Tor.
Mon Jul 20 18:26:13 +0000 2020
RT @evanwolf: @ChristopherA Name it after a classic pen to help with all those signatures.
Wax (like seals on an envelope) Then prepend…
Mon Jul 20 23:31:42 +0000 2020
I’m watching last year’s #Apollo11 documentary & just finished binge-watching @forallmankind_ last weekend. I only hazily remember the landing as I was only 8, but it felt nearby as I lived in Florida. That summer I recall more that I was PO’d that Star Trek wasn’t coming back.
Mon Jul 20 23:47:51 +0000 2020
I really enjoyed Apple+’s For All Mankind — led by Ronald D. Moore a former show runner of future Star Trek series. It shows how clearly how close he believes we came to doing more. Missed opportunity.
Mon Jul 20 23:54:54 +0000 2020
So far is seeking a new name for the Fully Noded 2 bitcoin multisig mobile wallet the winners is “Keep on looking for a name” at 64%. Next best is “Autonomy Wallet” at only 18%. Seeking more suggestions! https://twitter.com/ChristopherA/status/1285279863155224576
Tue Jul 21 19:36:52 +0000 2020
The “ergodicity” problem in economics is also a design problem of blockchains, collaborations, sustainability, incentives, risk management, etc. Fundamentally it is about how to optimize results over time rather than for an instant “now”. @TaylorPearsonMe has a good thread on it. https://twitter.com/TaylorPearsonMe/status/1282815076316188676
Tue Jul 21 22:06:16 +0000 2020
I’ve also shared before another good article on the ergodicity problem: “How ergodicity reimagines economics for the benefit of us all” by @mark__buchanan : https://twitter.com/ChristopherA/status/1167768865201430528?s=20
Tue Jul 21 22:09:28 +0000 2020
RT @ChristopherA: I’ve also shared before another good article on the ergodicity problem: “How ergodicity reimagines economics for the bene…
Tue Jul 21 22:09:38 +0000 2020
Replying to @kylekemper and @La__Cuen
There is a public beta on testflight for iOS at https://github.com/blockchainCommons/fullynoded-2#installing-fullynoded-2-from-testflight
Tue Jul 21 22:30:52 +0000 2020
Replying to @VinayTaylor and @Li7ardKing
http://www.lifewithalacrity.com/2004/08/intimacy_gradie.html
Wed Jul 22 06:29:50 +0000 2020
Replying to @VinayTaylor and @Li7ardKing
Lots of great patterns applicable to online here as well. There has been even discussions about applications of this one online, but I’ve see online tea parties “breaking bread together” https://groupworksdeck.org/patterns/Breaking_Bread_Together
Wed Jul 22 06:35:47 +0000 2020
Replying to @kylekemper and @La__Cuen
Right now only Bitcoin, and on the roadmap L2 Bitcoin like Lightning. We might support other UTXO blockchains like Litecoin if they ship Schnorr & Taproot significantly before others. Public beta right now is testnet, but private beta includes mainnet. …
Wed Jul 22 21:17:50 +0000 2020
Replying to @kylekemper and @La__Cuen
We might support or offer a fork for a very limited number of other UTXO coins like @ZcashFoundation @monero if there is substantial uniqueness to the coin and solid financial backing for us. We’ll likely never do Ethereum-like coins in this wallet but maybe support atomic swaps.
Wed Jul 22 21:21:31 +0000 2020
Replying to @kylekemper, @La__Cuen, @ZcashFoundation and @monero
All that being said, our security tools & code are all open source & designed to be useful not only for other blockchains, but other security tools like Tor, Signal, etc. In particular #LetheKit offline seed management & airgap QR features are agnostic to chain, token or usage.
Wed Jul 22 21:27:25 +0000 2020
We are currently working on updates to the next edition of our #SmartCustody book that will add to best practices for multisig, threat & risk modeling, adversarial analysis, and mitigation strategies. We also offer security & operational architecture reviews for custodians.
Wed Jul 22 21:54:43 +0000 2020
I hope that #OCC & @BrianBrooksOCC will set the bar for digital asset custody regulations at least as high as the ones defined under #Wyoming regulations where I am an advisor. Unfortunately, there is too much “security by obscurity” & “security theatre” in the custody space. https://twitter.com/CoinDeskMarkets/status/1285983044265017344
Wed Jul 22 21:54:43 +0000 2020
For a peek at our process for creating threat & risk models for digital asset #SmartCustody, this series of twitter threads shares how we think about adversaries: https://twitter.com/ChristopherA/status/1267560491657728000
Wed Jul 22 21:54:46 +0000 2020
Free #SmartCustody PDF v1.01 2019-09-16: http://bit.ly/SmartCustodyBookV101
At-cost POD (print-on-demand) $13.50 from Lulu #SmartCustody by Christopher Allen (Paperback) - Lulu: http://bit.ly/SmartCustodyBookViaLulu
Financially support updates to the next edition: #SmartCustody! https://smartcustody.btcpay.blockchaincommons.com
Wed Jul 22 21:54:48 +0000 2020
Replying to @tdryja
What might be a good scenario for supporting it in our iOS wallet?
Wed Jul 22 22:16:36 +0000 2020
Replying to @djkinkle and @CaitlinLong_
Personally (not speaking for anyone else) if the #OCC @BrianBrooksOCC get involved in custody regulatory requirements it might throw into the light to fix some poor digital custody practices. But if every state has to create their own regs could get worse. https://twitter.com/christophera/status/1286057109906264064?s=21 https://twitter.com/ChristopherA/status/1286057109906264064
Wed Jul 22 23:50:36 +0000 2020
Replying to @djkinkle, @CaitlinLong_ and @BrianBrooksOCC
I believe that #Wyoming regs do best at defining good custody practices (great work by Task Force & Chris Land!) but no one has actually fully implemented their regs yet so it may require some further tweaking. I’m seeking funding to publish a tech requirements document for it.
Wed Jul 22 23:57:02 +0000 2020
RT @ChristopherA: @djkinkle @CaitlinLong_ Personally (not speaking for anyone else) if the #OCC @BrianBrooksOCC get involved in custody reg…
Wed Jul 22 23:57:27 +0000 2020
For me, the key point in today’s #OCC’s regulatory interpretative letter on digital assets: “Specifically, the OCC has concluded that a national bank may escrow encryption keys“ https://www.occ.gov/topics/charters-and-licensing/interpretations-and-actions/2020/int1170.pdf
Thu Jul 23 00:07:20 +0000 2020
The second is “National banks may also provide non-fiduciary custody services to their customers…pursuant to the business of banking and their incidental powers.”
Thu Jul 23 00:12:26 +0000 2020
And finally “Such controls may need to be tailored in the context of digital custody…For example, procedures for verifying that a bank maintains access controls for a cryptographic key will differ from the procedures used for physical assets.”
Thu Jul 23 00:14:23 +0000 2020
RT @ChristopherA: The second is “National banks may also provide non-fiduciary custody services to their customers…pursuant to the business…
Thu Jul 23 00:14:28 +0000 2020
RT @ChristopherA: And finally “Such controls may need to be tailored in the context of digital custody…For example, procedures for verifyin…
Thu Jul 23 00:14:31 +0000 2020
Replying to @tdryja
Our wallet is cooperative. V3 Tor to connect to your own private pruned node, an archive node, at home or on a VPS. You can standup a SpotBit price server via Tor or other microservices. Eventually you can also WoT to friends & colleagues. So wondering if there is a sweet spot.
Thu Jul 23 03:15:33 +0000 2020
Scary thought but maybe? 🤔 “I’m not sure what a fire drill for global madness looks like, but an alarm alone — just the knowledge we may be in the middle of a mass hysteria — is something Google could build in a week, and it would have tremendous benefit” https://solana.substack.com/p/jump-23d06adb4cb7
Thu Jul 23 04:46:19 +0000 2020
Not only is it an ouroboros (snake eating it’s own tail) of a GPT-3 AI writing a post in the style of the author, the topic of identity reset in modern society is one that I have thinking of for a while but had not seen others write about & it is one I can imagine by @nayafia. https://twitter.com/nayafia/status/1286142500453801984
Thu Jul 23 05:15:46 +0000 2020
The other side is from SF. I once read a not-so-great fiction but great futurist book that talked that with immortality we have to learn forgiveness, or at least allow for redemption, or else we will tear each other apart. I’ve incorporated these ideas into my own fiction.
Thu Jul 23 06:10:40 +0000 2020
My own interest in identity reset come from two related areas: the American myths of the west, of cowboys, and even more recently noir are full of stories of escape from identity, some successful, some with identity coming back from the past to haunt you. …
Thu Jul 23 06:10:40 +0000 2020
So @nayafia, have you ever written about identity reset? Did the AI come up with topic based on some deeper memetic understanding, or was imitating something you’d done before?
Thu Jul 23 06:10:40 +0000 2020
Replying to @WillManidis and @GritGrowthCap
I’m also curious how large the input source material was, how long prompt was for this post vs what it wrote.
Thu Jul 23 08:03:03 +0000 2020
Replying to @mattysino, @sinoglobalcap, @dermotmcg and @Ian_88899
Re: this being done a city, @mattysino, I’ve been seeing that in in Self-Sovereign Identity, some of the best work is not being done at the national level, but at the regional or city level. Zug, The Hague, Wyoming, Scotland, Vienna, Catalan, Taipei.
Thu Jul 23 18:13:29 +0000 2020
RT @negrunch: “Learning Bitcoin (and Lightning) from the Command Line” is one of the most tasteful #Bitcoin resource, the excitement I got…
Thu Jul 23 22:01:40 +0000 2020
Replying to @oscpacey and @tdryja
Still in early stages, but here is the repo https://github.com/BlockchainCommons/spotbit Initially it is a self-hosted Tor Onion services that can do various price related functions on your behalf. Longer term goal is P2P WoT cooperative to share price discovery in information. Led by @filial_crypto.
Thu Jul 23 22:11:41 +0000 2020
Replying to @oscpacey and @tdryja
https://twitter.com/christophera/status/1278396429128486914?s=21 https://twitter.com/ChristopherA/status/1278396429128486914
Thu Jul 23 22:12:30 +0000 2020
@BrianBrooksOCC I’m have been quite concerned for years about questionable digital asset custody practices used by fiduciaries & qualified custodians. To much security by obscurity or worse, security theatre. The #Wyoming regs are best so far. How best commicate issues with #OCC?
Thu Jul 23 22:26:50 +0000 2020
Replying to @mikeinspace
We are very close to this in our public beta wallet. Demo soon.
Thu Jul 23 22:46:11 +0000 2020
Replying to @mikeinspace and @CarstenBKK
So we have a full multiaccount, multisig wallet for iOS, but also includes watch-only for any account. How much is that worth to you in an App Store? $1.99 certainly won’t cover it.
Thu Jul 23 22:49:42 +0000 2020
I have great sympathy for both sides of the problem that @hackerfactor brings up in this post about the @torproject. He is correct these should be fixed, but doesn’t understand their financial limitations. He wants to report bugs but not fix. They don’t have $ to fix. 🤷🏻♂️ https://twitter.com/hackerfactor/status/1286316046618488832
Fri Jul 24 00:01:46 +0000 2020
Thus the problem really are the costs and incentives to sustain and support security software. @hackerfactor can’t afford the costs to participate in their secure development practices, and the little money that @torproject receives has to be carefully managed & prioritized.
Fri Jul 24 00:04:11 +0000 2020
I’m in the same boat with my leadership in @BlockchainComns. You can’t tell volunteers what to do, and you have very limited funds for professional secure software development so you have to prioritize. Thus there holes between that are hard to fill. We are seeking to solve this.
Fri Jul 24 00:06:47 +0000 2020
RT @gojomo: news fr 2023: “Psychiatrist-General touts national negative emotional contagion down 50%, since intro of social-networking circ…
Fri Jul 24 00:07:21 +0000 2020
RT @gojomo: “Experimental evidence of massive-scale emotional contagion through social networks [2014]”
https://www.pnas.org/content/111/24/8788
Fri Jul 24 00:07:38 +0000 2020
Replying to @hackerfactor and @torproject
I don’t know what their expenses or priorities, but I know that even if @BlockchainComns was funded to that level, you have to pay top level security engineers, and in general third-party reviews, infrastructure, etc. isn’t cheap either. …
Fri Jul 24 03:14:48 +0000 2020
Replying to @hackerfactor, @torproject and @BlockchainComns
Remember, you said in your blog that you didn’t have time to learn how to be part of the community to be able to contribute the fix yourself. Community costs management time and resources too. And I find I am peter-principled keeping money flowing too, so some costs there.
Fri Jul 24 03:16:13 +0000 2020
Replying to @hackerfactor, @torproject and @BlockchainComns
There is also a matter of priorities — who knows if there is some other project in the works that totally replaces that code? Again, I have no idea of the internals, and yes, $3-$4M a year would be a great budget to have, but don’t call it easy. …
Fri Jul 24 03:17:33 +0000 2020
Replying to @hackerfactor, @torproject and @BlockchainComns
To your side of the equation I think their response has been far too long, and as an active user and supporter of Tor I need them to be more secure. And as the co-author of SSL/TLS, things like Heartbleed (also a money problem) worry me.
Fri Jul 24 03:19:21 +0000 2020
Replying to @hackerfactor, @torproject and @BlockchainComns
Worse, Tor just lost their best revenue sources, the OTF. This doesn’t excuse long delays to fix old vulnerability reports, but it does mean that they are probably devoting as much time to new issues as they should be.
Fri Jul 24 03:22:04 +0000 2020
Replying to @hackerfactor, @torproject and @BlockchainComns
So again, I have sympathy for both sides of the problem, and deep concern about underfunding of security infrastruture in general.
Fri Jul 24 03:24:44 +0000 2020
Replying to @hackerfactor, @torproject and @BlockchainComns
My TLS secures trillions of $ in commerce, but Heartbleed still happened because of insufficient funding. A blip increase in funding happened for a while after that attack, but I feel that support is falling and is still is underfunded. So we have system problems too.
Fri Jul 24 03:25:30 +0000 2020
Replying to @hackerfactor, @torproject and @BlockchainComns
Part of why I founded @BlockchainComns is to look deeper at the root of these problems while we also practice what we preach and deliver on our advocacy. No easy answers, but we are understanding the problem better. (fini)
Fri Jul 24 03:27:10 +0000 2020
RT @latonero: Concerned about Covid-19 immunity passports/digital health certificates? Read two important reports released this week by @p…
Sat Jul 25 17:46:42 +0000 2020
RT @Rainmaker1973: Henry Segerman designed these borromean hairpins with Saul Schleimer: this is another solution to the problem of designi…
Sat Jul 25 18:10:15 +0000 2020
For those of you who are fans of my book on cooperative game design @MeeplesTogether, you will like this series of articles on games, play & joy. As my co-author @Appelcline & I work on our next book on patterns of cooperative plans, there are some good ideas to mine from here. https://twitter.com/JFriedhoff/status/1285999079810531330
Sat Jul 25 18:29:40 +0000 2020
I’m finding the storygaming subgenre of #TTRPG challenging in times of Covid. There are virtual platforms for d&d battles and other stuff, whereas what I want is more like shared index cards on a shared virtual desktop. Google Docs not cutting it. Anyone found a good solution?
Sun Jul 26 22:43:10 +0000 2020
Replying to @adamcjonas
If it aligns with the mission of @BlockchainComns like the docs #SmartCustody book or “Learning Bitcoin from the Command Line” course, we should talk. Our limitation is more funding than writing.
Sun Jul 26 22:52:26 +0000 2020
Replying to @djkinkle
I think the last time I looked at Notion was it wasn’t very simultaneous. One of the reasons that Google Docs won over Wikis was in syncrous sessions & calls there wasn’t the “Now Jon, save your changes. Ok, now everyone refresh. Ooops, Sharon, your changes were lost, start over”
Sun Jul 26 23:08:45 +0000 2020
Replying to @djkinkle
I’d love to have interface like CardFlow, but simultaneous editing inside each card like Google Docs or HackMD. https://www.qrayon.com/home/Cardflow/
Sun Jul 26 23:12:48 +0000 2020
Replying to @La__Cuen and @nktgill
One of my favorites is Thalia, who is both a Grace of Festivities & Banquets, but also the Muse of Comedy & Idyllic Poetry. She must have been very good to get both jobs. Maybe she is one of your patron goddesses?
Mon Jul 27 06:11:15 +0000 2020
I will be reporting out this afternoon as a contributor to a number of #Wyoming “Select Committee on Blockchain, Financial Technology and Digital Innovation Technology” WGs on Digital Identity, DAOs & KYC. @CaitlinLong_ is a Commitee member. LiveStream at https://www.youtube.com/channel/UCZNA0zn1VU1ATv3XugYmFGw
Mon Jul 27 18:55:10 +0000 2020
The specific livestream for this afternoon’s topics (Digital Identity & KYC first, then DAOs) is https://youtu.be/ASWzQoLqvWg — we just finished identity, and we are now on to the topic of DAOs & LAOs, where I am also presenting.
Mon Jul 27 21:02:04 +0000 2020
RT @ChristopherA: The specific livestream for this afternoon’s topics (Digital Identity & KYC first, then DAOs) is https://youtu.be/ASWzQoLqvWg…
Mon Jul 27 21:02:12 +0000 2020
RT @CaitlinLong_: Fascinating debate happening NOW about #DAOs. Questions=why does a business need a lawyer to get started? Do DAOs wor…
Mon Jul 27 22:57:48 +0000 2020
RT @JaredSOlsen: Paving new ground in the Cowboy State. Our new world is more digital than ever. How we think about legal and incorporated…
Tue Jul 28 00:53:31 +0000 2020
Accessing full-node Bitcoin #BTC services through a remote app like a mobile wallet has been an intractable problem, which is why Blockchain Commons is introducing GordianWallet for iOS. It cuts through the difficulties! https://github.com/BlockchainCommons/GordianWallet-iOS 1/9
Tue Jul 28 17:11:38 +0000 2020
.@GordianWallet for iOS has been in development by Peter Denton @Fonta1n3 and @BlockchainComns under its former names as Fully Noded 2 and Bitcoin Standup. But, as we move toward open beta on mainnet Bitcoin, we’re changing its name to represent its part in the GordianSystem. 2/9
Tue Jul 28 17:11:39 +0000 2020
The GordianSystem is a family of services that together provide a private, secure, and cutting-edge experience for accessing your digital assets. It also include https://github.com/BlockchainCommons/GordianNode-macOS, which offers full-node services such as Bitcoin, Lightning, and Tor. 3/9
Tue Jul 28 17:11:40 +0000 2020
We believe that GordianWallet’s simple method of accessing full-node services slices right through a number of long-standing problem in Bitcoin development. 4/9
Tue Jul 28 17:11:42 +0000 2020
But we also believe that our GordianSystem services are Guardians, protecting your digital assets and keys using technology that’s entirely state of the art. https://github.com/BlockchainCommons/GordianSystem 5/9.
Tue Jul 28 17:11:43 +0000 2020
We hope to similarly make the problems of blockchain infrastructure go away, with our “not for profit” open source and open development work. The GordianSystem is just one such project. 7/9.
Tue Jul 28 17:11:46 +0000 2020
Blockchain Commons is all about solving the knotty problems in blockchain infrastructure that are holding back our joint development. That’s why we have the Borromean Rings in our logo. One twist of the magician’s hands, and they’re split apart. 6/9
Tue Jul 28 17:11:46 +0000 2020
Take a look at all of our other projects at our GitHub repo. https://github.com/BlockchainCommons, including our popular “Learning Bitcoin from the Command Line” course, our #SmartCustody book, #LetheKit, our open source DIY hardware box offline cryptography, and more! 8/9
Tue Jul 28 17:11:47 +0000 2020
And consider financially contributing to our work on the GordianSystem and our broader mission to support open blockchain infrastructure, internet security, the open web, digital civil liberties, and more. Become a monthly Patron at https://github.com/sponsors/BlockchainCommons 9/9
Tue Jul 28 17:11:48 +0000 2020
RT @exiledsurfer: Thread; consider supporting their work with a donation.
Tue Jul 28 17:48:41 +0000 2020
RT @zeynep: A truly must-read story about China and AI by @andersen. Today, tech CEO’s will wraps themselves in the language of freedom an…
Wed Jul 29 18:32:48 +0000 2020
This is a VERY important document, a joint commentary published Monday by the Human Rights Commitee of the United Nations offering more commentary & details on the “Right of Peaceful Assembly” from the UN “Universal Declaration of Human Rights”. https://tbinternet.ohchr.org/Treaties/CCPR/Shared%20Documents/1_Global/CCPR_C_GC_37_9233_E.docx
Wed Jul 29 18:50:05 +0000 2020
“States parties should not rely on a vague definition of “public order” to justify over-broad restrictions on the right of peaceful assembly. Peaceful assemblies can in some cases be inherently or deliberately disruptive and require a significant degree of toleration.”
Wed Jul 29 18:55:07 +0000 2020
“…“Public order” and “law and order” are not synonyms, and the prohibition of “public disorder” in domestic law should not be used unduly to restrict peaceful assemblies.”
Wed Jul 29 18:55:29 +0000 2020
“The mere fact that a particular assembly takes place in public does not mean that participants’ privacy cannot be violated. The right to privacy may be infringed, for example, by facial recognition and other technologies that can identify individual participants in a crowd…”
Wed Jul 29 18:57:55 +0000 2020
“… The same applies to the monitoring of social media to glean information about participation in peaceful assemblies.”
Wed Jul 29 18:58:28 +0000 2020
“Only the minimum force necessary may be used where this is required for a legitimate law enforcement purpose during an assembly. Once the need for any use of force has passed, such as when a violent individual is safely apprehended, no further resort to force is permissible.”
Wed Jul 29 19:00:11 +0000 2020
“Many associated activities happen online or otherwise rely upon digital services. Such activities are also protected under article 21. States parties must not, for example, block or hinder Internet connectivity in relation to peaceful assemblies.”
Wed Jul 29 19:01:25 +0000 2020
This document was several years in the making, and joins a similar document published in 2011 on “Freedom of Opinion and Expression” http://docstore.ohchr.org/SelfServices/FilesHandler.ashx?enc=6QkG1d%2fPPRiCAqhKb7yhsrdB0H1l5979OVGGB%2bWPAXiks7ivEzdmLQdosDnCG8FaJ7cpkH%2fR9YlpwV%2bAPs%2bmcH8jGnAN0wEPkLj1E63E3zdVfMFh0MJrIFe0tA7QZm4a
Wed Jul 29 19:06:15 +0000 2020
Complete details on this official commentary on the Article 21 “Right of Peaceful Assembly” can be found at https://www.ohchr.org/EN/HRBodies/CCPR/Pages/GCArticle21.aspx
Wed Jul 29 19:08:53 +0000 2020
RT @cvoule: By focusing extensively on the intersection of digital technologies and the right to peaceful assembly, General Comment 37 sets…
Wed Jul 29 19:09:56 +0000 2020
RT @coincenter: The Constitution Protects Software Developers and Users from Surveillance Overreach https://www.coincenter.org/the-constitution-protects-software-developers-and-users-from-surveillance-overreach/
Wed Jul 29 19:12:50 +0000 2020
We talked in #SmartCustody that one of the protections against a number of adversaries is to not let people know you have digital assets. Yet we also say that you need to buy hardware directly from the manufacturer to protect against evil-maid attack. Vendors should delete data. https://twitter.com/Ledger/status/1288452973811703810
Wed Jul 29 19:35:35 +0000 2020
RT @aantonop: @ChristopherA Always use a fake name, disposable email and PO Box address for this type of purchase. The risk of phishing att…
Wed Jul 29 19:40:46 +0000 2020
Time to start retiring older Tor & start using Tor v3. @GordianWallet for iOS & its companion GordianNode for macOS already use Tor v3 to secure the connection between your mobile phone and your personal full node. More details from @torproject: https://blog.torproject.org/v2-deprecation-timeline
Wed Jul 29 20:34:26 +0000 2020
We also have a new chapter in our “Learning Bitcoin from the Command Line” course on the topic of understanding and installing Tor v3 for use in Bitcoin: https://github.com/BlockchainCommons/Learning-Bitcoin-from-the-Command-Line/blob/master/14_0_Using_Tor.md
Wed Jul 29 20:36:50 +0000 2020
RT @ChristopherA: We also have a new chapter in our “Learning Bitcoin from the Command Line” course on the topic of understanding and insta…
Wed Jul 29 20:36:58 +0000 2020
Replying to @matt_odell, @MrKukks, @lukechilds, @evankaloudis, @DennisReimann and @Esky33junglist
Blockchain Commons https://GitHub.com/sponsors/BlockchainCommons
Thu Jul 30 00:41:56 +0000 2020
Replying to @matt_odell, @MrKukks, @lukechilds, @evankaloudis, @DennisReimann and @Esky33junglist
Christopher Allen https://GitHub.com/sponsors/ChristopherA
Thu Jul 30 00:42:30 +0000 2020
A challenges in cryptographic UX is that there are times when you need to compare two different hash fingerprints. Do you read the first 4 characters of both to see they are the same? First & last 4 characters? Compare every character? Announcing LifeHash https://github.com/BlockchainCommons/LifeHash
Thu Jul 30 18:50:22 +0000 2020
LifeHash is a method of hash visualization based on Conway’s Game of Life that creates beautiful icons that are deterministic, yet distinct and unique given the input data. Video explainer: https://www.youtube.com/watch?v=cu0K__KLxKo
Thu Jul 30 18:50:23 +0000 2020
You can see an example of how we use LifeHash in the UX of our demo research on airgap animated QRs. With LifeHash it is easy to see that the large text transmitted is exactly the same on both devices by looking at its hash fingerprint and its LifeHash https://www.youtube.com/watch?v=t-GGZ9FyuT8
Thu Jul 30 18:50:24 +0000 2020
We are adding LifeHash in our apps from @BlockchainComns where we ask a user to compare two different items & confirm they are the same. We will still present the full cryptographic hash for inspection, but the combination of both LifeHash & a cryptographic fingerprint is easier.
Thu Jul 30 18:50:24 +0000 2020
The basic concept of LifeHash to take a SHA256 hash of the input data (which can be any data including another hash) and then use the 256-bit digest as a 16x16 pixel “seed” for running the cellular automata known as Conway’s Game of Life: https://en.wikipedia.org/wiki/Conway’s_Game_of_Life
Thu Jul 30 18:50:25 +0000 2020
After the pattern becomes stable (or begins repeating) the resulting history is used to compile a grayscale image of all the states from the first to last generation.
Thu Jul 30 18:50:26 +0000 2020
Some bits of the initial hash are then used to apply symmetry and color to the icon to add beauty & quick recognizability.
Thu Jul 30 18:50:27 +0000 2020
We’ve been using LifeHash internally at @BlockchainComns for over a year, and hope that others will add it to their apps. To support this, we are offering it as open source repository along with initial reference implementations in Swift & Mathematica: https://github.com/BlockchainCommons/LifeHash
Thu Jul 30 18:50:29 +0000 2020
There is a long history & academic research about the UX of visual fingerprints that go back all the way to PGP days. There are still many open questions about relying too greatly on visual hashes. So we suggest that a LifeHash should be used only supplement a text fingerprint.
Thu Jul 30 18:50:29 +0000 2020
Using Game of Life provides visual structure to the resulting image, even though it was seeded with entropy. The finished visual hash, given the same input, should appear the same on every platform. For instances, here are hashes of 0-29 using iOS and Mathematica:
Thu Jul 30 18:50:29 +0000 2020
We would love to see more implementations of LifeHash in various languages, in particular Python, Rust and C/C++. We welcome your contribution of thoughts, issues and PRs to our repo. You can financially support more research & open source like this via https://github.com/sponsors/BlockchainCommons
Thu Jul 30 19:06:04 +0000 2020
This doesn’t just apply to teaching, but also employees & community: “I’m hoping to awaken my fellow educators — of all levels — to the fact that if a student is struggling, they probably aren’t choosing to.”—@drdevonprice https://humanparts.medium.com/laziness-does-not-exist-3af27e312d01
Thu Jul 30 20:19:38 +0000 2020
RT @__agwa: Every time there is another JWS/JWT vulnerability involving “alg”:”none” (like today, lolsob), people focus on the “none” part.…
Thu Jul 30 23:23:25 +0000 2020
Very cool. We should figure out how to incorporate this in #LetheKit and with seedtool-cli. I’ve also been talking with our researcher @WolfMcnally about an app to teach LC4, 138bit symmetric encryptions, using paper & 36 or 49 tiles or cards: https://eprint.iacr.org/2017/339.pdf cc @ksedgwic https://twitter.com/bjdweck/status/1288989286369460224
Fri Jul 31 02:58:09 +0000 2020
Replying to @bjdweck
We are also working on some standards for QR code exchange of seeds & Shamir shards between LetheKit, seedtool-cli, @ksedgwic GordianWallet and a few other wallet companies, both software & hardware. Would love your contributions.
Fri Jul 31 03:03:32 +0000 2020
Replying to @kallewoof, @DocHex and @COLDCARDwallet
We are very interested in supporting BIP322 signing at @BlockchainComns for a variety of purposes, including support of signing of messages based on off-chain transactions. This was something that Greg Maxwell wanted someday to replace GPG signing. #SmartSignatures
Fri Jul 31 03:09:24 +0000 2020
RT @ChristopherA: @kallewoof @DocHex @COLDCARDwallet We are very interested in supporting BIP322 signing at @BlockchainComns for a variety…
Fri Jul 31 03:09:29 +0000 2020
Replying to @bjdweck and @ksedgwic
We have diverted/forked from slip-39 support for a variety of reasons. Instead, you will use offline tools like #LetheKit to restore shards to BIP39 or derive an xprv so that at no point a master seed is ever on a networked device.
Fri Jul 31 19:26:01 +0000 2020
Replying to @bjdweck and @ksedgwic
I highly recommend that you look at our libraries. https://github.com/BlockchainCommons/bc-shamir is the core Shamir cryptographic functionality.
Fri Jul 31 19:28:10 +0000 2020
Replying to @bjdweck and @ksedgwic
We are removing SLIP-39 support and will be moving all of our apps to this proposal: https://github.com/BlockchainCommons/Research/blob/master/papers/bcr-2020-011-sskr.md
Fri Jul 31 19:29:42 +0000 2020
RT @SpotBit: Spotbit is a portable crypto exchange API that runs over Tor. That means you can access market data over a tor endpoint at any…
Sat Aug 01 05:20:03 +0000 2020
The newest project from @BlockchainComns is @SpotBit. Our first “customers” will be self-sovereign users of our @GordianWallet to ensure that they don’t have to connect directly to an exchange API but can choose instead to get prices via Tor. In late alpha https://github.com/BlockchainCommons/spotbit https://twitter.com/SpotBit/status/1289386293495918592
Sat Aug 01 05:27:06 +0000 2020
https://twitter.com/spotbit/status/1289387227546411009?s=21 https://twitter.com/SpotBit/status/1289387227546411009